[ad_1]

Many people only associate the dark web with drugs, crime and leaked credentials, but in recent years a complex and interrelated cybercrime ecosystem has emerged on Tor and illicit channels on Telegram.
This trend can be illustrated by examining ransomware groupsaffiliates and the increasingly complex methods they use to extort businesses.
Ransomware has been an acute concern for organizations for over a decade, but one of the more recent trends we’ve seen is that groups are now building infrastructure, but outsourcing the actual infection (and in some cases negotiation) to “affiliates” who act effectively. as contractors to the Ransomware as a Service (RaaS) group and share the profits at the end of a successful attack.
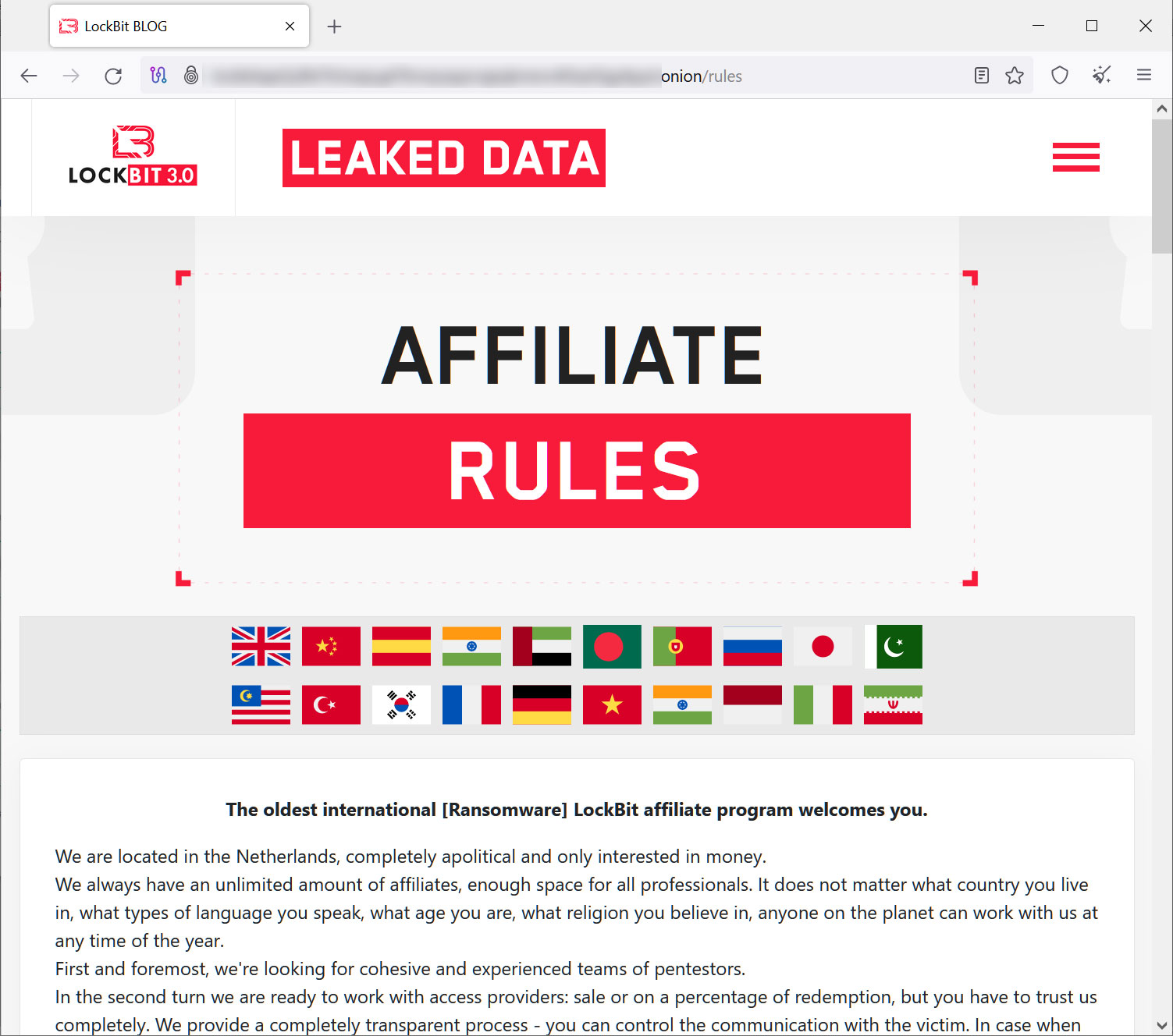
This allows the specialization of roles and the exploitation of the economic principle of “economies of scale”. This “commodification of cybercrime” allows more infections, more victims and higher payouts.
At the same time, we have seen groups resort to increasingly sophisticated extortion tactics. A group only encrypting a company’s data is now a rarity (one-time extortion), with some groups forgoing encryption entirely and instead focusing on exfiltrating data and blackmailing employees.
Different types of ransomware extortion
What are simple, double and triple extortion attacks?
Single extortion
This is your “traditional” ransomware attack where a group encrypts a company’s data and demands payment for releasing the data.
Double extortion
A ransomware group encrypts a company’s data, but first exfiltrates the data, which is posted on ransomware blogs on a certain date if the victim does not pay.

