[ad_1]
Indigo Books & Music, Canada’s largest bookstore chain, was hit by a cyberattack yesterday, forcing the company to make the website unavailable to customers and only accept cash payments.
The exact nature of the incident remains unclear, but Indigo does not rule out that hackers stole customer data.
Cash payments only
On Wednesday, Indigo announced that “technical problems” prevented access to the website and that customers in physical stores could only pay in cash.
Additionally, the company announced that gift card transactions were not possible and there could be delays with online orders.
Hours later, Indigo disclosed that its IT systems were the target of a cyberattack and that it was investigating the incident with the help of third-party experts.
The company did not disclose what type of cybersecurity incident it is currently facing, but said it is trying to determine if the intruders managed to access and/or steal customer data.
As Indigo said it was working to restore systems, another possibility would be a ransomware attack, which usually results in a data breach as hackers steal data and threaten to release it unless the victim pays the ransom.
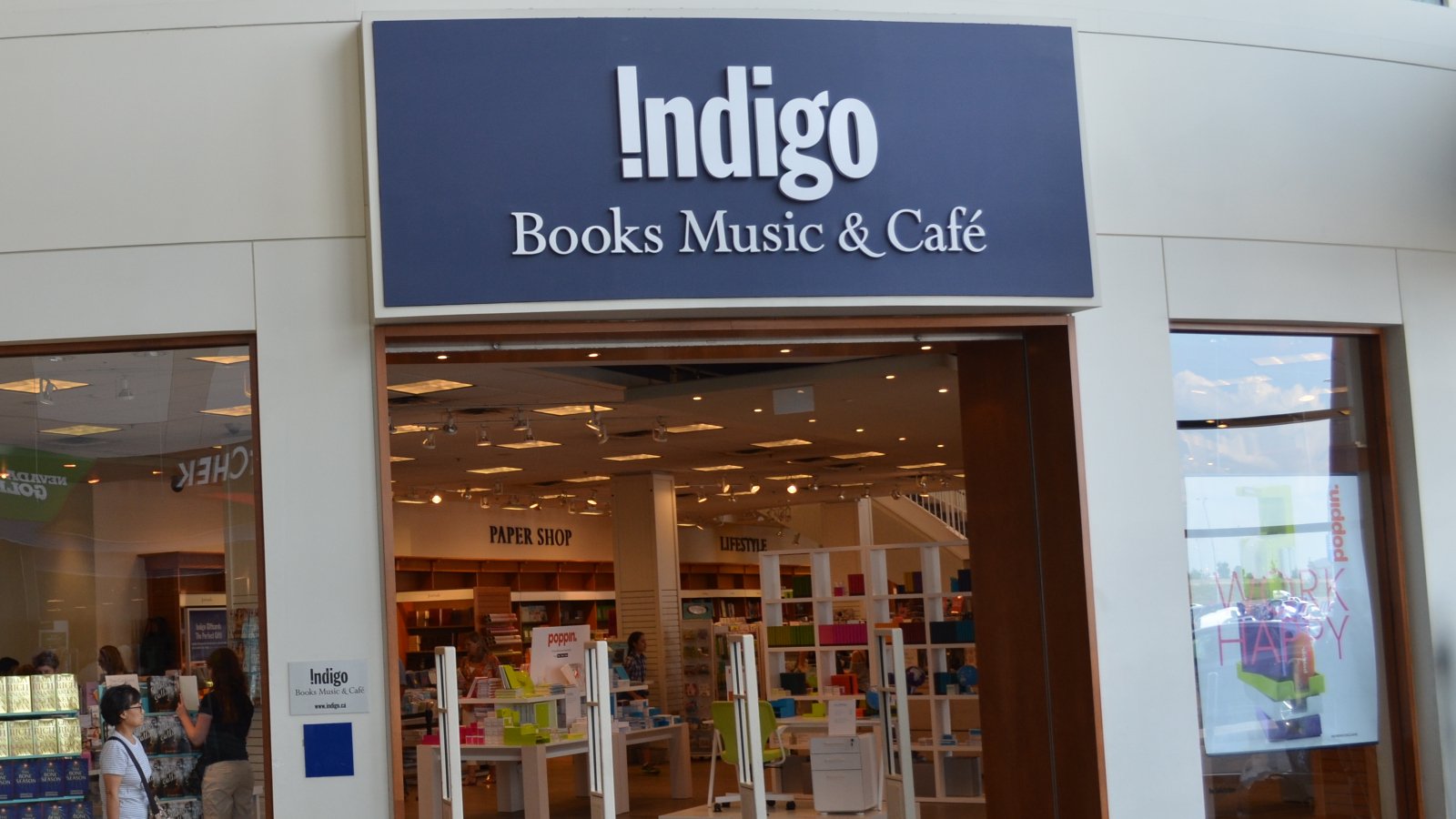
Cybercriminals often target big brands, and with annual revenue of over $1 billion CAD, Indigo fits the bill.
The company’s activities include the sale of books, magazines, toys, beauty and wellness products, and even “everything baby items” and electronics such as smart home devices.
Indigo has thousands of employees, 86 hypermarkets under the Chapters and Indigo banners, and 123 small format stores.
Information Stealing Malware
Although it is still early in the investigation and the company has not released any information on the method used to breach its systems, the hackers may have used data collected by information-stealing malware to access to the Indigo network.
BleepingComputer learned from a threat intelligence company Kela that at least one cybercrime market in February and January was selling Indigo credentials stolen by information-stealing malware, such as Redline, Vidar and Raccoon.
This malware searches for sensitive information about the infected system and also collects details about the machine. All of this serves to create a profile that would allow hackers to access the compromised host without triggering any alarms.
[ad_2]
Source link