[ad_1]

A massive brand impersonation campaign targeting over a hundred popular clothing, shoe and apparel brands has been going on since June 2022, tricking people into entering their account credentials and financial information on fake websites.
Brands spoofed by fake sites include Nike, Puma, Asics, Vans, Adidas, Columbia, Superdry Converse, Casio, Timberland, Salomon, Crocs, Sketchers, The North Face, UGG, Guess, Caterpillar, New Balance, Fila, Doc Martens , Reebok, Tommy Hilfiger and others.
According to Bolster’s threat research team, which uncovered the campaign, it relies on at least 3,000 domains and around 6,000 sites, including inactive sites.
Strengthen relationships that the campaign saw a significant spike in activity between January and February 2023, adding 300 new fake sites per month.
Domain names follow a brand name usage pattern with a city or country, followed by a generic TLD such as “.com”.
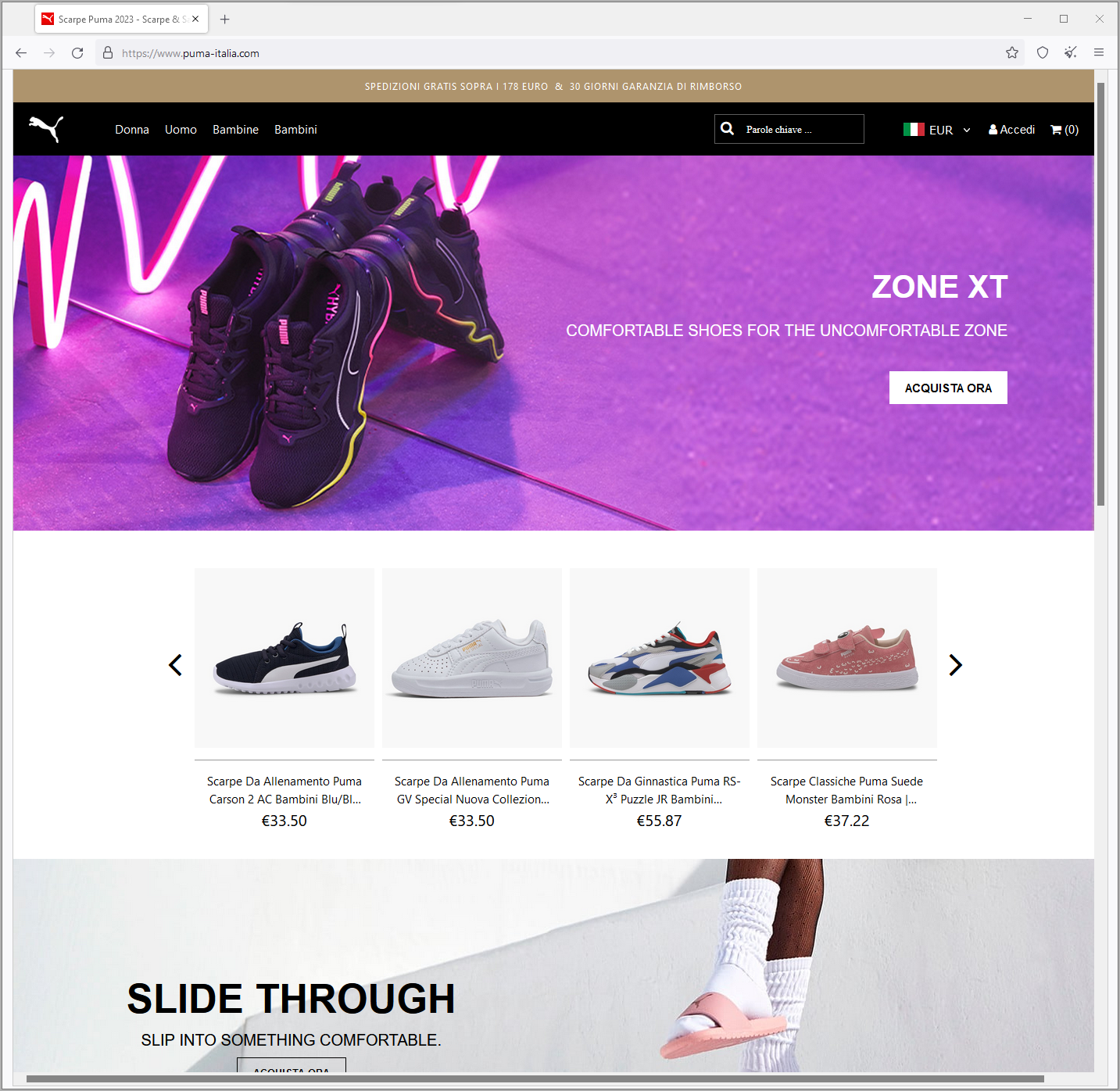
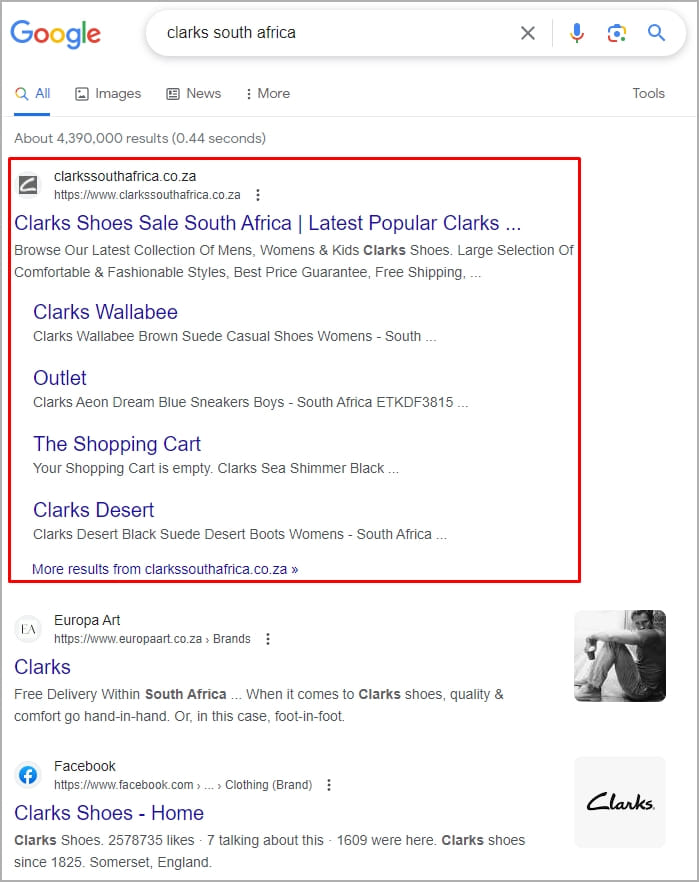
The researchers claim that the campaign exploited more than ten fake websites for Nike, Puma and Clarks, featuring a design very similar to the brands’ official sites.
These fraudulent domains were traced to Autonomous System number AS48950 and were hosted by two internet service providers, Packet Exchange Limited and Global Colocation Limited.
Most are registered through Alibaba.com Singapore, and domain ages range from two years to 90 days.
Domain Aging is a crucial factor in phishing operations because the longer a domain remains active but remains innocuous, the less likely it is to be flagged by security tools as suspicious.
Letting a domain age for at least two years is something that Reported Confident last year, observing the tactic in a global malvertising campaign that has successfully used it since 2018.
In the campaign discovered by Bolstermany malicious domains have gone unreported for so long that Google Search has indexed them and are now likely to rank well for specific search terms.
This is a particularly effective strategy for tricking unsuspecting users into visiting a phishing site, as most people associate high Google search rankings with credibility and trustworthiness.
(Computer Beep)
BleepingComputer has gone through the pages of some of these sites and found that they are not hastily built clones, as they feature realistic “About Us” pages, include contact details, order pages work as expected and are generally difficult to identify as suspicious.
The exact scam strategy followed in this campaign is unknown, but Bolster suggests that the sites never ship products that customers pay for or ship Chinese counterfeits.
Moreover, all details entered on payment pages including credit card details can be stored by website operators and resold to cyber criminals.
When searching for a brand’s official website, ignore any promoted results on Google Search. If you’re still unsure, check the brand’s Wikipedia page or social media channels for the legit URL.
[ad_2]
Source link
