[ad_1]

Hackers injected malware into several extensions of FishPig, a Magento-WordPress integrations provider that has over 200,000 downloads.
Magento is a popular open-source e-commerce platform used for building e-stores, supporting the sale of tens of billions of dollars worth of goods per year.
The intruders took over FishPig’s server infrastructure and added malicious code to the vendor’s software to access websites using the products, in what is described as a supply chain attack.
Security Researchers at Sanseca company providing malware and vulnerability detection services for e-commerce, confirmed the compromise of “FishPig Magento Security Suite” and “FishPig WordPress Multisite”.
They say other paid extensions from the provider are also likely compromised. The free extensions hosted on GitHub look clean though.
Malware
Hackers injected malicious code into License.php, a file that validates licenses in premium FishPig plugins, which downloads a Linux binary (“lic.bin”) from FishPig’s servers (“license.fishpig.co. uk”).
The binary is Rekoobe, a Remote Access Trojan (RAT) that has been seen in the past dropped by the ‘Syslog‘ The Linux rootkit.
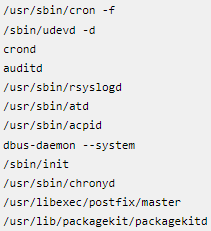
When launched from memory, Rekoobe loads its configuration, deletes all malicious files, and assumes the name of a system service to make it harder to find.
(Sancec)
Eventually, Rekoobe sits idle and waits for commands from a Latvia-based command-and-control (C2) server that Sans researchers located at 46.183.217.2.
Sansec has seen no ongoing action, suggesting that the threat actors behind the breach were likely planning to sell access to compromised e-commerce stores.
Corrective actions
Merchants who installed or updated FishPig premium software before August 19, 2022 should consider their stores compromised and take the following actions:
- Disable all Fishpig extensions
- Run a server-side malware scanner
- Restart the server to end any unauthorized background processes
- Add “127.0.0.1 license.fishpig.co.uk” to “/etc/hosts” to block outgoing connections
Responding to a request for comment from BleepingComputer, FishPig said they were investigating the impact of the intrusion. The company released a security consulting recommending an upgrade of all FishPig modules.
Additionally, a FishPig spokesperson shared the following with BleepingComputer:
The best advice for people at the minute is to reinstall all FishPig modules. They don’t need to update to the latest version (although they can) but just reinstall the same version to ensure they have clean code as any infected code has been removed from FishPig.
The infection was limited to a single file in our obfuscation code on our separate license.fishpig.co.uk and this has been removed and protection added against future attacks. FishPig.co.uk was not affected.
Sorry for any inconvenience people may have encountered. It was an extremely smart and targeted attack and we will be more vigilant in the future.
[ad_2]
Source link
