[ad_1]

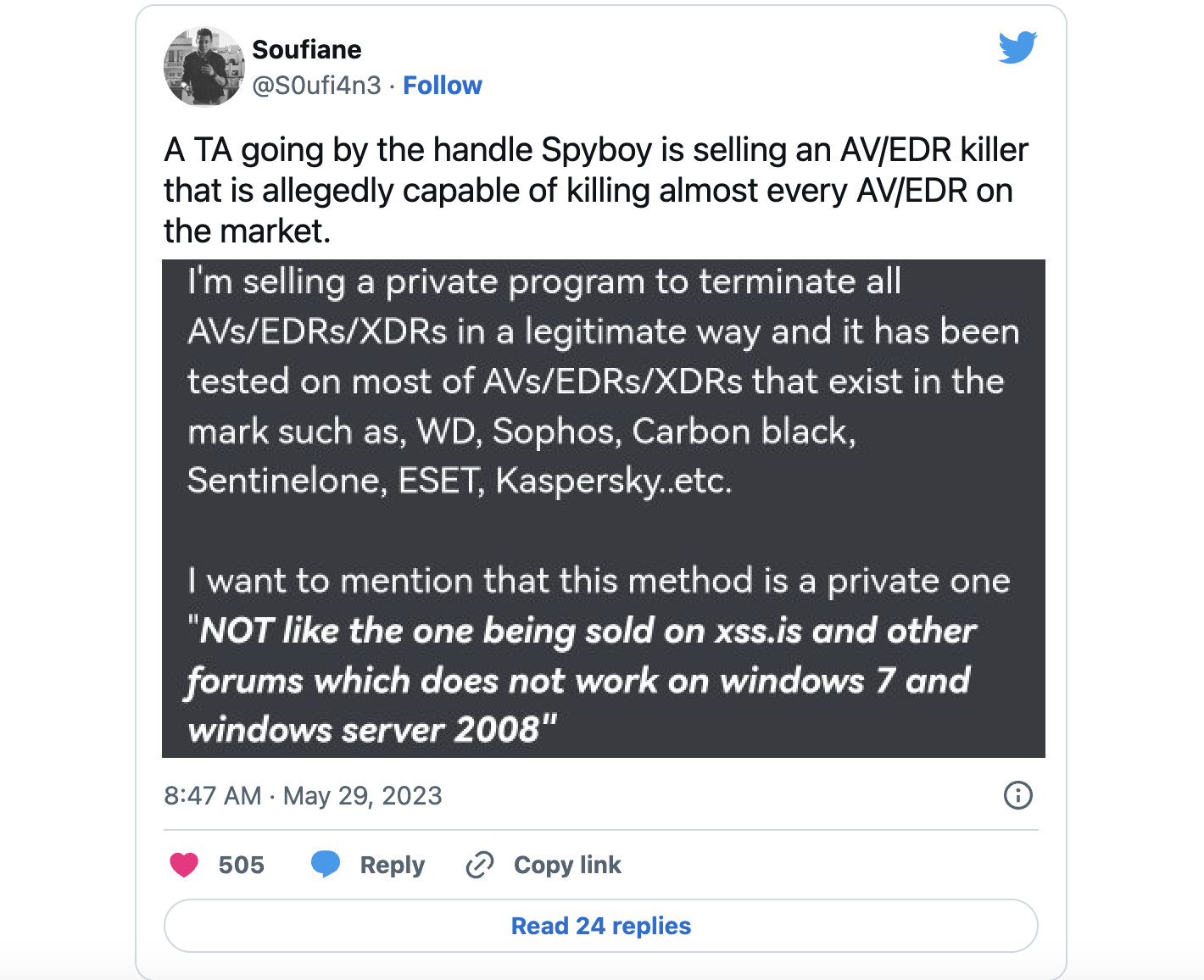
A malicious actor known as Spyboy is promoting a tool called “Terminator” on a Russian-speaking hacking forum that can allegedly terminate any antivirus, XDR and EDR platform. However, CrowdStrike says this is just a sophisticated BYOVD (Bring Your Own Vulnerable Driver) attack.
The terminator is supposedly able Bypass 24 Antivirus (AV), Endpoint Detection and Response (EDR), and Extended Detection and Response (XDR) security solutions, including Windows Defender, on devices running Windows 7 and later.
Spyboy sells the software at prices ranging from $300 for a single bypass to $3,000 for an all-in-one bypass.
“The following EDRs cannot be sold alone: SentinelOne, Sophos, CrowdStrike, Carbon Black, Cortex, Cylance,” the threat actor states, with a disclaimer that “ransomware and lockers are not allowed and I I am not responsible for these actions”.
To use Terminator, “clients” require administrative privileges on the targeted Windows systems and must prompt the user to accept a User Account Control (UAC) pop-up that will be displayed when running the tool.
However, as a CrowdStrike engineer revealed in a Reddit post, Terminator simply removes the legitimate, signed Zemana anti-malware kernel driver named zamguard64.sys Or zam64.sys in the C:\Windows\System32\ folder with a random name between 4 and 10 characters.
After the malicious driver is written to disk, Terminator loads it to use its kernel-level privileges to kill user-mode processes of AV and EDR software running on the device.
Although it is unclear how the Terminator program interfaces with the pilot, a The PoC exploit was released in 2021 which exploits driver flaws to execute commands with Windows kernel privileges, which could be used to terminate normally protected security software processes.
This driver is only detected by a single anti-malware scan engine as a vulnerable driver at this time, according to a VirusTotal Scan.
Thankfully, Nextron Systems Research Manager Florian Roth and Threat Researcher Nasreddine Bencherchali have already shared YARA and SIGMA (per hash And name) that can help defenders detect the vulnerable driver used by the Terminator tool.
This technique is prevalent among threat actors who like to install vulnerable Windows drivers after escalating privileges to bypass security software running on compromised machines, execute malicious code and deliver additional malicious payloads.
In BYOVD (Bring Your Own Vulnerable Driver) attacks, legitimate drivers signed with valid certificates and able to run with kernel privileges are dropped on victims’ devices to disable security solutions and take control of the system .
A wide range of threatening groups have used this technique for years, ranging from financially motivated groups ransomware gangs For state-backed hacking outfits.
More recently, security researchers at Sophos X-Ops spotted a new hacking tool dubbed AuKill used in the wild to disable EDR software using a vulnerable Process Explorer driver before deploying ransomware in BYOVD attacks.
[ad_2]
Source link