[ad_1]

An ongoing malware campaign is targeting YouTube and Facebook users, infecting their computers with a new information stealer that will hijack their social media accounts and use their devices to mine cryptocurrency.
Security researchers from Bitdefender’s Advanced Threat Control (ATC) team discovered the new malware and dubbed it S1deload Stealer due to its heavy use of Sideloading DLLs to escape detection.
“Between July and December 2022, Bitdefender products detected more than 600 unique users infected with this malware,” said Bitdefender researcher Dávid Ács. said.
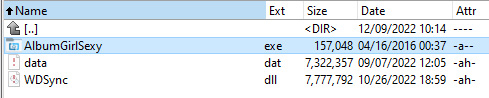
Victims are tricked into getting infected using social engineering and comments on FaceBook pages that push archives with adult themes (e.g., AlbumGirlSexy.zip, HDSexyGirl.zip, SexyGirlAlbum.zip, and more).
If the user downloads one of the linked archives, they will instead obtain a signed executable with a valid Western Digital digital signature and a malicious DLL (WDSync.dll) containing the final payload.
Once installed on victims’ devices, S1deload Stealer can be instructed by its operators to perform one of several tasks after connecting to the command and control (C2) server.
As Bitdefender discovered, it can download and run additional components, including a headless Chrome web browser that runs in the background and emulates human behavior to artificially increase views on YouTube videos and Facebook posts.
On other systems, it can also deploy a thief that decrypts and exfiltrates credentials and saved cookies from victim’s browser and Login Data SQLite database or a cryptojacker that will mine BEAM cryptocurrency.
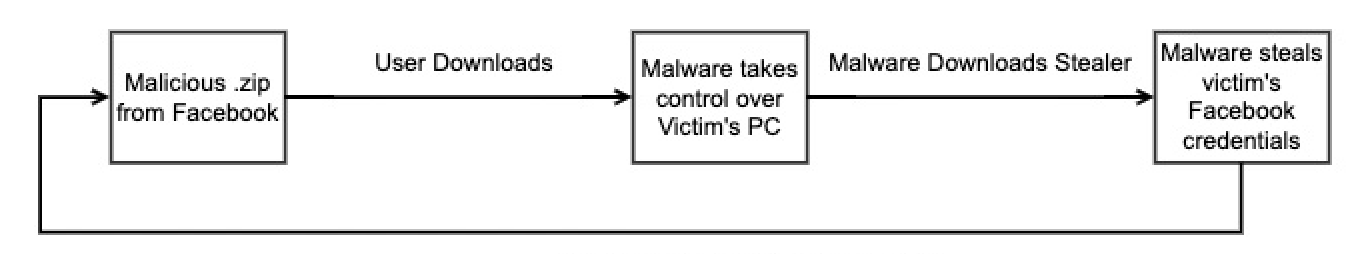
If it manages to steal a Facebook account, the malware will also try to estimate its real value by exploiting the Facebook Graph API to find out if the victim is the admin of a Facebook page or group, if he pays for advertisements or if he is linked. to a business manager account.
“The stealing component we observed in the wild steals credentials saved in the victim’s browser, exfiltrating them to the malware author’s server,” Ács added.
“The malware author uses the newly obtained credentials to spam social media and infect more machines, creating a feedback loop.”
To avoid getting infected and having your social media accounts hacked, you should never run executables from unknown sources and always keep your anti-malware software updated.
Indicators of Compromise (IOC) and YARA rules related to this malware campaign are available at the end of Bitdefender’s white paper (PDF).
Threat intelligence firm SEKOIA also spotted a new information-stealing strain known as Stealc and advertised on the dark web and hacking forums as featuring an easy-to-use admin panel and extensive data-stealing capabilities.
Unlike S1deload Stealer, Stealc malware is distributed via fake pirated software, a very popular tactic also used to push other info stealers like Vidar, Redline, Raccoon and Mars.
[ad_2]
Source link
