[ad_1]

The Vice Society ransomware gang is rolling out a rather sophisticated new PowerShell script to automate data theft from compromised networks.
Stealing corporate and customer data is a standard tactic in ransomware attacks to use as additional leverage when extorting victims or reselling the data to other cybercriminals for maximum profit.
Vice Society’s new data exfilter is fully automated and uses “living off the ground” binaries and scripts that are unlikely to trigger security software alarms, keeping their activities stealthy before the final attack stage. by ransomware, data encryption.
Powershell Exfiltration
The new data theft tool was discovered by Palo Alto Networks Unit 42 during an incident response in early 2023, when responders recovered a file named “w1.ps1” from the Palo Alto Networks network. a victim and, specifically, referenced in Event ID 4104: Script Block Logging Event.
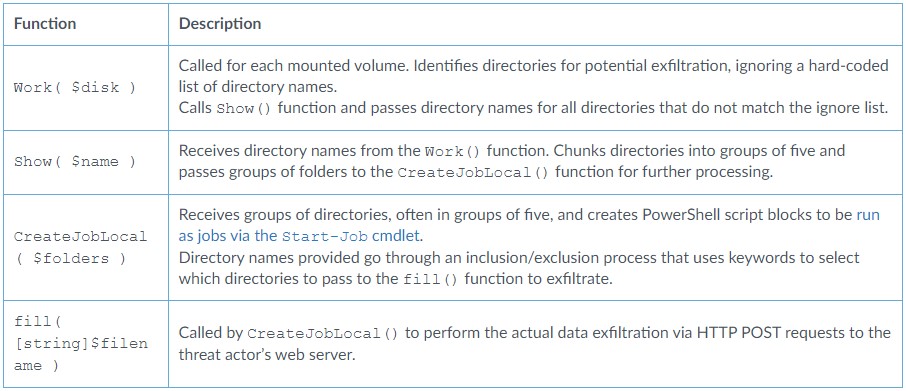
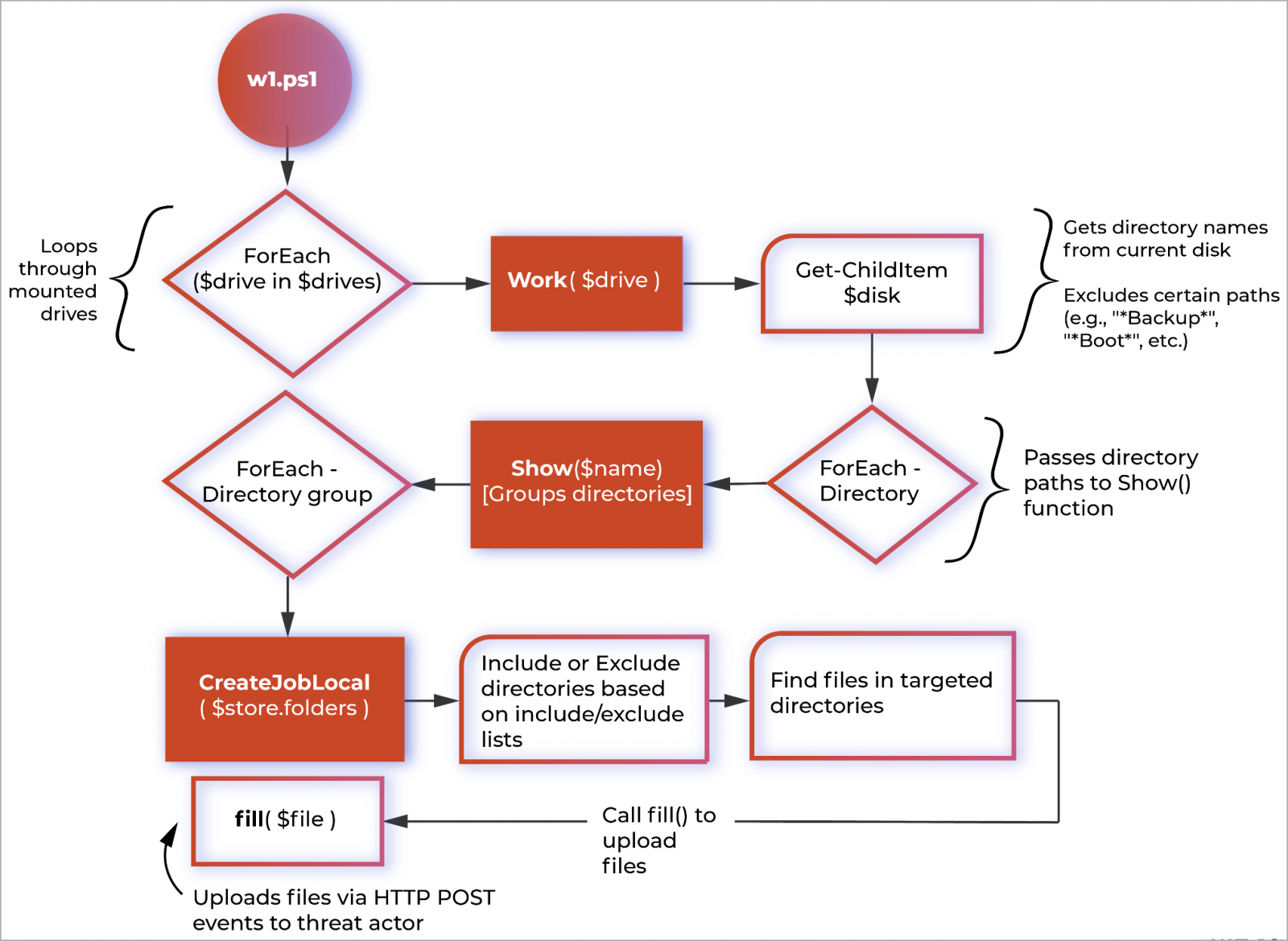
The script uses PowerShell to automate data exfiltration and consists of several functions, including Work(), Show(), CreateJobLocal(), and fill().
