[ad_1]

A hacking group tracked as MirrorFace has been targeting Japanese politicians for weeks before the House of Councilors election in July 2022, using a previously undocumented credential stealer named “MirrorStealer”.
The campaign was discovered by ESETwhose analysts report having been able to gather evidence thanks to the operational errors committed by the hackers who left traces.
The hackers deployed the new information-stealing malware along with the group’s backdoor, LODEINFO, which communicated with a C2 server known to belong to the APT10 infrastructure.
A October 2022 Kaspersky’s report described an extensive deployment of LODEINFO against high-profile Japanese targets and highlighted the constant development needed to improve the custom backdoor.
Spear phishing attacks
Hacking group MirrorFace (APT10 and Cicada) began sending spear phishing emails to their targets on June 29, 2022, posing as PR agents from the recipient’s political party, asking them to release the video files joined on social networks.
.png)
In other cases, threat actors have impersonated a Japanese ministry, attaching decoy documents that extract WinRAR archives in the background.
The archive contained an encrypted copy of the LODEINFO malware, a malicious DLL loader and a harmless application (K7Security Suite) used for DLL search order hijacking.
This is the same stealth attack chain that Kaspersky described in its previous report, which loads the backdoor directly into memory.
MirrorStealer Operations
APT10 used LODEINFO to deploy MirrorStealer (‘31558_n.dll’) to compromised systems.
MirrorStealer targets credentials stored in web browsers and email clients, including “Becky!”, a popular email client in Japan.
This indicates that MirrorStealer could have been developed explicitly for Japan-focused APT10 operations.
All stolen credentials are stored in a txt file in the TEMP directory, then wait for LODEINFO to send them to C2, as MirrorStealer does not support data exfiltration on its own.
LODEINFO is also used as a connection bridge between the C2 and MirrorStealer, to transmit commands to the information thief
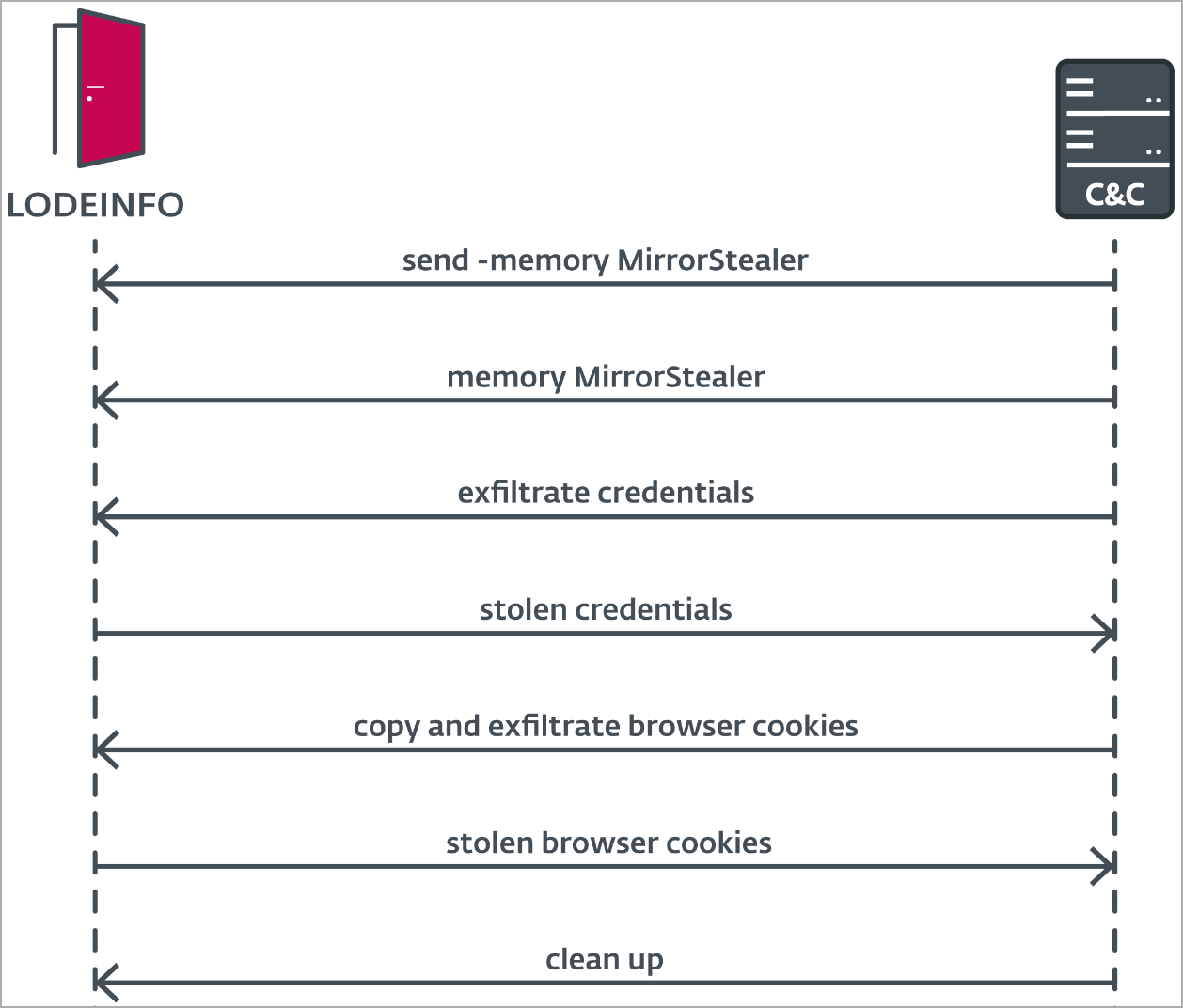
ESET analysts have observed that LODEINFO transmits commands to load MirrorStealer onto the memory of the hacked system, injecting it into a newly generated cmd.exe process and executing it.
Also, there are signs that the remote operator tried to exfiltrate cookies from the browser using MirrorStealer, but reverted to using LODEINFO for this action, because the new infostealer doesn’t take support this function.
Leave traces
APT10 was not very careful in this campaign, not removing all traces of its activity from the hacked computers and leaving behind the MirrorStealer text file containing the collected credentials.
Additionally, ESET analysts noticed that hackers sent commands with typos to LODEINFO in several cases, indicating that the technical aspect of the operation is more manual than expected from an APT group.
[ad_2]
Source link
