[ad_1]

Security researchers have discovered a previously unknown backdoor they call Dolphin that has been used by North Korean hackers in highly targeted operations for over a year to steal files and send them to storage Google Drive.
According to research from cybersecurity firm ESET, the threat group APT 37 (aka Reaper, Red Eyes, Erebus, ScarCruft) used the newly discovered malware against very specific entities. The group has been associated with espionage activities aligned with North Korean interests since 2012.
Researchers found Doplphin in April 2021 and watched it evolve into new versions with improved code and anti-detection mechanisms.
Beyond BLUELIGHT
Dolphin is used with BLUELIGHT, a basic recognition tool seen in previous APT37 campaignsbut it offers more powerful features such as stealing web browser information (passwords), taking screenshots and logging keystrokes.
BLUELIGHT is used to launch Dolphin’s Python loader on a compromised system but has a limited role in spying operations.
The Python loader includes script and shellcode, initiating multi-step XOR decryption, process creation, etc., ultimately resulting in the execution of the Dolphin payload in a newly created memory process.

(ESET)
Dolphin is a C++ executable using Google Drive as a command and control (C2) server and to store stolen files. The malware establishes persistence by modifying the Windows registry.
Dolphin Abilities
During the initial phase, Dolphin collects the following information from the infected machine:
- username
- computer name
- Local and external IP address
- Security software installed
- RAM size and usage
- Presence of debugging or network packet inspection tools
- Operating system version
The backdoor also sends the C2 its current configuration, version number, and time.
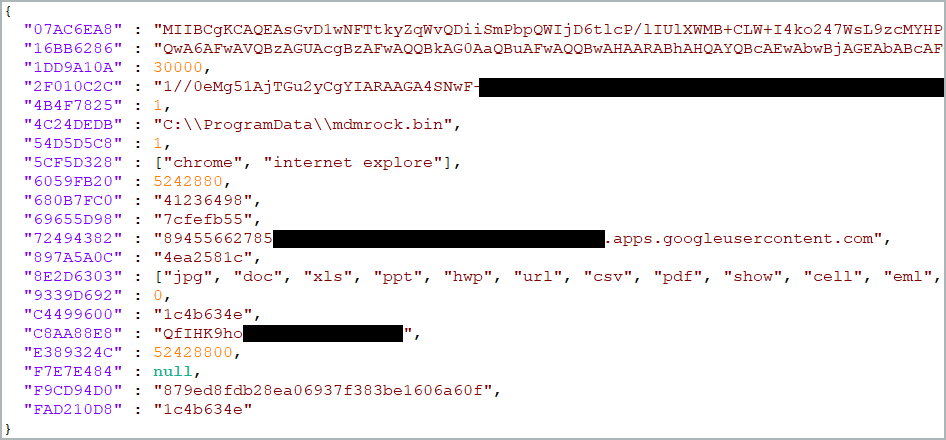
The configuration contains keylogging and file exfiltration instructions, credentials for Google Drive API access, and encryption keys.
The say the researchers that the hackers delivered their orders to Dolphin by uploading them to Google Drive. In response, the backdoor downloads the result of the command execution.
The malware has an extended feature set which includes scanning local and removable drives for different types of data (media, documents, emails, certificates) which are archived and delivered to Google Drive. This feature has been further enhanced to filter data by extension.
Steal files from a connected phone
Its search capabilities extend to any phone connected to the compromised host using the Windows Portable Device API.
ESET notes that this feature appeared to be in development in the first version of the malware they found. The supporting evidence was as follows:
- using a hard-coded path with a username that probably does not exist on the victim’s computer
- missing variable initialization – some variables are assumed to be initialized to zero or dereferenced as pointers without initialization
- filter missing extensions
Moreover, it can also reduce the security of a victim’s Google account by modifying related settings. This could allow attackers to retain access to the victim’s account for longer
Dolphin can log user keystrokes in Google Chrome by abusing the “GetAsyncKeyState” API and it can take a snapshot of the active window every 30 seconds.
ESET researchers discovered four separate versions of the Dolphin backdoor, the latest being 3.0 from January 2022.
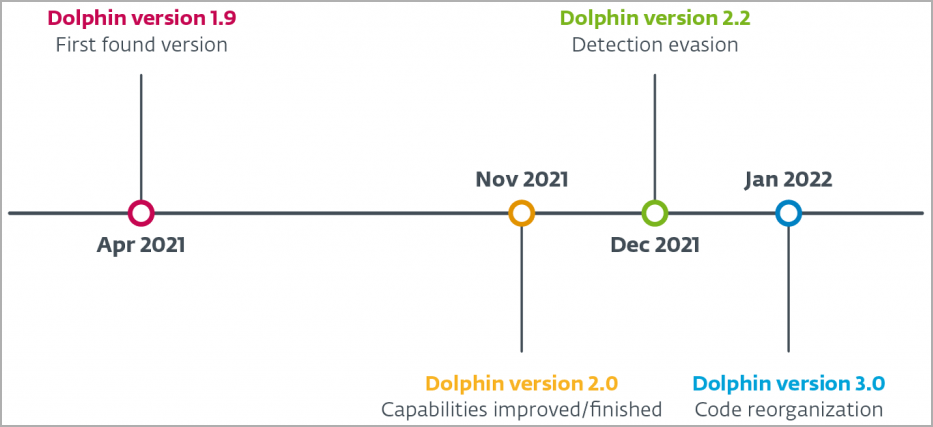
It is possible that new versions of Dolphin exist and have been used in attacks, given that the backdoor was deployed against selected targets.
According to the researchers, the malware was used in a watering hole attack on a South Korean newspaper reporting on North Korea-related activities and events. Hackers relied on an Internet Explorer exploit to ultimately deliver a Dolphin backdoor to target hosts.
ESET report provides a list of hashes for Dolphin backdoor versions 1.9 to 3.0 (86/64 bit).
[ad_2]
Source link
