[ad_1]

Revolut suffered a cyberattack that gave an unauthorized third party access to the personal information of tens of thousands of customers.
The incident happened a week ago on Sunday evening and was described as “highly targeted”.
Founded in 2015, Revolut is a rapidly growing fintech company, now offering banking, fund management and investment services to customers around the world.
In a statement for BleepingComputer, a spokesperson for the company said an unauthorized party had access “for a short period” to the details of just 0.16% of its customers.
“We immediately identified and isolated the attack to effectively limit its impact and contacted affected customers. Customers who did not receive an email were not impacted” – Revolut
According to disclosure of the breach to the State Data Protection Inspectorate in Lithuania, where Revolut has a banking license, 50,150 customers were affected.
According to information from Revolut, the agency said that the number of affected customers in the European Economic Area is 20,687 and that only 379 Lithuanian citizens are potentially affected by this incident.
Details on how the threat actor gained access to the database were not disclosed, but it appears the attacker relied on social engineering.
The Lithuanian Data Protection Agency notes that information likely to be exposed includes:
- Email addresses
- Full names
- Postal addresses
- Phone numbers
- Limited payment card data
- Account data
However, in a message to a concerned customer, Revolut says the type of personal data compromised varies by customer. Card details, PINs or passwords have not been accessed.
Revolut points out that the intruder did not gain access to user funds.
“Our customers’ money is safe – just as it always has been. All customers can continue to use their cards and accounts as normal,” the company’s spokesperson told BleepingComputer.
The company reacted quickly to the intrusion and significantly limited the risk to its customers, isolating the attack by early Monday (2 a.m.).
As a precaution, Revolut has formed a dedicated team to monitor customer accounts, to ensure money and data are safe.
Users should be “extremely suspicious” of any message asking for personal information or passwords. Revolut will not call customers about the incident and will never ask for sensitive information.
Below is the full statement BleepingComputer received from a Revolut spokesperson:
Revolut recently suffered a highly targeted cyberattack. This allowed an unauthorized third party to access the details of a small percentage (0.16%) of our customers for a short period of time.
We immediately identified and isolated the attack to effectively limit its impact and contacted the affected customers. Customers who did not receive an email are not impacted.
To be clear, no funds were accessed or stolen. Our customers’ money is safe, as it always has been. All customers can continue to use their cards and accounts normally.
We take incidents like these extremely seriously, and would like to sincerely apologize to all customers who have been impacted by this incident, as the security of our customers and their data is our top priority at Revolut.
Some Revolut customers also noted at the time of the incident that the support chat displayed inappropriate language to visitors.
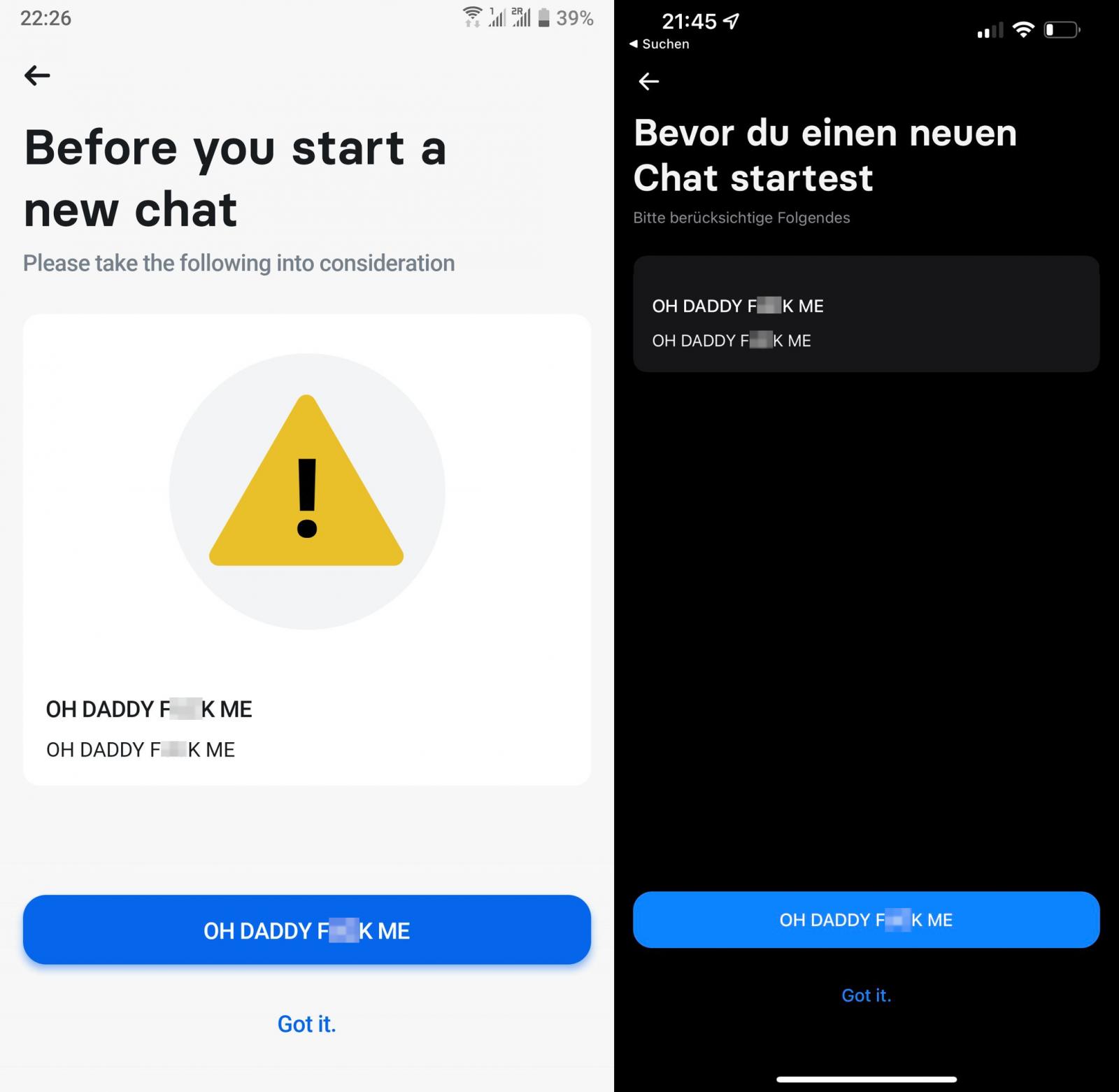
While it’s unclear whether this degradation is related to the breach disclosed by Revolut, it does show that hackers were able to gain access to a wider range of systems used by the company.
