[ad_1]

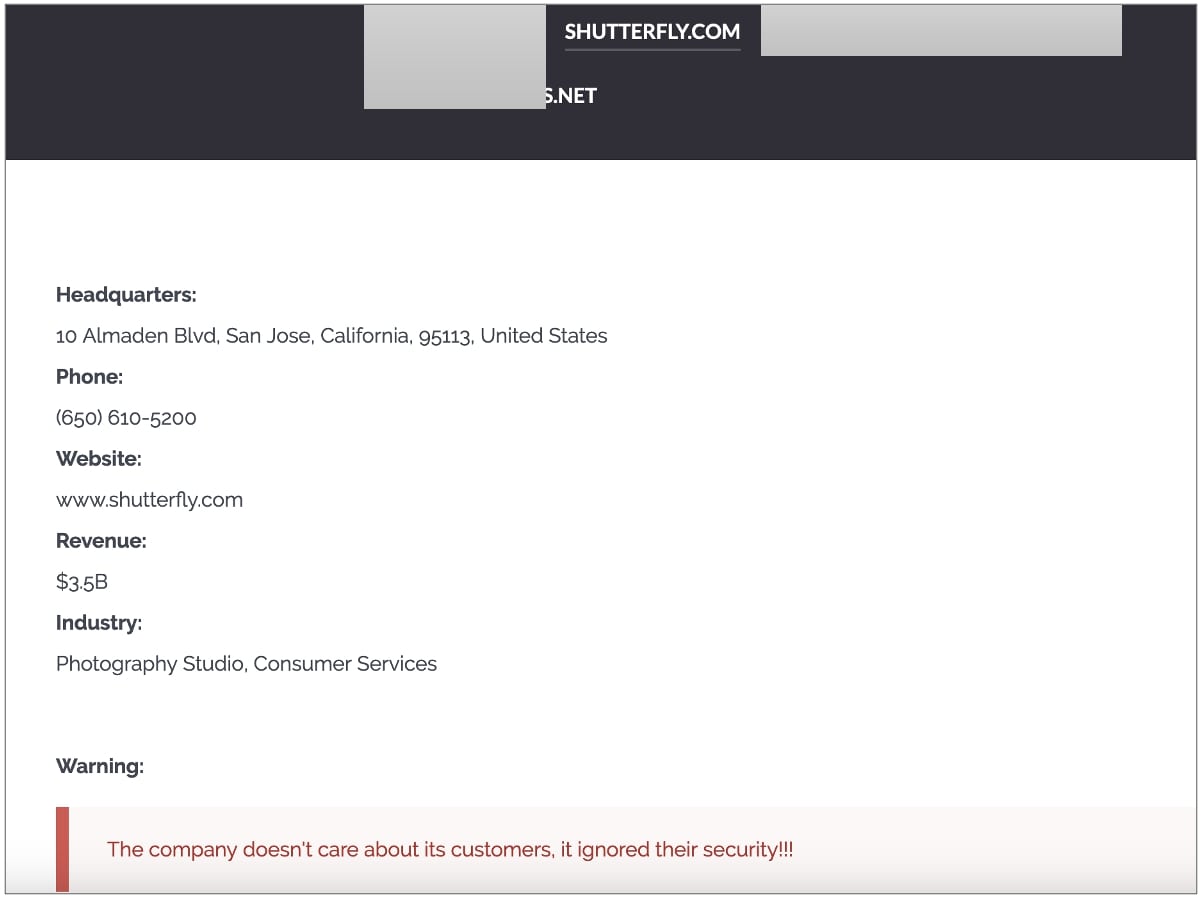
Shutterfly, an online retail and photography manufacturing platform, is among the latest victims of Clop ransomware.
Over the past few months, the Clop ransomware gang has exploited a vulnerability in the MOVEit file transfer utility to breach hundreds of companies in order to steal their data and attempt to extort them.
Shutterfly offers photography-related services to consumers, businesses, and education through a variety of brands, including Shutterfly.comBorrowLenses, GrooveBook, Snapfish and Lifetouch.
In ransomware attacks, hackers gain access to a corporate network and steal data and files as they spread through the system. Once they gain access to a Windows domain controller, and after harvesting all valuable data, they deploy their ransomware to encrypt all network devices.
Shutterfly: security of customer and employee data
This week, the Clop ransomware gang published Shutterfly’s name on its data leak site, among other companies it has targeted, largely through the MOVEit SQL Injection vulnerabilityfollowed as CVE-2023-34362.
“Shutterfly can confirm that it was one of several companies impacted by the MOVEit vulnerability. Shutterfly’s business unit, Shutterfly Business Solutions (SBS), has used the MOVEit platform for some of its operations,” confirmed a Shutterfly spokesperson told BleepingComputer.
“After learning of the vulnerability in early June, the company quickly took action, taking relevant systems offline, implementing fixes provided by MOVEit, and initiating a forensic examination of certain systems with the assistance of medical companies. -first-rate legal documents.”
The company has not commented on the size of the ransom demand, but says customer and employee data is safe.
“After a thorough investigation with the assistance of a leading third-party forensics firm, we have no indication that Shutterfly.com, Snapfish, Lifetouch or Spoonflower consumer data or employee information has been impacted by the MOVEit vulnerability.”
In March 2022, Shutterfly had revealed to be hit by Conti ransomware attack which happened in December 2021. At the time of this attack, a source informed BleepingComputer that Conti had encrypted on 4,000 devices and 120 VMware ESXi servers owned by Shutterfly.
Hundreds of people affected by MOVEit vulnerabilities
In June, Clop told BleepingComputer that by exploiting this flaw, he had hacked into servers belonging to “hundreds of companies” to steal data, which is apparent from a significant number of organizations that have so far disclosed to have been hacked during the Clop’s MOVEit hacking frenzy.
Some big names like the British oil and gas multinational, Shell, German Bankthe University of Georgia (UGA) and University System of Georgia (USG), UnitedHealthcare Student Resources (UHSR), Heidelberger Druck and Landal Greenparks have since confirmed to BleepingComputer that they were affected by the attacks.
Other organizations that have previously disclosed MOVEit Transfer violations include Zellis (and its customers BBC, Boots, Aer Lingus and Irish HSE), OfcamTHE Nova Scotia governmentTHE US state of MissouriTHE US state of IllinoisTHE University of RochesterTHE American Board of Internal Medicine, BORN IN OntarioSOVOS [1, 2]And Extreme networks.
Previously, the US Cybersecurity and Infrastructure Security Agency (CISA) also revealed that several US federal agencies had been breached, according to a CNN report. Two U.S. Department of Energy (DOE) entities were also compromised, according to Federal News Network.
In June, MOVEit Transfer customers were asked to remedy a separate SQL injection flaw (tracked as CVE-2023-35708), PoC exploits for which have surfaced online.
Last week, MOVEit addressed another critical SQL injection flaw (tracked as CVE-2023-36934) and notified customers to patch their applications.
Customers using the MOVEit File Transfer utility should ensure their instances are up to date and watch out for any new vulnerabilities that could be exploited in the wild.
BleepingComputer continues to monitor and cover incidents as well as program-related vulnerability advisories.
[ad_2]
Source link
