[ad_1]

Microsoft has shared more information about malicious embedded files that OneNote will soon block to defend users against ongoing malware-pushing phishing attacks.
The company first revealed that OneNote will get enhanced security in a Microsoft 365 roadmap published three weeks ago, on March 10, following recent And in progress waves of phishing attacks pushing malware.
Hackers have been using OneNote documents in spear phishing campaigns for mid-December 2022 after Microsoft patched a MoTW zero-day bypass exploited to drop malware via ISO and ZIP files and finally Word and Excel macros disabled by default.
Threat authors create malicious Microsoft OneNote documents by embedding dangerous files and scripts and then cloaking them with design elements, as shown below.
File types considered dangerous
Today, the company shared more details about specific file extensions that will be blocked once new OneNote security enhancements are rolled out.
Microsoft says it will align files deemed unsafe and blocked in OneNote with those blocked by Outlook, Word, Excel and PowerPoint.
The full list includes 120 extensions according to this Microsoft 365 support document:
.ade, .adp, .app, .application, .appref-ms, .asp, .aspx, .asx, .bas, .bat, .bgi, .cab, .cer, .chm, .cmd, .cnt, .com, .cpl, .crt, .csh, .der, .diagcab, .exe, .fxp, .gadget, .grp, .hlp, .hpj, .hta, .htc, .inf, .ins, .iso, .isp, .its, .jar, .jnlp, .js, .jse, .ksh, .lnk, .mad, .maf, .mag, .mam, .maq, .mar, .mas, .mat, .mau, .mav, .maw, .mcf, .mda, .mdb, .mde, .mdt, .mdw, .mdz, .msc, .msh, .msh1, .msh2, .mshxml, .msh1xml, .msh2xml, .msi, .msp, .mst, .msu, .ops, .osd, .pcd, .pif, .pl, .plg, .prf, .prg, .printerexport, .ps1, .ps1xml, .ps2, .ps2xml, .psc1, .psc2, .psd1, .psdm1, .pst, .py, .pyc, .pyo, .pyw, .pyz, .pyzw, .reg, .scf, .scr, .sct, .shb, .shs, .theme, .tmp, .url, .vb, .vbe, .vbp, .vbs, .vhd, .vhdx, .vsmacros, .vsw, .webpnp, .website, .ws, .wsc, .wsf, .wsh, .xbap, .xll, .xnkWhereas previously OneNote warned users that opening attachments could damage their data, but still allowed them to open embedded files marked as unsafe, after the security enhancement was rolled out, users no longer will no longer have the choice of opening files with dangerous extensions.
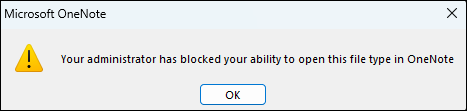
Users will see a warning dialog box when a file is blocked, stating: “Your administrator has blocked your ability to open this type of file in OneNote.”
Microsoft says the change will begin rolling out in Current Channel (Preview) version 2304 to OneNote for Microsoft 365 on Windows devices between late April 2023 and late May 2023.
The security enhancement will also be available in retail versions of Office 2021, Office 2019, and Office 2016 (Current Channel), but not in volume licensed versions of Office, such as Office Standard 2019 or Office LTSC Professional Plus 2021.
However, it will not be available in OneNote on the web, OneNote for Windows 10, OneNote on Mac, or OneNote on Android or iOS devices.
| Update channel | Version | Release date |
| Current channel (preview) | Edition 2304 | First half of April 2023 |
| Current Channel | Edition 2304 | Second half of April 2023 |
| Monthly Business Channel | Edition 2304 | June 13, 2023 |
| Semi-Annual Enterprise Channel (preview) | Release 2308 | September 12, 2023 |
| Semi-Annual Enterprise Channel | Release 2308 | January 9, 2024 |
Management of blocked extensions
To block additional file extensions that you might consider dangerous, enable the “Block additional file extensions for OLE embedding” policy under User Configuration\Policies\Administrative Templates\Microsoft Office 2016\Security Settings and select the extensions you want to block.
On the other hand, if you need to allow specific file extensions that will soon be blocked by default, you can enable the “Allow file extensions for OLE integration” policy from the same location in the Policy Management Console group and specify the extensions you want to allow.
You can also use the Cloud Policy service for Microsoft 365 to tailor policies to your preferences. Any changes you make will also affect other applications, including Word, Excel, and PowerPoint.
These policies are only available for Microsoft 365 Apps for enterprise users, as they are not available in Microsoft Apps for Business.
Microsoft Office Group Policies can also be used to restrict the launch of attachments built into OneNote until new security enhancements are rolled out.
[ad_2]
Source link