Triple extortion
Not only does the group encrypt and exfiltrate data, but it also attempts to:
- Target specific employees
- Conduct a DDoS attack on the company
- Notify third parties of the company
or otherwise attempts to create additional leverage to force the victim to pay.
How big is the threat of ransomware attacks?
In 2022, we saw 2,947 corporate data breaches on ransomware blogs. Undoubtedly, hundreds or thousands of other companies fell victim and paid the ransom to avoid data disclosure.
In 2023, we have already seen over 2,000 ransomware blog data leaks in the first six months of the year, making 2023 likely to be a peak year for ransomware data leaks.
How Triple Extortion Ransomware Exploits the Cybercrime Ecosystem
The rise of triple extortion ransomware also directly coincides with another significant change in the threat landscape: the rise of information-stealing malware.
Infostealer variants such as Vidar, Redline, and Raccoon infect individual computers and exfiltrate the browser’s fingerprint, host data, and most importantly, all credentials stored in the browser.
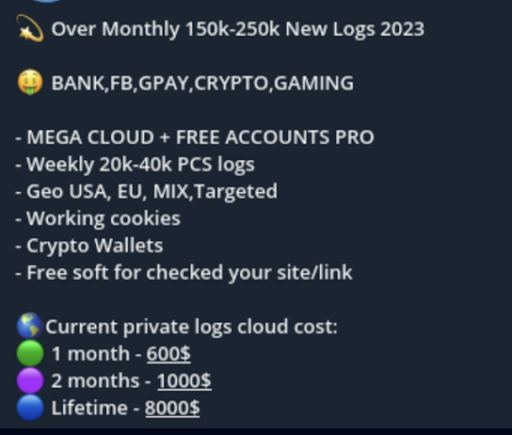
Ransomware affiliates can easily purchase ransomware through specialized forums and then seek initial access through infected device logs posted on public Telegram channels or offered for sale on Russian sites or Genesis Markets.
What’s in a Stealer Log?
An individual log can contain credentials for:
- VPN and business applications
- Online banks
- Retirement accounts
- Email addresses
- and more.
We estimate that there are at least 20 million infected devices for sale on the dark web and Telegram, with a single-digit percentage containing IDs from corporate environments.
Triple extortion attacks and theft logs
Ransomware groups can also use theft logs as part of triple extortion attacks.
We have seen affiliates use logs for initial access to corporate IT environments, as well as to identify logs already listed after a successful attack related to specific employees that can be exploited as a means to pressure the organization.
Ransomware and Initial Access Brokers
Another interesting convergence we’ve seen is the rapid increase in “initial access brokers” that operate on dark web forums and specialize in establishing initial access to a business, which is then sold in an auction to include a “buy it now price”.
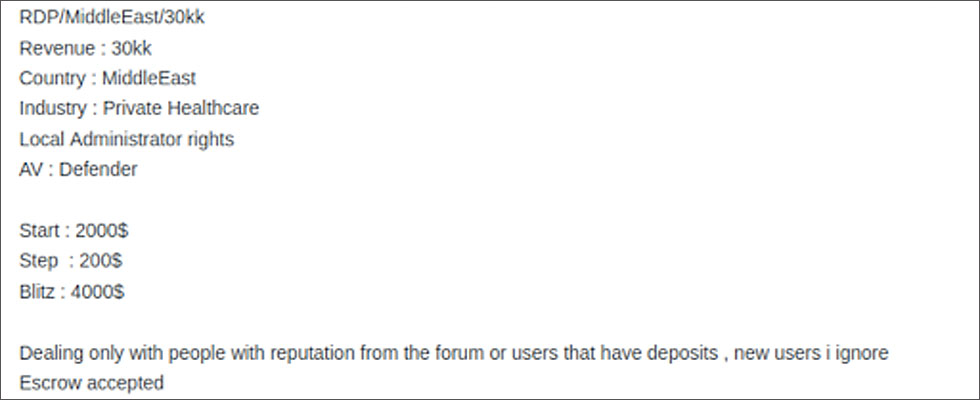
Initial access brokers further commoditize the infection process, allowing threat actors to easily purchase access to targets before ransomware is distributed and allowing them to do a number of “shopping” for the good target.
What does this mean for security teams?
The increasing complexity of the cybercrime ecosystem allows an increasing number of even unsophisticated malicious actors to launch sophisticated attacks against corporate environments. At Flare, we believe that having a Continuous Threat Exposure Monitoring (CTEM) process in place is the key to effective cybersecurity.
Gartner estimates that companies that leverage processes around CTEM will reduce the risk of a data breach by 66% in 2026.
All cyberattacks require an initial access vector. This can be achieved through traditional methods such as phishing emails and vulnerability exploits, but it can also come from developers leaking credentials on public GitHub repositories, infostealer malware infecting employee computers or credential stuffing attacks.
Protect against ransomware attacks with Flare
Flare automatically detects enterprise-specific threats across the light and dark web and illicit Telegram channels, integrates with your security program in 30 minutes, and provides early warning of potential high-risk exposure in a SaaS platform unique and easy to use.
We identify high-risk vectors that could allow threat actors to gain access to your environment and provide continuous monitoring of infected devices, ransomware exposure, GitHub public secrets leaks, information leaks. identification, etc.
Sign up for a free trial to learn more about protecting your organization.
Sponsored and written by To burst
[ad_2]
Source link
