[ad_1]

A previously unnamed ransomware has been rebranded as ‘Trigona’, launching a new Tor trading site where they accept Monero as a ransom payment.
Trigona has been active for some time, with samples seen earlier this year. However, these samples used email for negotiations and were not branded with a specific name.
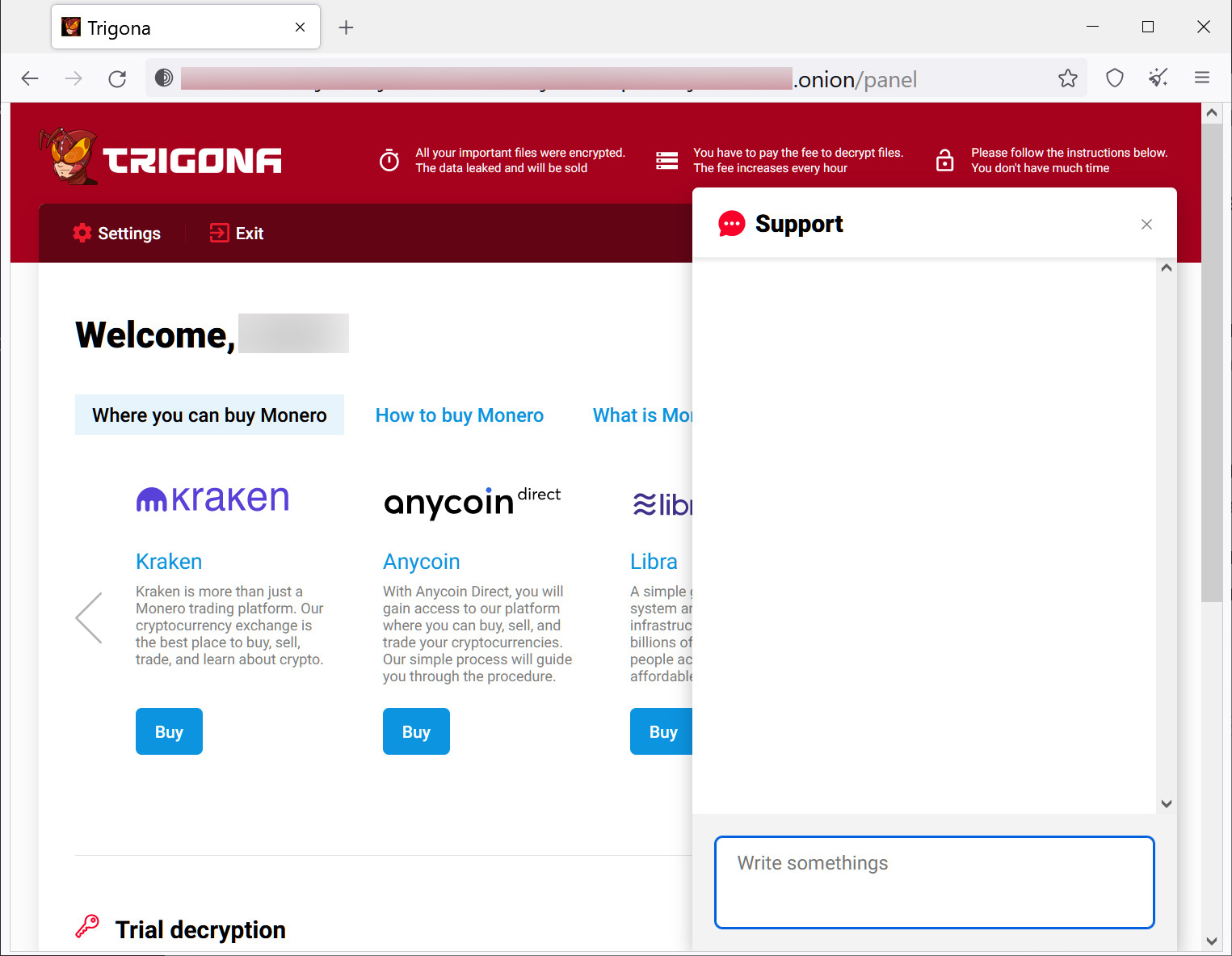
As discovered by MalwareHunterTeamStarting in late October 2022, the ransomware operation launched a new Tor trading site where they officially named themselves “Trigona”.
