[ad_1]

Toyota Motor Corporation discovered two other misconfigured cloud services that leaked car owners’ personal information for more than seven years.
The discovery came after the Japanese automaker conducted a thorough investigation of all cloud environments managed by Toyota Connected Corporation after discovering a misconfigured server that exposed location data more than 2 million customers for ten years.
“We conducted an investigation for all cloud environments managed by TOYOTA Connected Corporation (TC). It was discovered that part of the data containing customer information had been potentially accessed from outside,” reads the new Toyota Reviews.
The first cloud service exposed the personal information of Toyota customers in Asia and Oceania between October 2016 and May 2023.
The database, which should have been accessible only to resellers and service providers, was publicly exposed, leaking the following customer information:
- Address
- Name
- Phone number
- E-mail address
- Customer No.
- Vehicle registration number
- Vehicle Identification Number (VIN)
The Japanese manufacturer did not specify how many customers were affected by this leak.
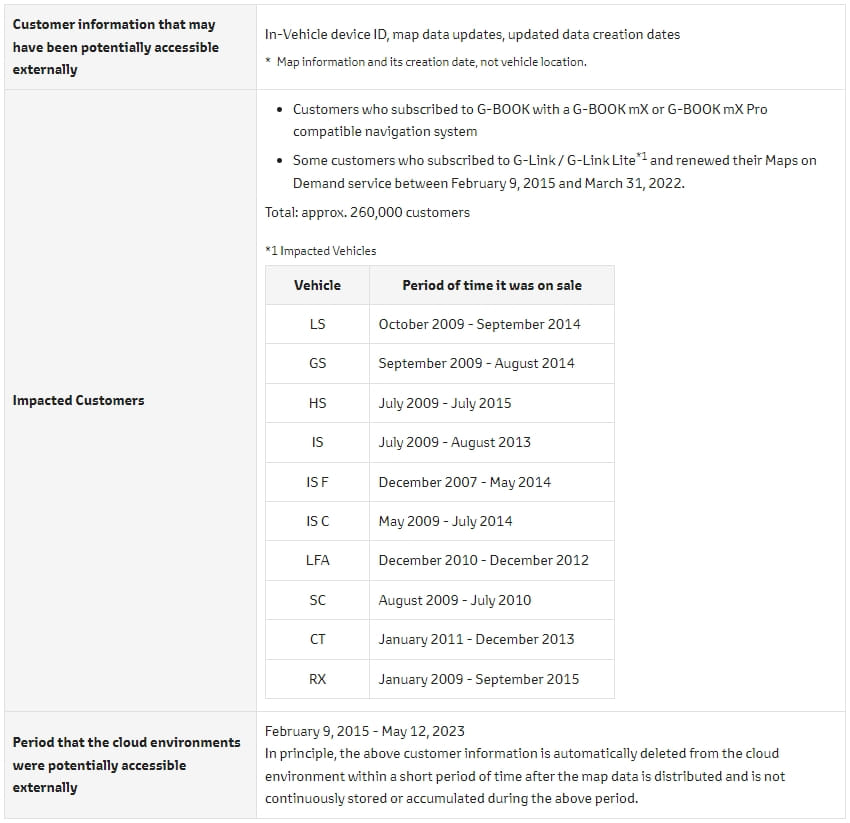
The second cloud instance was exposed between February 9, 2015 and May 12, 2023 and contained less sensitive data related to car navigation systems. This data includes in-vehicle device (navigation terminal) ID, map data updates and data creation dates (no vehicle location data) of approximately 260,000 customers in Japan.
This leak affected customers who subscribed to the G-BOOK navigation system with a G-BOOK mX or G-BOOK mX Pro and some who subscribed to G-Link / G-Link Lite and renewed their cards in using Toyota’s On-Demand Service between February 9, 2015, and March 31, 2022.
Affected vehicles are models of Toyota’s sub-brand, Lexus, and include LS, GS, HS, IS, ISF, ISC, LFA, SC, CT and RX cars sold between 2009 and 2015.
Toyota claims that data entries were automatically deleted from the cloud environment after a period of time, so there was a limited amount of data exposed at any given time.
The automaker says that even if the data were accessed from the outside, it would not be enough to infer identifying details about the customer or gain access to vehicle systems in any way.
Toyota says it has a system in place that regularly monitors cloud configurations and database settings across all of its environments to prevent such leaks in the future.
[ad_2]
Source link
