[ad_1]

Password salting is a technique for making passwords harder to crack by adding random values to the stored password hash.
However, in order to understand password salting and its benefits, it is necessary to understand how Windows stores passwords and some of the risks associated with storing passwords in this manner.
Password hashes and where it lacks security
When you create a user account in Windows, the operating system does not actually store the account password. Otherwise, it would be too easy for malware, cybercriminals, or even dishonest administrators to simply track down user passwords.
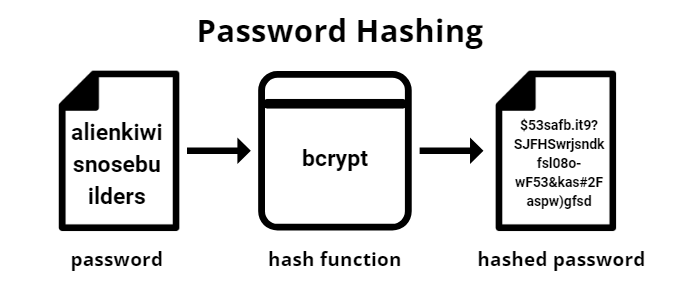
Instead, passwords are hashed before being stored. In other words, a mathematical formula is used to turn passwords into hexadecimal strings. It is these strings, or hashes, that are stored rather than the password itself.
When a user attempts to log on to a system, they are prompted for a user name and password. When the user types their password, the password they typed is hashed using the same formula used to create the stored password hash.
At this point, the hash of the password the user just entered is compared to the hash of the stored password. If the two hashes are identical, the user has entered the correct password and is therefore authorized to log into the system.
The problem with password hashes is that they can make it easier for an attacker to find a user’s password. Long passwords can make brute force password cracking impractical or impossible. However, an attacker can use a password hash as is, avoiding brute force cracking altogether.
The reason this is possible is that Windows does not use a unique hashing algorithm on every system.
Suppose for a moment that you created an account and then looked up the hash of that account’s password. If you were then to create a different account on a completely different system, but used the same password as before, both accounts would have identical password hashes.
Cybercriminals know this and have created huge databases of passwords and their corresponding hashes. This means that if an attacker wants to crack an account’s password, all they have to do is check if the hash of the password is listed in their password database.
If the hash is present in the database, then they can use a simple table lookup to find the password that matches the hash, without the hassle of a brute force crack.
Increase the security of your passwords stored in AD
This is where password salting comes in. A salt is an added value to the user’s password. This happens behind the scenes without the knowledge of the user.
Adding a salt causes the hash of the password to change, which makes it much more difficult to use a table lookup as a means of cracking the password.
When properly implemented, the salts are randomized, with a different salt being used for each user. This means that even if two users in your organization have identical passwords, their password hashes will be different because a different salt was used for each.
Disadvantages of password salting
Using password salts can be a very effective way to protect your organization’s user accounts. Even so, password salting has at least some drawbacks.
- Password salting is not fast
First, the salting process is computationally intensive. As such, salting can slow down the user authentication process, especially in situations where domain controllers are under-provisioned or a large number of users attempt to login at the same time.
- Password salting is not a beginner level protocol
Another disadvantage of password salting is that it can be difficult to implement. The Windows operating system does not natively integrate a salting mechanism. According to Microsoft, “Neither the NT hash nor the LM hash are salted”. As such, salting will require the use of third-party software.
Secure alternatives to password salting
Of course, it is possible to secure your organization’s passwords without resorting to password salting. Specops password policy for example, contains tools to prevent users from using weak passwords.
This means not only enforcing password complexity requirements (even beyond what is possible using only Windows), but also preventing users from choosing passwords susceptible to dictionary attacks than word salting. password would normally prevent.
More importantly, Specops maintains a database of over 3 billion passwords known to have been compromised.
The Specops password policy actively compares user passwords against this database to see if the user is using a compromised password, then forces a password change if necessary. You can test the Specops password policy in your Active Directory with a free trial, anytime.
Remember that array-based lookup attacks are only effective if the user’s password hash is listed in the array. The Specops Password Policy can help prevent users from using passwords known to be vulnerable to these types of attacks.
The result is a level of protection comparable to password salting, but without the hassle of managing salts.
Sponsored and written by Specops software
[ad_2]
Source link