Revolut did not explain how or why users received these messages but apologized to reporting customers and said it was “resolving the issue and taking steps to ensure this doesn’t happen again.”
Phishers take advantage
This security incident is a good opportunity for phishers to trick any Revolut customer, even those not affected, into disclosing their sensitive information.
As first spotted by UCL”Report a smishingthere’s already an ongoing SMS phishing campaign trying to trick Revolut account holders with messages that their existing card has been frozen to prevent fraud.
To request a new card, victims are invited to click on the link “revolut-card-cancel[.]com”, where they will go through a four-step phishing process as shown below.
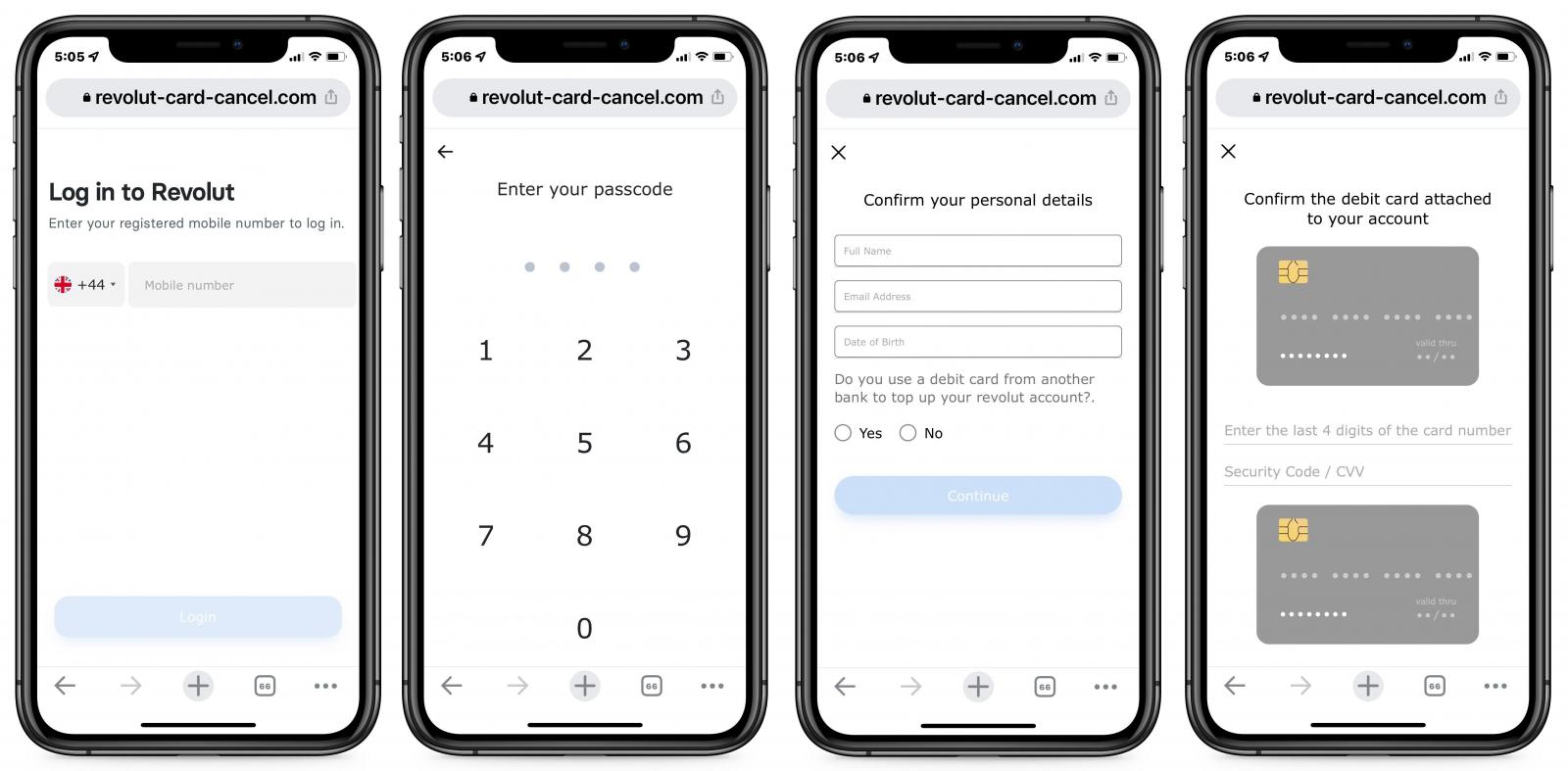
More importantly, threat actors attempt to steal complete payment card details, which allows them to make online purchases or send money to accounts under their control.
[ad_2]
Source link