As Trigona is the name of a family of large stingless bees, the ransomware operation adopted a logo showing a person in a cyber bee-like costume, shown below.

Source: BleepingComputer
BleepingComputer is aware of numerous victims of the new ransomware operation, including a real estate company and what appears to be a village in Germany.
Trigona ransomware
BleepingComputer analyzed a recent sample of Trigona and discovered that it supports various command-line arguments that determine whether local or network files are encrypted, whether a Windows AutoRun key is added, and whether a victim ID ID (VID) or Campaign ID (CID) must be used.
The command line arguments are listed below:
/full
/!autorun
/test_cid
/test_vid
/path
/!local
/!lan
/autorun_onlyWhen encrypting files, Trigona will encrypt all files on a device except those located in specific folders, such as the Windows and Program Files folders. Additionally, the ransomware will rename the encrypted files to use the ._locked extension.
For example, the 1.doc file would be encrypted and renamed to 1.doc._locked as shown below.
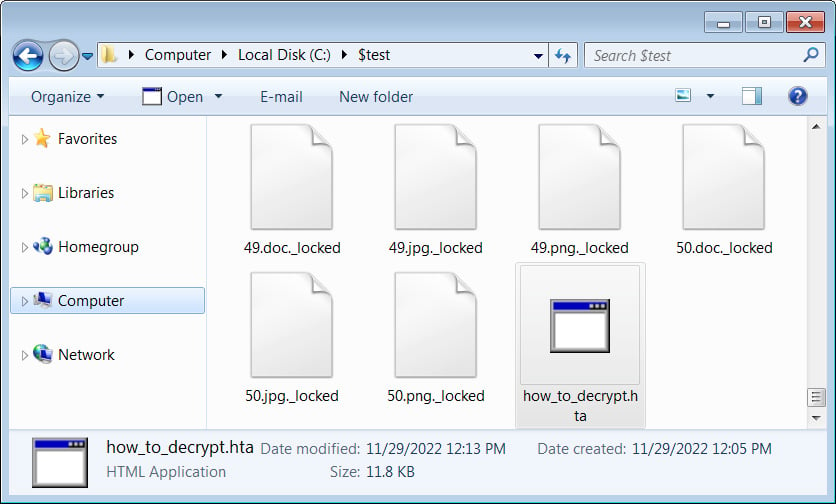
Source: BleepingComputer
The ransomware will also embed the encrypted decryption key, campaign ID and victim ID (company name) in the encrypted files.
