[ad_1]

Cryptocurrency wallet provider MetaMask is warning users of a new scam called “Address Poisoning” used to trick users into sending funds to a scammer rather than an intended recipient.
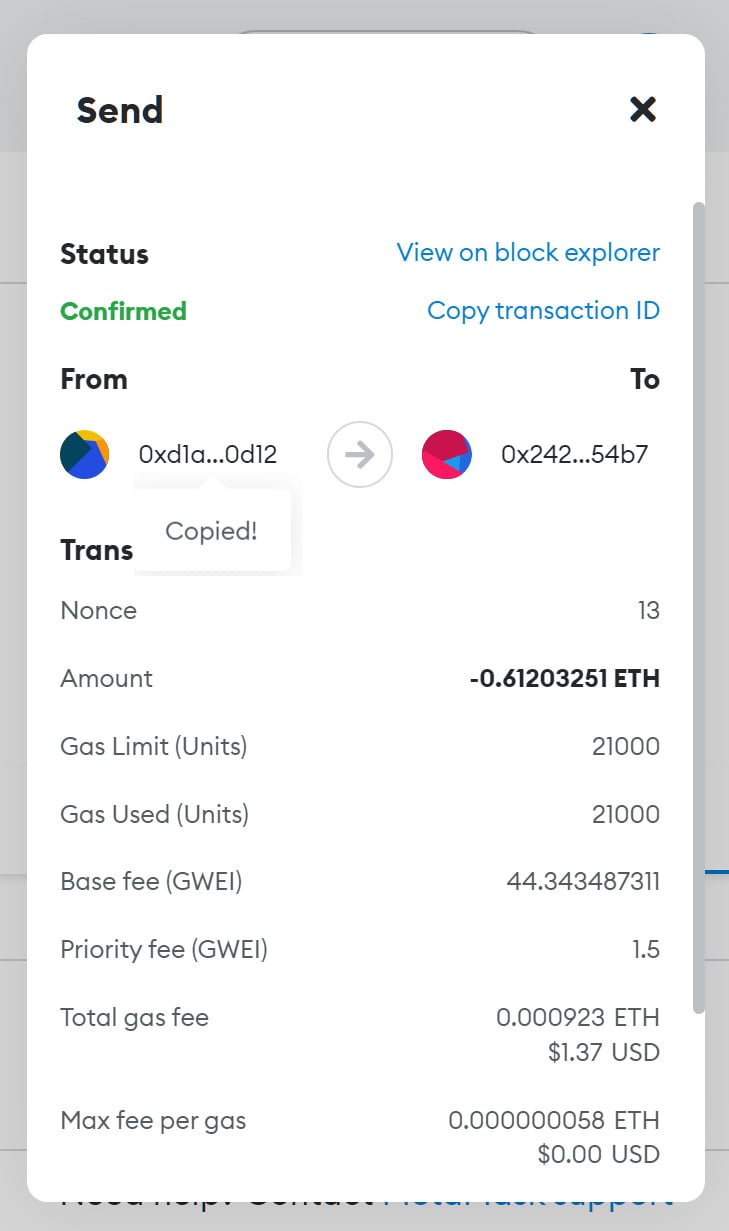
When MetaMask users send or receive cryptocurrency, it appears in the list of wallet transactions. Clicking on the transaction displays more details, including the token, the amount sent or received, and an abbreviated form of the third party’s address.
For example, below are examples of two shortened addresses that could be displayed in MetaMask cryptocurrency transactions.
From: 0x242...54b7
To: 0x242...54b7Although the two wallet addresses appear identical in their abbreviated form, they can be completely different, which easily confuses MetaMask users.
Scammers poison your MetaMask transactions
In a new post from MetaMask, the developers warn of a new scam called “Address Poisoning” which relies on poisoning the wallet’s transaction history with scammer addresses that are very similar to the addresses a user has. recently performed.
The threat actor monitors the blockchain for new transactions to conduct the scam.
After selecting a target, they use a custom address builder to create an address very similar, if not almost exactly the same, as the one involved in the recent transaction.
It should be noted that creating an address that matches the prefix of a target address or suffix can take less than a minute. However, targeting both will take much longer (perhaps too long to be worth it) to generate.
The threat actor then sends the targeted sender’s address a small amount of cryptocurrency, or even a $0 token transaction, from this new address so that the transaction appears in the history of his wallet.
Because the threat actor’s address is very similar to a user’s previous transaction, and MetaMask shortens addresses in transaction history, it appears to be from the same person.
This method effectively poisons the transaction history with multiple entries that appear to be between the same address but use different ones – one address for the real and legitimate transaction and the attacker’s most recent using an impersonated wallet address.
The attacker then hopes that when a user needs to send cryptocurrency to someone they have already sent to, they will find the most recent transaction, which in this case is from the attacker, and send the crypto to the scammer’s address instead.
To perform a transaction, even for negligible amounts, the attacker still has to cover additional costs called “gas”, because the transaction is recorded on the blockchain.
However, threat actors are willing to invest in the scam in hopes of a much bigger payout.
Since there is no way to prevent these malicious transactions from occurring on the blockchain, MetaMask warns users to be diligent when copying addresses from transactions.
Also, since clicking on the short address in MetaMask transactions automatically copies it to the keyboard without displaying the full address, as shown in the mockup below, it’s crucial to be very careful.
Source: BleepingComputer
Instead, search your transaction list for a known valid transaction and retrieve the full address from a blockchain explorer like EtherScan.
MetaMask also recommends that you use their built-in address book feature in “Settings → Contacts” to save known and valid cryptocurrency addresses for people or services you commonly send transactions to.
One possible way for MetaMask to prevent these types of attacks is to create a new option that forces the display of full sender and sender addresses in transaction histories.
However, since Ethereum addresses are very long (66 characters), this would introduce UI design issues.
[ad_2]
Source link
