[ad_1]
The Russian state-sponsored hacking group “APT29” (aka Nobelium, Cloaked Ursa) uses unconventional decoys like car listings to trick diplomats in Ukraine into clicking on malicious links that deliver malware.
APT29 is linked to the Russian government’s Foreign Intelligence Service (SVR) and has been responsible for numerous cyber espionage campaigns targeting highly interested individuals around the world.
Over the past two years, Russian hackers focused on NATO, EUand Ukrainian targets, using phishing emails and documents on foreign policy topics, as well as fake websites to infect their targets with stealth backdoors.
A report released today by Palo Alto Network The Unit 42 team explains that APT29 has evolved its phishing tactics, using more personal lures for the recipient of the phishing email.
Luxury cars in Kyiv
In one of the most recent APT29 operations spotted by Unit 42, which began in May 2023, threat actors use an advertisement for a BMW car to target diplomats in Ukraine’s capital, Kyiv.
The sales flyer was sent to the diplomat’s email addresses, mimicking a legitimate car sale circulated two weeks earlier by a Polish diplomat preparing to leave Ukraine.

When recipients click on the “more high quality photos” link embedded in the malicious document, they are redirected to an HTML page that delivers payloads of malicious ISO files via HTML smuggling.
HTML smuggling is a technique used in phishing campaigns that use HTML5 and JavaScript to hide malicious payloads in encoded strings in an HTML attachment or web page. These strings are then decoded by a browser when a user opens the attachment or clicks on a link.
Using this technique helps evade security software because the malicious code is obfuscated and only decoded when rendered in the browser.
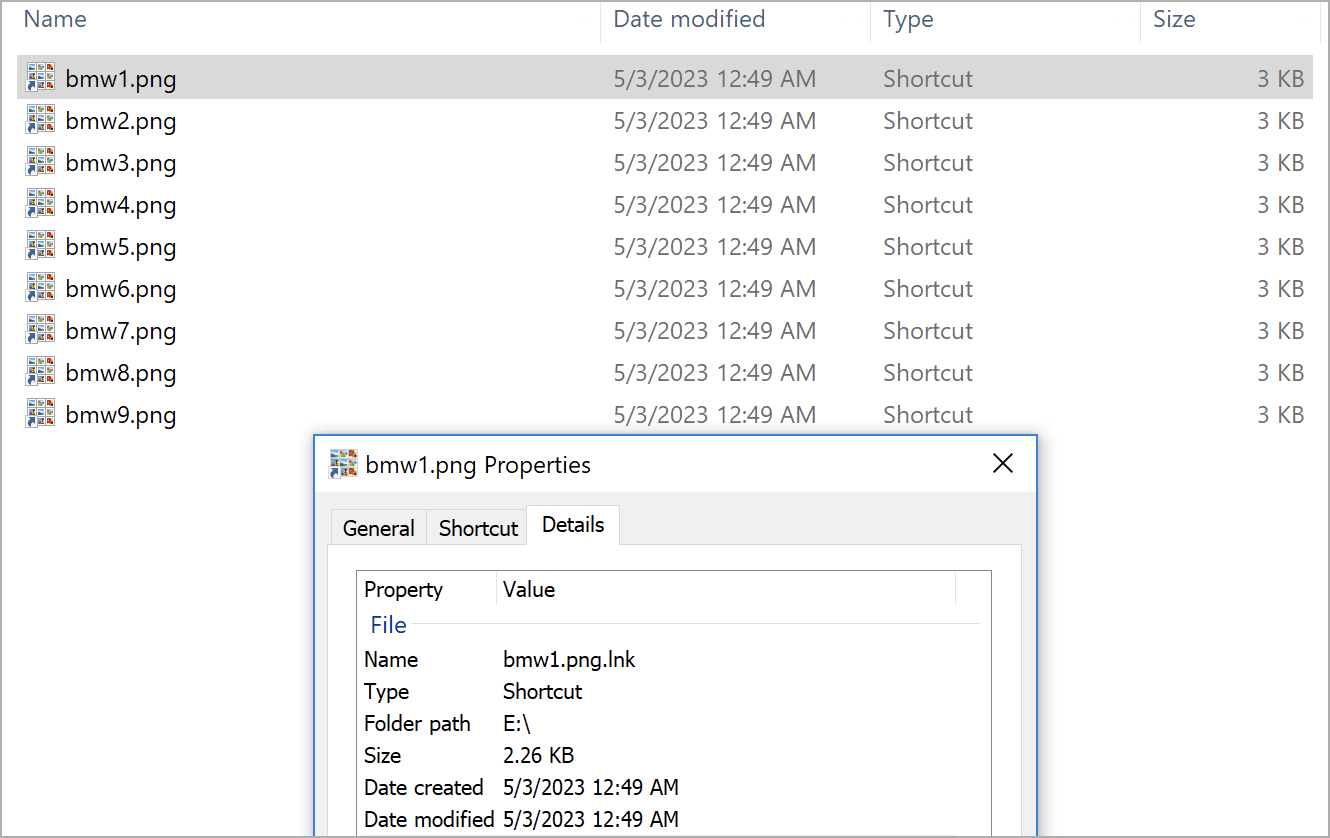
The ISO file contains what appear to be nine PNG images but are, in fact, LNK files that trigger the chain of infection shown in the diagram below.
