[ad_1]

The Norwegian National Security Authority (NSM) has confirmed that attackers used a zero-day vulnerability in Ivanti’s Endpoint Manager Mobile (EPMM) solution to breach a software platform used by 12 ministries in the country.
The Norwegian Security and Services Organization (DSS) said Monday that the cyberattack did not affect the Norwegian Prime Minister’s office, the Ministry of Defence, the Ministry of Justice and the Ministry of Foreign Affairs.
The Norwegian Data Protection Authority (DPA) has also been made aware of the incident, stating that hackers could have accessed and/or exfiltrated sensitive data from compromised systems, resulting in a data breach.
“This vulnerability was unique and was first discovered here in Norway. Had we released information about the vulnerability too soon, it could have contributed to its misuse elsewhere in Norway and the rest of the world,” the NSM said. said.
“The update is now generally available and it is prudent to announce what type of vulnerability it is,” said Sofie Nystrøm, director of the National Security Agency.
The Norwegian National Cyber Security Center (NCSC) has also notified all known MobileIron Core customers in Norway of a security update to address this actively exploited zero-day bug (tracked as CVE-2023-35078).
As a recommendation, the NCSC urged those system owners to install security updates to block incoming attacks as soon as possible.
Actively Exploited Authentication Bypass Vulnerability
THE Security Bug CVE-2023-35078 is an authentication bypass vulnerability that affects all supported versions of Ivanti’s (formerly MobileIron Core) Mobile Device Management (EPMM) software, as well as unsupported and end-of-life versions.
Successful exploitation allows remote attackers to access specific API paths without requiring authentication.
“An attacker with access to these API paths could gain access to personally identifiable information (PII) such as names, phone numbers and other mobile device details for users of a vulnerable system,” the US Cybersecurity and Infrastructure Security Agency (CISA) warned in an advisory released Monday.
“An attacker can also make other configuration changes, including creating an EPMM administrative account that can make other changes to a vulnerable system.”
The company confirmed that day zero is being leveraged in attacks and also warned customers that it is essential to “take immediate action to ensure you are fully protected.”
According to Shodan’s Internet Exposure Analytics Platform, more than 2,900 MobileIron user portals are currently exhibited online, including about three dozen are related to US local and state government agencies.
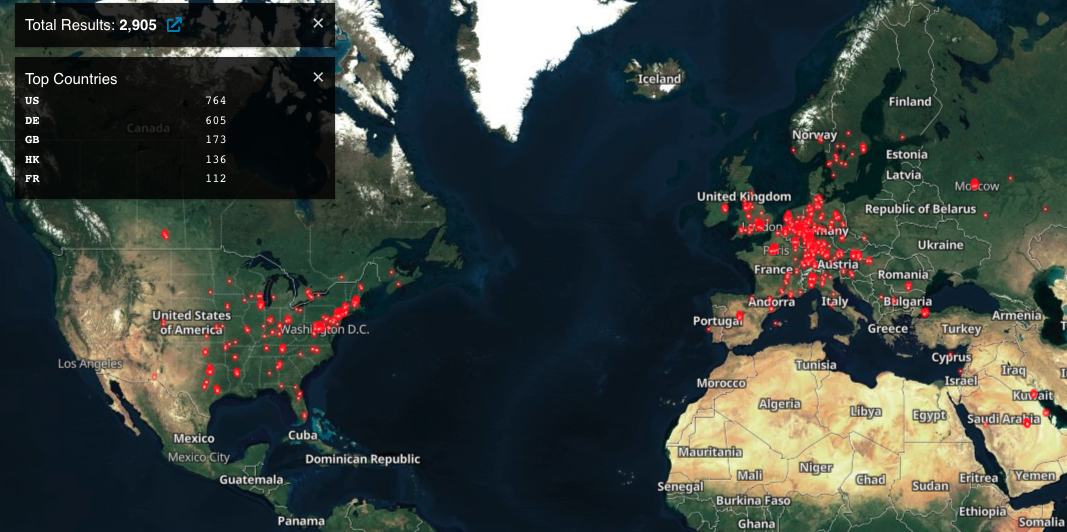
Most of these exposed servers are in the United States, with other notable locations like Germany, the United Kingdom, and Hong Kong.
In this context, it is essential that all network administrators quickly install the latest Ivanti Endpoint Manager Mobile (MobileIron) patches to protect their systems against attacks.
[ad_2]
Source link
