[ad_1]
VMware has released a critical security update to address a critical injection vulnerability that affects several versions of Carbon Black App Control for Windows.
The company warns that the severity rating for the security issue is 9.1 out of 10 and an attacker can take advantage of this to gain access to the underlying operating system.
Carbon Black App Control is a suite designed to help large organizations ensure that their mission-critical endpoints are only running trusted, trusted software.
Tracked as CVE-2023-20858The issue was discovered by security analyst Jari Jääskelä and could allow a hacker with privileged access to the App Control admin console to gain access to the operating system using a specially designed entrance.
“A malicious actor with privileged access to the App Control administrative console may be able to use a specially crafted entry to gain access to the underlying server operating system,” read VMware review.
Injection flaws allow attackers to execute commands or code in the target application. They can lead to a complete compromise of back-end systems and all clients connecting to the vulnerable application.
VMware strongly recommends that administrators “upgrade as soon as possible” to a secure version of the product.
CVE-2023-20858 affects VMware Carbon Black App Control for Windows version 8.7.7 and earlier, version 8.8.5 and earlier, and version 8.9.3 and earlier. It is recommended that administrators upgrade to versions 8.9.4, 8.8.6And 8.7.8 or later.
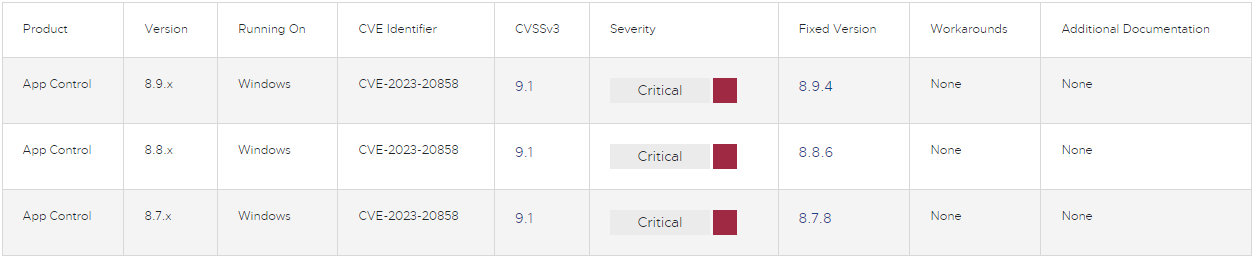
The VMware security advisory did not share any workarounds or mitigation advice, so the only safe option is to upgrade to the recommended versions.
Tuesday, VMware also patched CVE-2023-20855, a high-severity (CVSS v3:8.8) XXE (XML external entity) injection flaw that could allow an attacker to bypass XML parsing restrictions to access sensitive information or perform elevation of privileges.
CVE-2023-20855 impacts VMware Orchestrator on v8.11.1 (fixed version), vRealize Automation below v8.11.1 (fixed version) and VMware Cloud Foundation 4.x (fixed in KB90926).
[ad_2]
Source link
