[ad_1]

The Federal Security Service of the Russian Federation (FSB) has accused the United States and other NATO countries of launching more than 5,000 cyberattacks against critical infrastructure in the country since the start of 2022.
The agency claims to have taken timely measures to prevent these attacks from having negative consequences for Russia.
In addition, the FSB claims that these attacks come from Ukrainian territories, which are used to hide the true origin and identity of the perpetrators. At the same time, the attacks also involve the deployment of “new types of cyber weapons”.
“In the analysis of identified cyber threats, data was obtained indicating the use of Ukrainian territory by the United States and NATO countries to carry out massive cyber attacks against civilian objects in Russia,” reads- on in machine translation. FSB Statement.
“Currently, Ukraine’s network infrastructure is used by offensive cyber operations units of Western countries, allowing them to covertly use new types of cyber weapons.”
The FSB claims that despite numerous attacks presented as activities of “the computer army of Ukraine”, it was able to discern the involvement of pro-Western hacker groups such as “Anonymous”, “Sailens “, “Goast clan”, “Ji-En-Ji”, “SquadZOZ” and others.
The timing of this FSB statement is suspicious, as Poland’s military counterintelligence service and its computer emergency response team have linked APT29-backed Russian hackers to widespread attacks on several EU countries. EU and NATO. just yesterday.
Detections point to Chinese APTs
Meanwhile, Rostelecom’s CERT team also released a report on cyberattacks targeting Russian infrastructure between March 2022 and March 2023.
In this report, Rostelecom claims that 20% of all detected attacks can be attributed to sophisticated APT groups, 38% are cases of hacktivism and 38% are ransomware attacks.
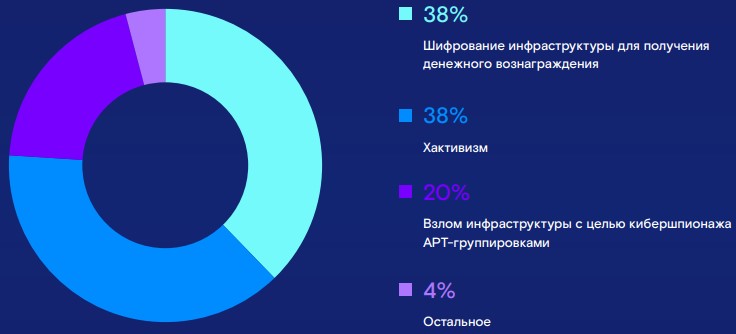
In 72% of detected cases, network intruders exploited known vulnerabilities for initial access, while the time to achieve their ultimate goal has now been reduced to an average of seven days.
“The activity of state-owned APT groups has grown, which since the start of the special military operation have become more active in infrastructure, expanding the range of objectives,” reads the automatic translation The Rostelecom report.
Interestingly, the four hacking groups reported by Rostelecom analysts to have the most activity against Russian entities during the mentioned period are APT27, APT41, APT10, all three believed to be of Chinese origin, and the Lazarus group, who are North Korean.
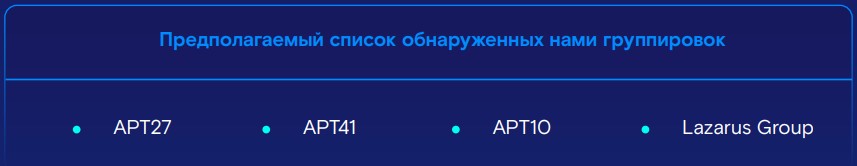
This directly contradicts the FSB statement regarding a massive wave of thousands of attacks launched by NATO-backed hacking collectives.
On the contrary, the country’s largest telecommunications provider reports that the highest volume of cyber espionage attacks come from Russia’s own perceived allies.
[ad_2]
Source link
