[ad_1]

Security analysts have discovered two API security vulnerabilities on BrickLink.com, the LEGO Group’s official used and vintage marketplace for LEGO bricks.
BrickLink is the world’s largest online community of LEGO fans, with over one million registered members.
Two API security issues discovered by Salt Security could have allowed an attacker to take control of members’ accounts, access and steal personally identifiable information (PII) stored on the platform, or access internal production data and compromise internal servers.
API flaw details
Salt Security analysts discovered the vulnerabilities while experimenting with user input fields on the BrickLink website.
The first is a Cross-Site Scripting (XSS) flaw in the “Find Username” dialog of the Coupon Search section, which allowed an attacker to inject and execute code on the machine of the target using a specially crafted link.
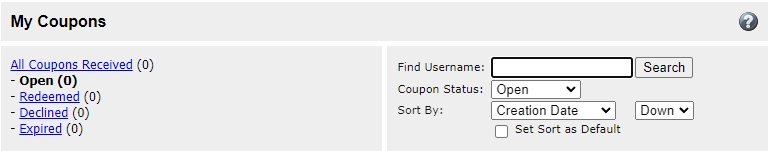
By using the target’s session ID exposed on another page, an attacker could exploit the XSS flaw to hijack the session and gain control of the target’s account.
Accessing the account means exposing all data stored on the platform, including personal details, email address, shipping address, order history, coupons, comments received, searched items and message history.
The second flaw was located on the “Upload to Wanted List” page, where users can upload XML listings containing LEGO parts they wish to find and purchase.
By exploiting a flaw in the endpoint scanning mechanism, Salt Security analysts launched a successful XML External Entity (XXE) injection attack, adding a reference to an external entity to their file.
The XXE attack allowed them to read files on the web server and execute a server-side request forgery (SSRF) attack, which could lead to the exfiltration of AWS EC2 tokens for the server.
Security researchers have reported the discovered vulnerabilities to LEGO, and the company has taken steps to resolve all issues.
Cyber attacks increase during shopping seasons and the retail sector is a more attractive target as the focus is on the commercial side of the business and less on improving security.
Buyers are advised to use strong account credentials and enable two-factor authentication where applicable. When placing orders, a good recommendation is to use guest accounts or virtual/temporary payment cards, if possible.
[ad_2]
Source link
