[ad_1]

Uber suffered a cyberattack on Thursday afternoon with a hacker gaining access to vulnerability reports and sharing screenshots of the company’s internal systems, email dashboard and Slack server.
Screenshots shared by the hacker and seen by BleepingComputer show what appears to be full access to many of Uber’s critical computer systems, including company security software and the Windows domain.
Other systems accessed by the hacker include the company’s Amazon Web Services console, VMware ESXi virtual machines, Google Workspace email administration dashboard, and Slack server, where the hacker posted messages.
Uber has since confirmed the attack, tweeting that they are in contact with law enforcement and will release additional information as it becomes available.
“We are currently responding to a cybersecurity incident. We are in contact with law enforcement and will post additional updates here as they become available,” tweeted the Uber Communications account.
The New York Times, which reported for the first time about the breach, said he spoke to the threat actor, who said he breached Uber after performing a social engineering attack on an employee and stealing his password.
The threat actor then gained access to the company’s internal systems using the stolen credentials.
Social engineering has become a very popular tactic in recent attacks against well-known companies, including Twitter, MailChimp, Robin Hoodand Okta.
HackerOne Vulnerability Reports Exposed
While it’s possible the threat actor stole data and source code from Uber during this attack, he also gained access to what could be an even more valuable asset.
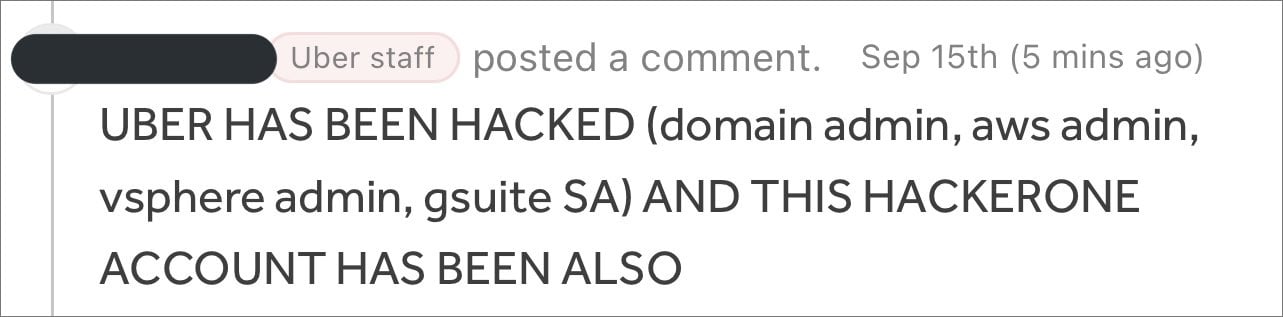
According to Yuga Labs security engineer Sam Currythe hacker also gained access to the company’s HackerOne bug bounty program, where he commented on all of the company’s bug bounty tickets.
Source: curry
Curry told BleepingComputer he learned of the breach after the attacker left the above comment on a vulnerability report he submitted to Uber two years ago.
Uber runs a HackerOne bug bounty program which allows security researchers to privately disclose vulnerabilities in their systems and applications in exchange for a monetary bug bounty. These vulnerability reports are meant to remain confidential until a patch can be released to prevent attackers from exploiting them in attacks.
Curry further shared that an employee of Uber said the threat actor had access to all of the company’s private vulnerability submissions on HackerOne.
BleepingComputer was also told by a source that the attacker downloaded all vulnerability reports before losing access to Uber’s bug bounty program. This likely includes vulnerability reports that have not been patched, presenting a serious security risk to Uber.
HackerOne has since disabled the Uber Bug Bounty program, cutting off access to the disclosed vulnerabilities.
However, it would not be surprising if the threat actor has already downloaded the vulnerability reports and is likely selling them to other threat actors to quickly cash in on the attack.
BleepingComputer has contacted Uber with further questions about the attack, but has not heard back at this time.
[ad_2]
Source link
