[ad_1]

Tens of thousands of QNAP network-attached storage (NAS) devices are waiting to be patched against a critical security flaw patched by the Taiwanese company on Monday.
Remote hackers can exploit this SQL injection vulnerability (CVE-2022-27596) to inject malicious code into attacks targeting unpatched, internet-exposed QNAP devices.
QNAP has also assigned this bug a Baseline CVSS score of 9.8/10 and said it could be abused in low complexity attacks by unauthenticated malicious actors without requiring user interaction.
The company recommends that customers with affected devices (running QTS 5.0.1 and QuTS hero h5.0.1) upgrade to QTS 5.0.1.2234 build 20221201 or later and QuTS hero h5.0.1.2248 build 20221215 or later for protect against attacks.
To update your device, you need to log in as an administrator user, go to “Control Panel → System → Firmware Update”, click on the “Check for Update” option under the ” Live Update” and wait for the download and installation to complete.
Although QNAP has not marked this flaw as actively exploited in the wild, customers are advised to update to the latest available software version as soon as possible, as NAS devices have a long history of ransomware attacks.
Tens of Thousands of Unpatched Devices Exposed to Attacks
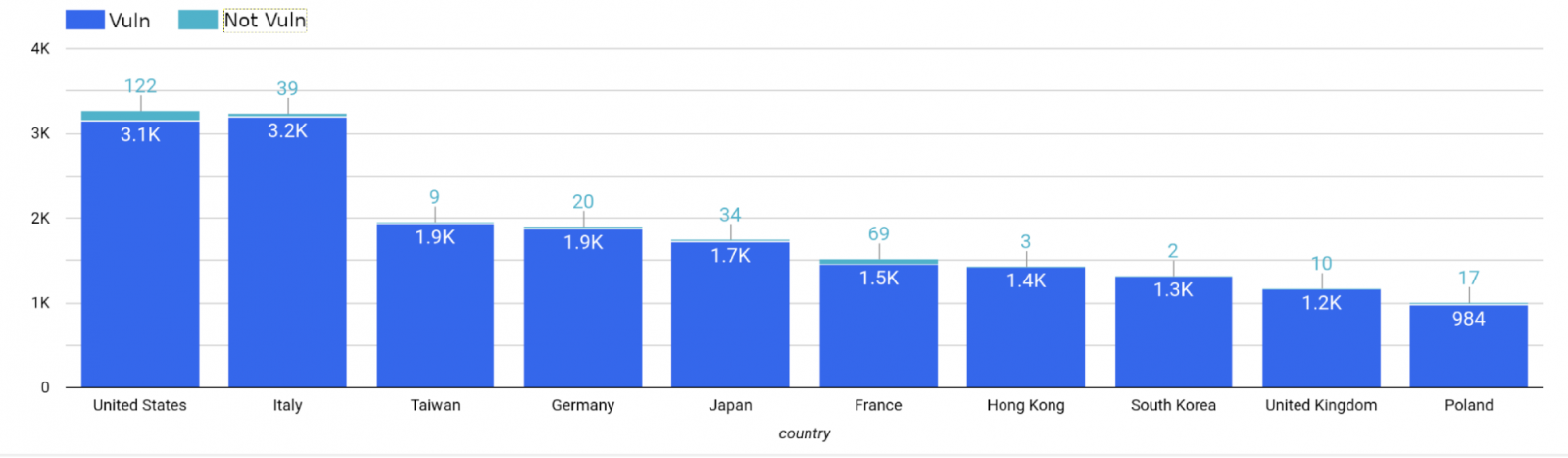
One day after QNAP released security updates To address this critical vulnerability, Censys security researchers released a report revealing that just over 550 of the more than 60,000 QNAP NAS devices they found online have been patched.
“Censys has observed 67,415 hosts with indications of running a QNAP-based system; unfortunately we were only able to get the version number of 30520 hosts. But, if the advisory is correct, over 98% of identified QNAP devices would be vulnerable to this attack,” said Mark Ellzey, Senior Security Researcher.
“We found that of the 30,520 hosts with a version, only 557 were running QuTS Hero greater than or equal to ‘h5.0.1.2248’ or QTS greater than or equal to ‘5.0.1.2234’, which means that 29,968 hosts could be affected by this vulnerability.”
Fortunately, since this flaw is yet to be exploited in the wild and proof-of-concept exploit code has yet to surface online, there is still time to fix these vulnerable NAS devices and fix them. protect against attacks.
Since these devices have been targeted by multiple strains of ransomware in recent years (including Muhstik, eCh0raix/QNAPCrypt, QSnatch, Agelocker, Qlocker, DeadBolt, and Checkmate), it bears repeating that QNAP customers should patch their device immediately NAS before threat actors pounce. and encrypt their files.
“If the exploit is released and weaponized, it could cause problems for thousands of QNAP users. Everyone should update their QNAP devices immediately to be safe from future ransomware campaigns,” added Elzey.
Apart from updating your NAS device as soon as possible, you should also consider not exposing it online to ensure that it is not accessible through the Internet for remote exploitation.
The NAS manufacturer has previously invited guests with devices exposed to the Internet to take the following steps to protect against inbound attacks:
- Disable the Port Forwarding feature of the router: Access your router’s management interface, check the virtual server, NAT, or port forwarding settings, and disable the port forwarding setting of the NAS management service port (ports 8080 and 433 by default).
- Disable the UPnP function of QNAP NAS: Go to myQNAPcloud in the QTS menu, click “Auto Router Configuration”, and deselect “Enable UPnP Port Forwarding”.
You should also disable SSH and Telnet connections, change the system port number, change device passwords, and enable IP and account access protection using these detailed step-by-step procedures.
[ad_2]
Source link
