[ad_1]

GitHub today announced the introduction of support for passwordless authentication in the public beta, allowing users to switch from security keys to access keys.
Access keys are associated with individual devices such as computers, tablets or smartphones and play a vital role in reducing the likelihood of data breaches by protecting users against phishing attacks by thwarting data theft. identifiers and range attempts.
They also allow logging into applications and online platforms using personal identification numbers (PINs) or biometric authentication methods, such as facial recognition or fingerprints.
By eliminating the need to remember and manage unique passwords for every app and website, they also dramatically improve user experience and security.
GitHub Staff Product Manager Hirsch Singhal revealed today that “Security Keys are now available in public beta. Activation allows you to upgrade Security Keys to Security Keys and to use them instead of your password and 2FA method”.
To activate access keys on your account, click your profile picture in the upper right corner of any GitHub page. From there, open the “Features Overview” menu and click on the “Enable Passkeys” option.
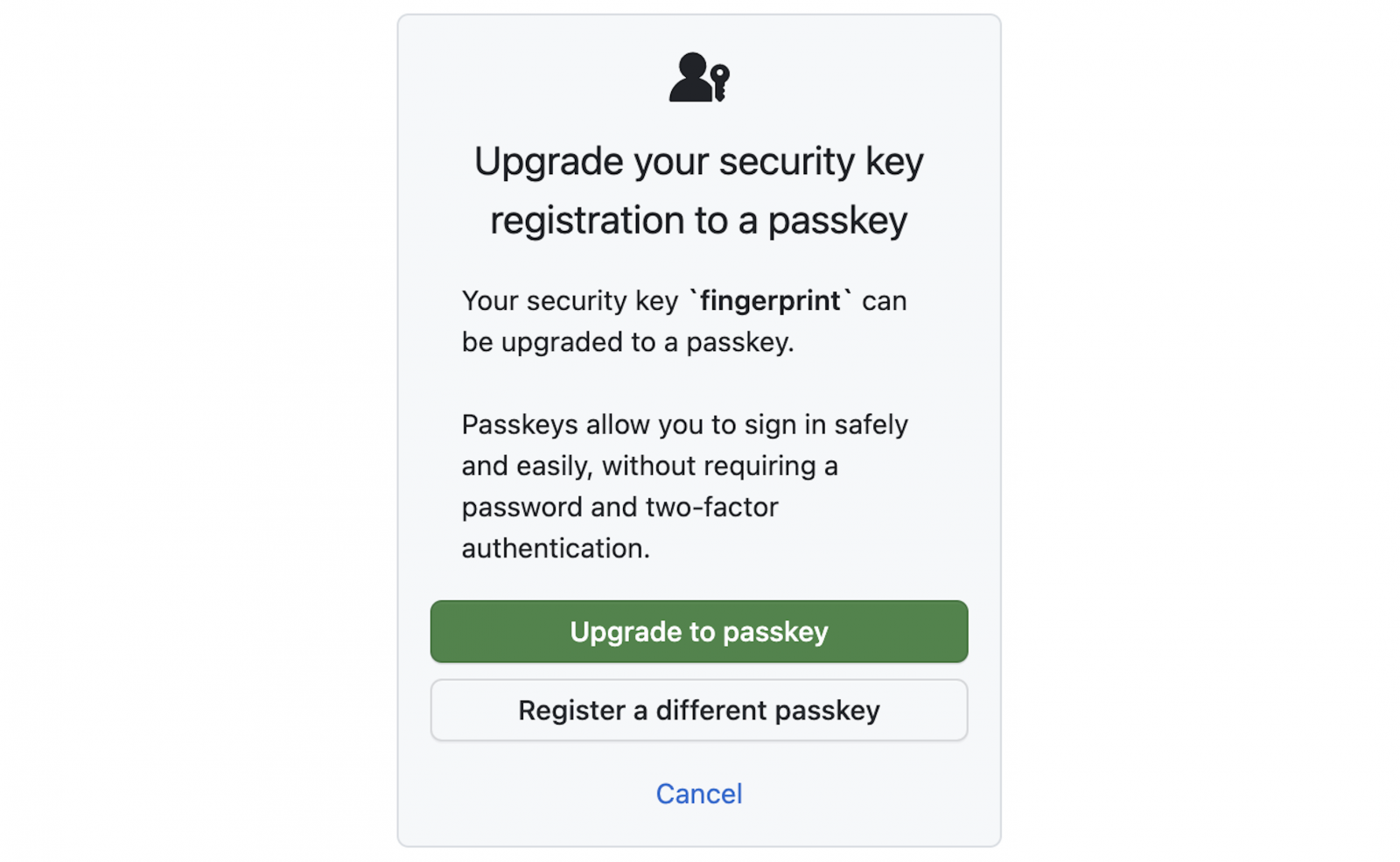
“The next time you log in with [a] security key, we will ask if you want to upgrade it to a security key, which will re-register it with your security key provider,” Singhal said.
“Because access keys maintain privacy, you may need to trigger your access key multiple times during this upgrade flow so that we can ensure that we are upgrading the correct credentials. identification. Once you’ve done that, you’re ready for a password-free experience.”
This is another step taken by GitHub to improve software supply chain security by moving away from basic password-based authentication.
Today’s announcement comes after GitHub made mandatory two-factor authentication (2FA) for all active developers using its platform starting March 13.
Previously the code hosting platform phasing out account passwords to authenticate Git operations and introduces device verification by email.
In November 2020, GitHub REST API password authentication disabled and introduced Support for FIDO2 security keys to secure Git SSH operations in May 2021.
Over the years, GitHub has strengthened its account security measures by implementing two-factor authentication And connection alerts, block the use of a compromised passwordAnd added support for WebAuthn.
“We’re excited to continue to provide more flexibility, reliability, and security in how you can authenticate with GitHub,” Singhal added on Wednesday.
In May, Google also announcement a rollout of passkey support for Google Accounts across all of its services and platforms to allow users to sign in to their accounts without entering a password or using two-step verification (2SV) .
Last month, Microsoft expanded passkey support in Windows 11 adding a built-in passkey manager for Windows Hello and making login more secure using biometric authentication.
[ad_2]
Source link
