[ad_1]
The Dark Pink APT hacking group continues to be very active in 2023, observed targeting government, military and educational organizations in Indonesia, Brunei and Vietnam.
The threat group has been active since at least mid-2021, primarily targeting entities in the Asia-Pacific region, but it was exhibited for the first time in January 2023 by a report from Group IB.
Researchers report that after analyzing signs of previous threat actor activity, they have now uncovered additional violations against an educational institute in Belgium and a military body in Thailand.
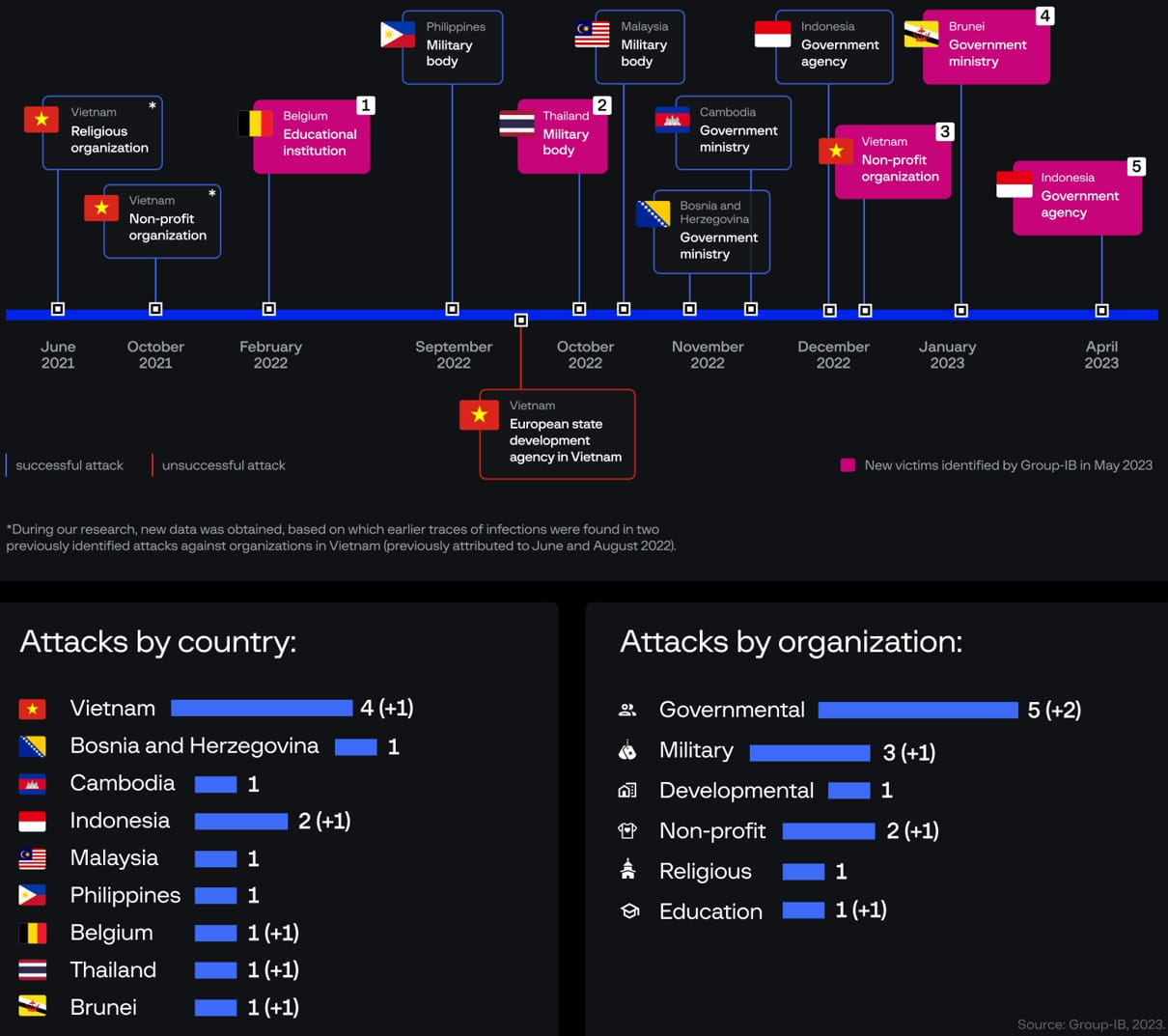
Despite Group-IB’s previous exposure, Dark Pink has shown no signs of slowing down, and the company claims to have identified at least five attacks perpetrated by the group following the publication of the previous report.
In recent attacks, Dark Pink showcased a revamped attack chain, implemented different persistence mechanisms, and deployed new data exfiltration tools, likely attempting to evade detection by moving their operations away from publicly available IoCs. (indicators of compromise).
Infiltration and Lateral Movement
Dark Pink’s attacks continue to rely on spear-phishing ISO archives for the initial infection, which uses side-loading DLLs to launch its backdoors, “TelePowerBot” and “KamiKakaBot”.
