[ad_1]

Microsoft says Cuba ransomware threat actors are hacking Microsoft Exchange servers without patching against a critical Server-Side Request Forgery (SSRF) vulnerability also exploited in Play ransomware attacks.
Cloud computing provider Rackspace recently confirmed that Play ransomware used a zero-day exploit called OWASSRF targeting this bug (CVE-2022-41080) to compromise unpatched Microsoft Exchange servers on its network after bypassing ProxyNotShell URL Rewrite Mitigation.
According to Microsoft, the Play ransomware gang has been abusing this security flaw since late November 2022. The company advises customers to prioritize CVE-2022-41080 patches to block potential attacks.
Redmond says this SSRF vulnerability has also been exploited since at least Nov. 17 by another threat group it tracks as DEV-0671 to hack into Exchange servers and deploy Cuba ransomware payloads.
Microsoft shared this information in a January update to a private threat analysis report seen by BleepingComputer and available to customers with Microsoft 365 Defender, Microsoft Defender for Endpoint Plan 2, or Microsoft Defender for Business.
While Microsoft released security updates to address this SSRF Exchange vulnerability on November 8 and provided some of its customers with information that ransomware gangs are using the flaw, the board has not yet been updated to warn that it is exploited in the wild.
Patch your Exchange servers against OWASSRF attacks
The OWASSRF exploit spotted by CrowdStrike security researchers on the Rackspaces network has also been shared online along with some of the other malicious Play ransomware tools.
This will make it easier for other cybercriminals to adapt the Play ransomware tools for their own purposes or to create their own custom CVE-2022-41080 exploits, which will add urgency to fixing the vulnerability as soon as possible.
On Tuesday, the Cybersecurity and Infrastructure Security Agency (CISA) also ordered civilian Federal Executive Branch (FCEB) agencies to patch their systems against this bug by January 31 and strongly encouraged all organizations to secure their Exchange servers to thwart exploit attempts.
Organizations with on-premises Microsoft Exchange servers on their networks should immediately deploy the latest Exchange security updates (with November 2022 as the minimum patch level) or disable Outlook Web Access (OWA) until they can apply fixes CVE-2022-41080.
Cuba ransomware behind over 100 attacks worldwide
The FBI and the CISA revealed in a joint security advisory released last month that Cuba’s ransomware gang reaped more than $60 million in ransoms in August 2022 after killing more than 100 people worldwide.
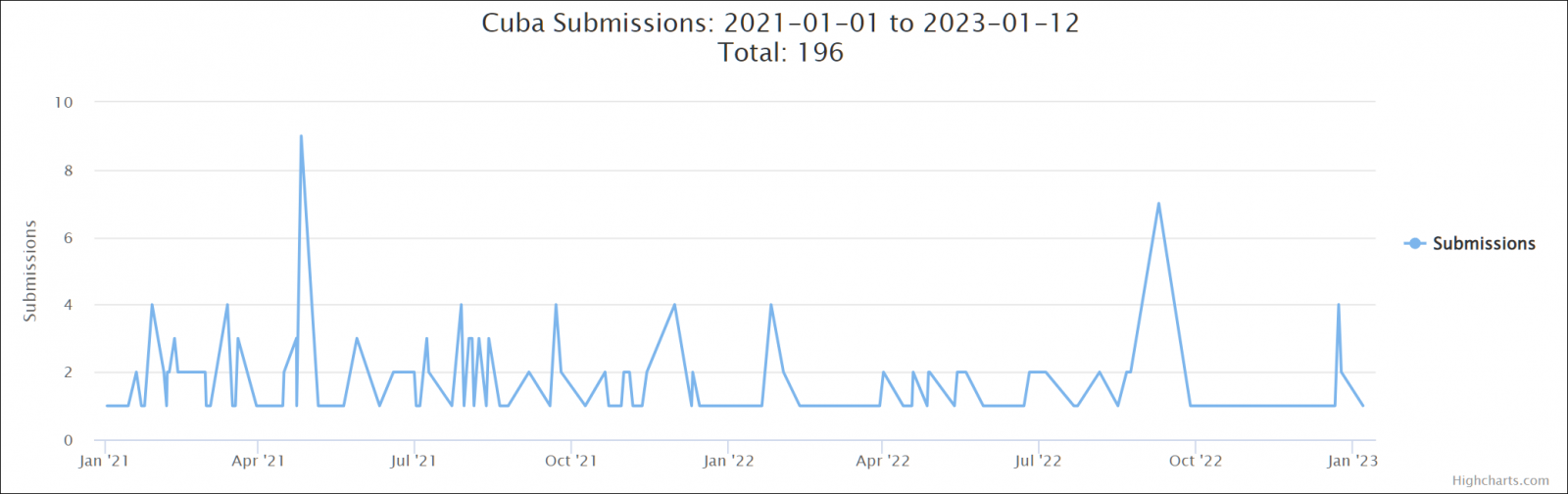
Although this paints a bleak picture, samples submitted by victims for analysis by the ID-Ransomware platform show that the gang is not very active, proving that even a somewhat inactive ransomware operation can have a huge impact. .
Another FBI notice from December 2021 warned that the ransomware group had compromised at least 49 organizations from critical infrastructure sectors in the United States.
In both notices, the FBI urged reporting of ransomware attacks in Cuba to local FBI offices and asked victims to share related information with their local FBI Cyber Squad to help identify members. of the ransomware gang and the cybercriminals they work with.
Although not as prolific as Cuba ransomware and although it was first spotted much more recently, in June 2022, Play ransomware has been quite active and has already claimed dozens of victims in the world, including rack spacethem German hotel chain H-Hotelsthem Belgium city of Antwerpand Argentinian Judiciary of Córdoba.
[ad_2]
Source link