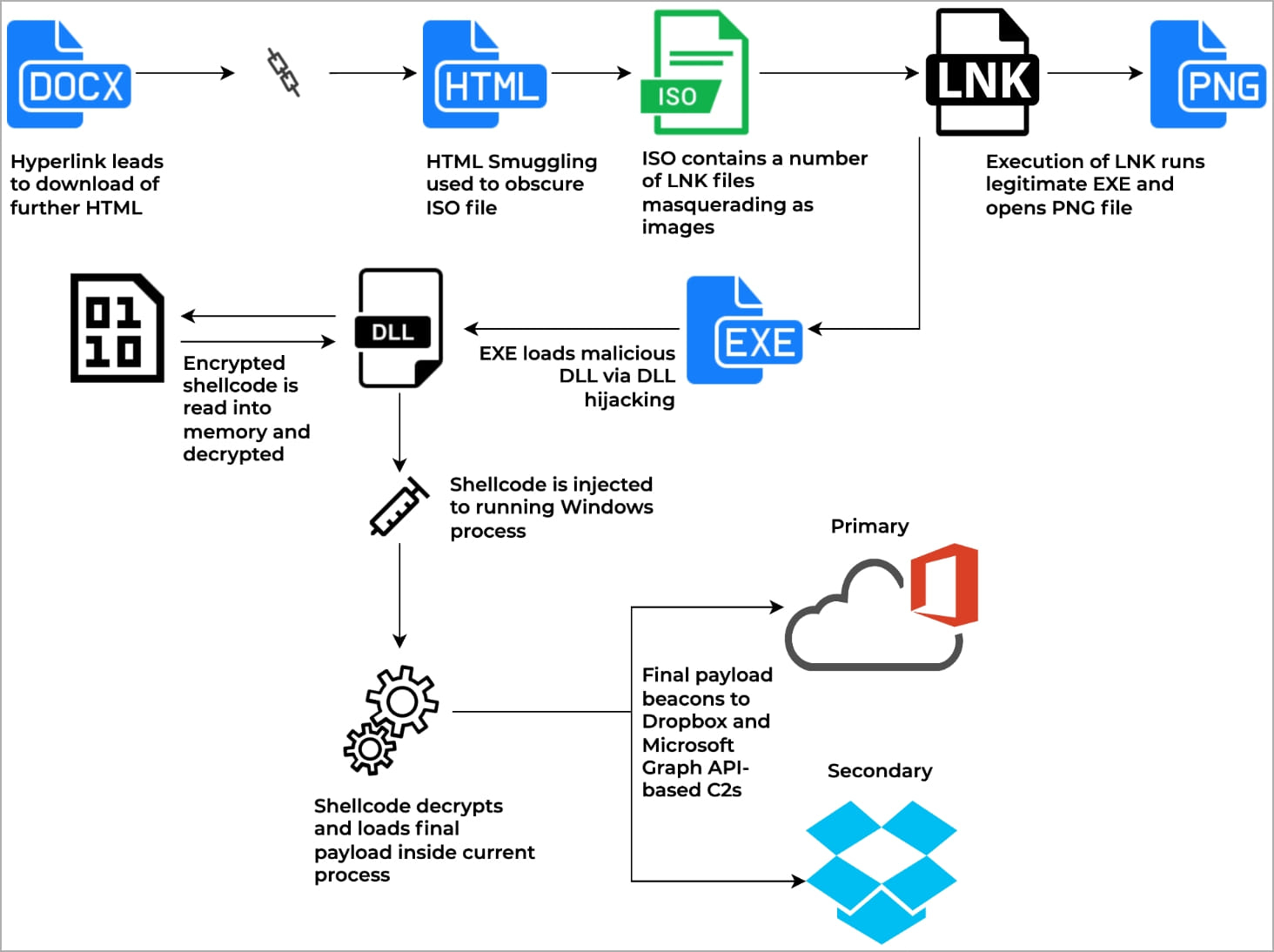
When the victim opens one of the LNK files masquerading as PNG images, it launches a legitimate executable that uses DLL sideloading to inject shellcode into the current process in memory.
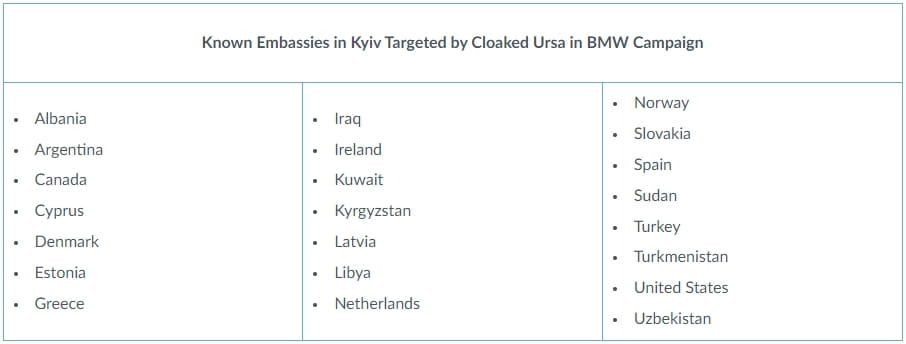
Unit 42 reports that this campaign has targeted at least 22 of the 80 foreign missions in Kyiv, including those from the United States, Canada, Turkey, Spain, the Netherlands, Greece, Estonia and Denmark. However, the infection rate remains unknown.
About 80% of the email addresses that received the malicious flyer were publicly available online, while APT29 must have obtained the remaining 20% via account compromise and intelligence gathering.
Another recent example of APT29’s willingness to exploit real incidents for phishing purposes is a PDF sent to the Turkish Ministry of Foreign Affairs (MFA) in early 2023 guiding humanitarian aid for the earthquake that hit southern Turkey in February.
Unit 42 comments that the malicious PDF was likely shared among MFA employees and forwarded to other Turkish organizations, as the attack took advantage of the excellent timing.
As the conflict in Ukraine persists and evolving developments within NATO threaten to alter the geopolitical landscape, Russian cyber espionage groups are expected to continue and even intensify their efforts to target diplomatic missions.
[ad_2]
Source link