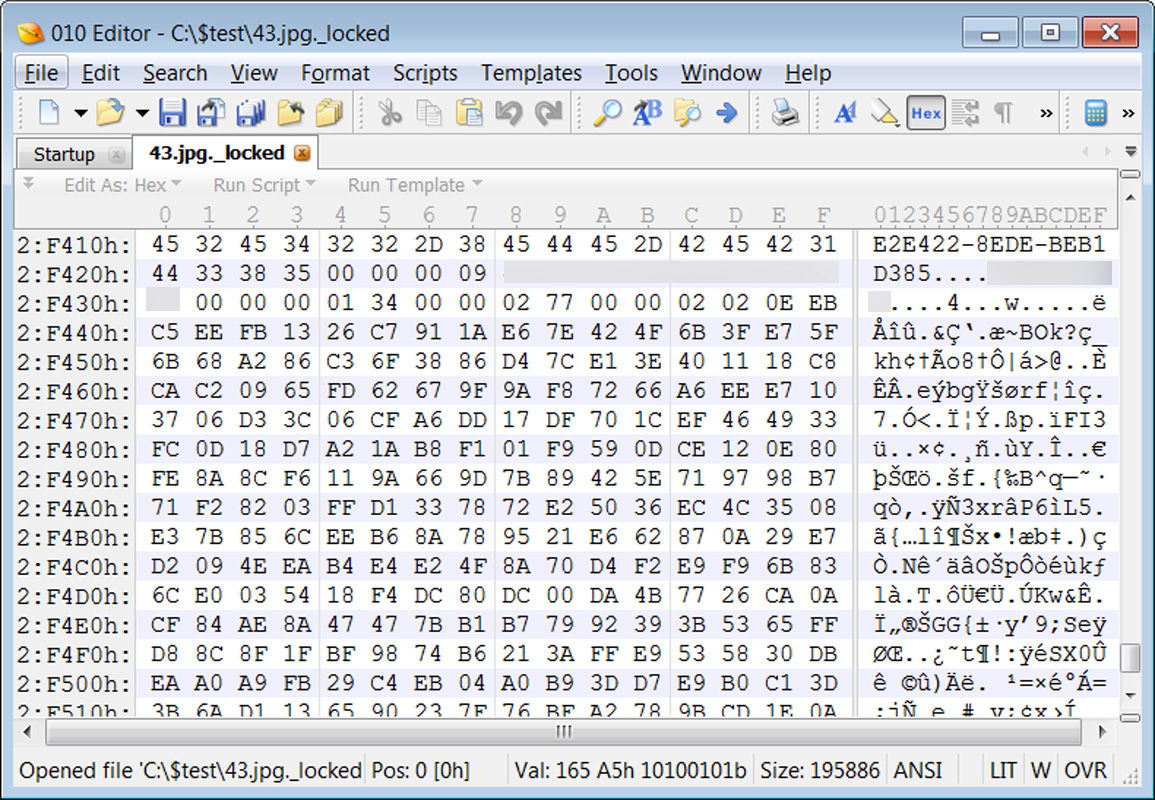
Source: BleepingComputer
A ransom note named how_to_decrypt.hta will be created in each scanned folder. This note displays information about the attack, a link to the Tor trading site, and a link that copies an authorization key to the Windows clipboard needed to connect to the Tor trading site.
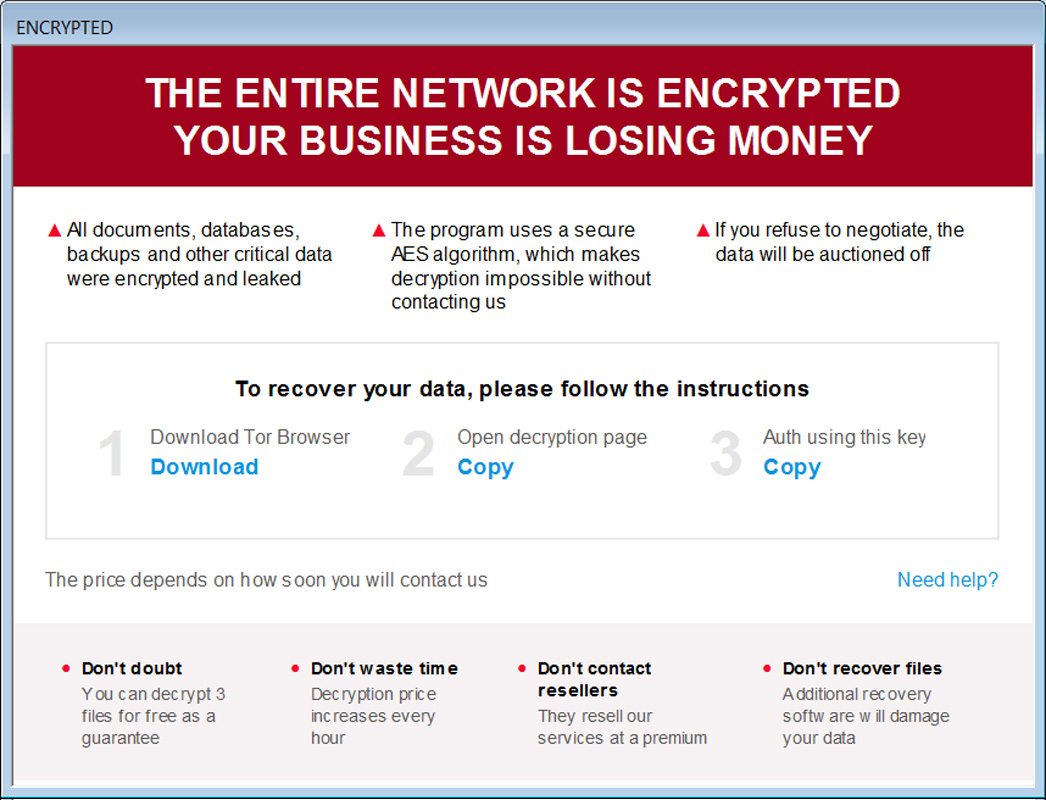
Source: BleepingComputer
After logging into the Tor site, the victim will receive information on how to buy Monero to pay a ransom and a support chat that they can use to negotiate with threat actors. The site also offers the ability to decrypt five files, up to 5MB each, for free.
BleepingComputer has not seen any active negotiations and it is unclear how much money the threat actors are demanding from the victims.
