[ad_1]
Microsoft has patched a zero-day vulnerability in the Windows Common Log File System (CLFS), actively exploited by cybercriminals to elevate privileges and deploy Nokoyawa ransomware payloads.
Given its continued operation, CISA has also added CVE-2023-28252 Windows zero-day to its catalog of Known exploited vulnerabilities today, directing Federal Civilian Executive Branch (FCEB) agencies to secure their systems against him by May 2.
Tracked as CVE-2023-28252This CLFS A security flaw was discovered by Genwei Jiang of Mandiant and Quan Jin of DBAPPSecurity’s WeBin Lab.
It affects all supported Windows server and client versions and can be exploited by local attackers in low complexity attacks without user interaction.
Successful exploitation allows hackers to gain SYSTEM privileges and fully compromise targeted Windows systems.
Microsoft fixed this zero-day and 96 other security bugs as part of this month’s Patch Tuesdayincluding 45 remote code execution vulnerabilities.
Exploited in ransomware attacks
Security researchers from Kaspersky’s Global Research and Analysis Team (GReAT) also recently discovered that the CVE-2023-28252 flaw was exploited in Nokoyawa ransomware attacks.
“Kaspersky researchers discovered the vulnerability in February following additional verification of a number of attempts to execute similar privilege escalation exploits on Microsoft Windows servers belonging to different small and medium-sized businesses in the regions. Middle East and North America,” the company said in a press release.
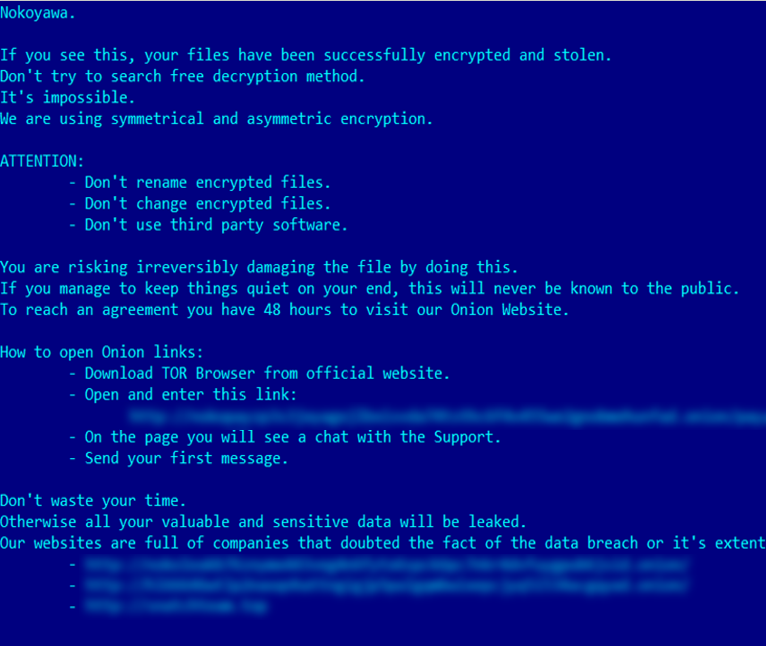
“CVE-2023-28252 was first spotted by Kaspersky in an attack in which cybercriminals attempted to deploy a newer version of Nokoyawa ransomware.”
According to Kaspersky, the Nokoyawa ransomware gang has used other exploits targeting the Common Log File System (CLFS) driver since June 2022, with similar but distinct characteristics, linking them all to a single exploit developer.
The group has used at least five other CLFS exploits to target multiple verticals, including but not limited to retail and wholesale, energy, manufacturing, healthcare, and software development.
Redmond has patched at least 32 local privilege escalation vulnerabilities in the Windows CLFS driver since 2018, three of which (CVE-2022-24521, CVE-2022-37969, and CVE-2023-23376) are also exploited in the wild in as long as zero days, according to Kaspersky.
“Cybercrime groups are becoming increasingly sophisticated in using zero-day exploits in their attacks,” said senior security researcher Boris Larin.
“It used to be primarily an advanced persistent threat actor (APT) tool, but now cybercriminals have the resources to acquire zero-days and use them regularly in attacks.”
Evolution of ransomware
Nokoyawa ransomware surfaced in February 2022 as a strain capable of targeting 64-bit Windows systems in double extortion attacks, where threat actors also steal sensitive files from compromised networks and threaten to leak them online unless a ransom is paid.
Nokoyawa shares the code with JSWormName, KarmaAnd Nemty ransomware, and it was rewritten in Rust from September 2022, moving from the initial version of Nokoyawa ransomware, which was developed using the C programming language.
“The first Nokoyawa variants were just ‘rebranded’ variants of the JSWorm ransomware, which we’ve talked about before,” Larin said in today’s report.
“In this attack, the cybercriminals used a newer version of Nokoyawa which is quite distinct from the JSWorm code base.”
[ad_2]
Source link