These four functions are used to identify potential directories for exfiltration, process groups of directories, and optionally exfiltrate data via HTTP POST requests to Vice Society’s servers.
“The script does not require any arguments, as the responsibility of which files to copy off the network is left to the script itself”, note unit 42 in the report.
“Testing has confirmed that the script ignores both files that are less than 10KB in size and those that have no file extension.”
Although there appears to be some automated functionality in the script to determine which files are stolen, there is still a master exclude and include list to help narrow down stolen files.
For example, the script will not steal data from folders whose names include common strings for backups, program installation folders, and Windows operating system folders.
However, it will specifically target folders containing more than 433 channels in English, Czech, German, Lithuanian, Luxembourgish, Portuguese and Polish, with emphasis on German and English.
For example, some of the folders it targets include:
*941*", "*1040*", "*1099*", "*8822*", "*9465*", "*401*K*", "*401K*", "*4506*T*", "*4506T*", "*Abkommen*", "*ABRH*", "*Abtretung*", "*abwickeln*", "*ACA*1095*", "*Accordi*", "*Aceito*", "*Acordemen*", "*Acordos*", "*Acuerde*", "*Acuerdo*", "*Addres*", "*Adres*", "*Affectation*", "*agreem*", "*Agreemen*Disclosur*", "*agreement*", "*Alamat*", "*Allocation*", "*angreifen*", "*Angriff*", "*Anmeldeformationen*", "*Anmeldeinformationen*", "*Anmeldenunter*", "*Anmeldung*", "*Anschrift*", "*Anspruch*", "*Ansspruch*", "*Anweisung*", "*AnweisungBank*", "*anxious*", "*Análise*", "*Apotheke*", "*ARH*", "*Asignación*", "*Asignatura*", "*Assegnazione*", "*Assignation*", "*Assignment*", "*Atribuição*", "*attorn*", "*Audit*", "*Auditnaadrese*", "*Aufführen*", "*Aufgabe*", "*Aufschühren*", "*Auftrag*", "*auftrunken*", "*Auftrunkinen*", "*Auswertung*", "*Avaliação*", "*Avaliações*", "*Avtal*", "*balanc*", "*bank*", "*Bargeld*", "*Belästigung*", "*Benef*", "*benefits*", "*Bericht*", "*Beschäftigung*", "*Betrug*", "*Bewertung*", "*bezahlen*", "*billing*", "*bio*"The PowerShell script uses system-native cmdlets like “Get-ChildItem” and “Select-String” to find and exfiltrate data from the infected machine, minimizing its footprint and maintaining a stealthy profile.
Another interesting aspect of Vice Society’s new data exfilter is its rate-limiting implementation that sets a maximum of 10 concurrently running tasks from five directory groups to avoid capturing too much of the host’s available resources.
While the specific purpose behind it is unclear, Unit 42 comments that it aligns with best coding practices and shows a professional level of script coding.
Vice Society evolves
Vice Society’s new data exfiltration script uses “live off the ground” tools to evade detection from most security software and features multiple processing and process queuing to keep its reduced footprint and stealth activity.
Unit 42 comments that this approach makes detection and hunting difficult, although security researchers have provided guidance on this at the bottom of their report.
In December 2022, SentinelOne warned that the Vice Society had switched to a sophisticated new file encryptor called “PolyVicewhich was likely provided by a contracted developer who also sold their malware to Chilly and SunnyDay ransomware.
Unfortunately, with the adoption of ever more sophisticated tools, the Vice Society has become a more formidable threat to organizations around the world, giving defenders fewer opportunities to detect and stop attacks.
[ad_2]
Source link