Source: BleepingComputer
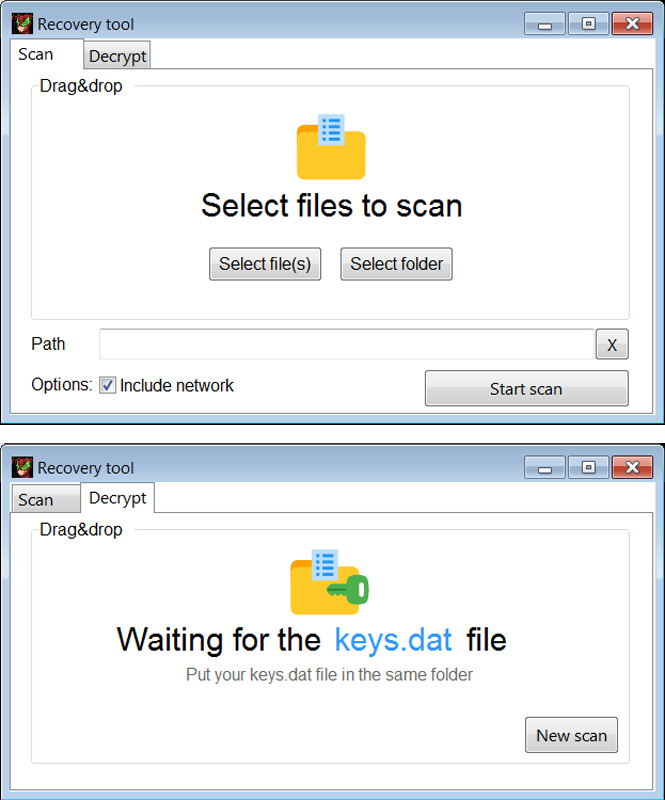
When a ransom is paid, victims receive a link to a decryptor and a keys.dat file, which contains the private decryption key.
The decryptor allows you to decrypt individual files or folders on the local device and network shares.
Source: BleepingComputer
It is unclear how the operation breaches networks or deploys ransomware. Also, while their ransom notes claim to steal data in attacks, BleepingComputer has seen no evidence of this.
However, their attacks have increased worldwide, and with the investment in a dedicated Tor platform, they will likely continue to expand their operations.
[ad_2]
Source link