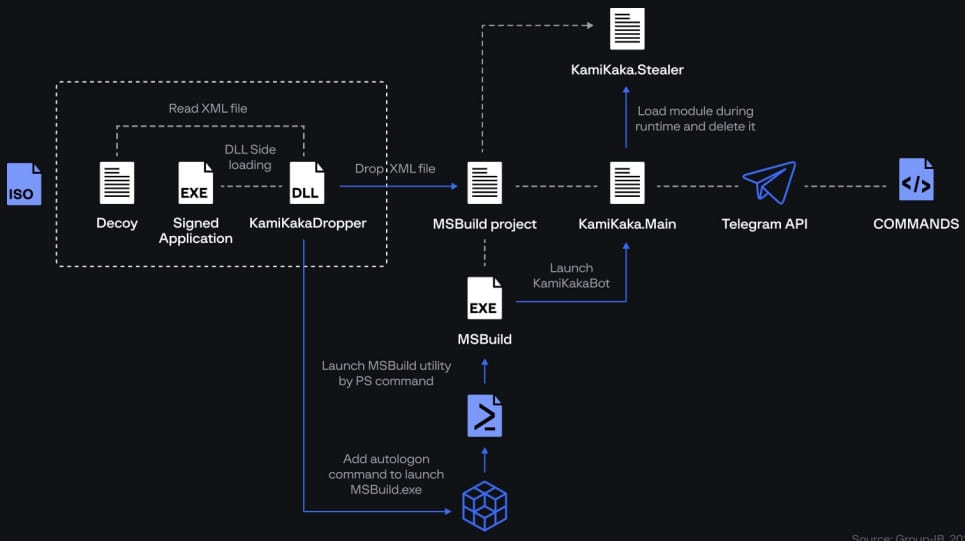
A new element is that the attackers have now split the functionality of KamiKakaBot into two parts, namely device control and data theft.
Additionally, the implant is now loaded from memory, without ever touching the disc. This helps to evade detection because antivirus tools do not monitor processes that launch in memory.
KamiKakaBot continues to target data stored in web browsers and sends it to attackers via Telegram. Additionally, the backdoor can download and run arbitrary scripts on the hacked device.
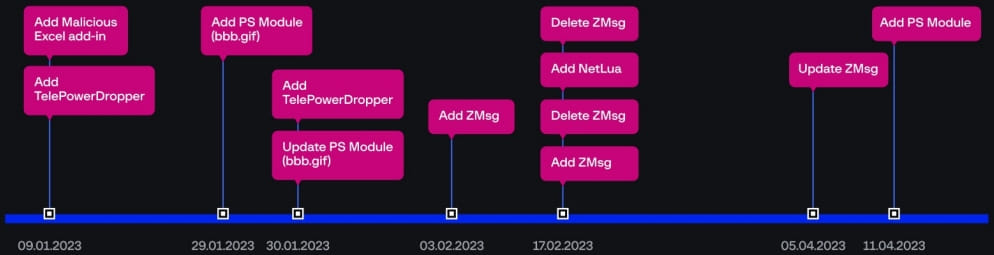
Group-IB discovered that Dark Pink uses a private GitHub repository to host additional modules downloaded by its malware on compromised systems.
Threat actors only made 12 commits to this repository throughout 2023, mostly to add or update malware droppers, PowerShell scripts, ZMsg infostealer, and hack tool. Netlua privilege escalation.
One of these PowerShell scripts is essential to Dark Pink’s lateral movement strategy, helping to identify and interact with SMB shares within the network.
The script retrieves a ZIP archive from GitHub, saves it to a local directory, then creates LNK files on each SMB share linked to the malicious executable in the archive.
When these LNK files are opened, they launch the malicious executable, spreading Dark Pink across the network and extending their reach to additional systems.
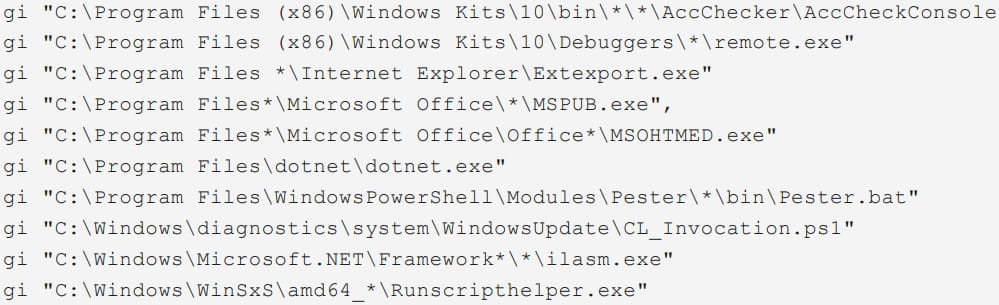
Dark Pink also uses PowerShell commands to perform checks for the presence of legitimate software and developer tools on the compromised device that they can abuse for their operations.
These tools include “AccCheckConsole.exe”, “remote.exe”, “Extexport.exe”, “MSPUB.exe” and “MSOHTMED.exe”, which can be exploited for proxy execution, downloading additional payloads , etc.
However, Group-IB notes that it has not seen any instances of abuse of these tools in the attacks observed.
New data theft tactics
Group-IB reports that Dark Pink is now showing variety in its data exfiltration method, going beyond sending ZIP archives to Telegram channels.
In some cases seen by analysts, the attackers used DropBox downloads, while in others they used HTTP exfiltration using a temporary endpoint created with the “Webhook.site” service or Windows servers .
The previously mentioned scripts also provide the ability to exfiltrate data by creating new WebClient objects to upload files to an external address using the PUT method after setting the location of the target files on the hacked computer.
Group-IB concludes that Dark Pink threat actors are undeterred by their previous exposure and are unlikely to stop now.
Most likely, attackers will continue to update their tools and diversify their methods as much as possible.
[ad_2]
Source link
