[ad_1]

A new phishing campaign is exploiting security community members’ growing interest in Flipper Zero to steal their personal information and cryptocurrency.
Flipper Zero is a portable multifunctional cybersecurity tool for pen testers and hacking enthusiasts. The tool allows researchers to tinker with a wide range of hardware by supporting RFID emulation, digital passkey cloning, radio communications, NFC, infrared, Bluetooth, and more.
The developers launched the device after a massively successful 2020 Kickstarter Campaignwhich exceeded the fundraising goal of $60,000 by 81 times, after receiving $4,882,784 in pledges.
Since then, demonstrations by security researchers of Flipper Zero’s endlessly fun and somewhat creepy capabilities on social media have helped generate a lot of hype around the device, sparking the interest of aspiring hackers and researchers alike.
However, over the past year, the product has been hampered by production issues leading to supply shortages that have made it impossible to meet ever-increasing demand.
In September 2022, withholding of income by the PayPal digital payment platform jeopardize the project, jeopardizing its production by withholding $1.3 million earmarked for ordering new production batches.
Target cybersecurity researchers
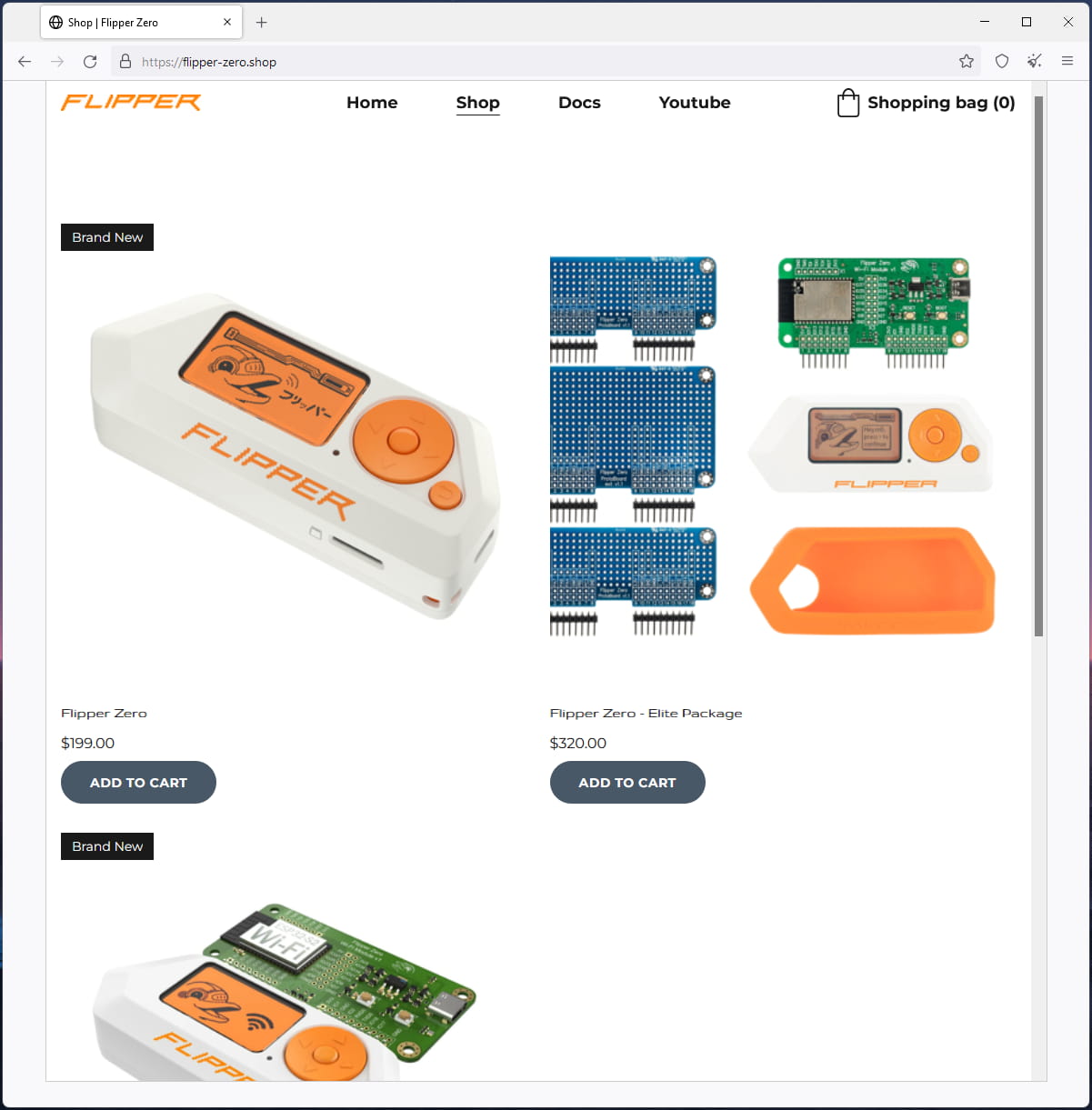
Threat actors are now taking advantage of the immense interest in Flipper Zero and its lack of availability by creating fake shops claiming to sell it.
These phishing campaigns were discovered by a security analyst Dominique Alvieriwho spotted three fake Twitter accounts and two fake Flipper Zero stores.
At first glance, one of the fake Twitter accounts appears to have the same ID as the official Flipper Zero account. However, in reality, he uses a capital “I” in the name, which looks like an “l” on Twitter.

Source: BleepingComputer
This fake Twitter account actively responds to people about the availability and tweets of other accounts to make it legit.
As of this writing, one of the fake shops remains online, claiming to sell Flipper Zero, the Wi-Fi module, and the case for the same price as the real shop.
Source: BleepingComputer
The goal is to take shoppers to the phishing checkout page, where they are prompted to enter their email addresses, full names, and shipping addresses.
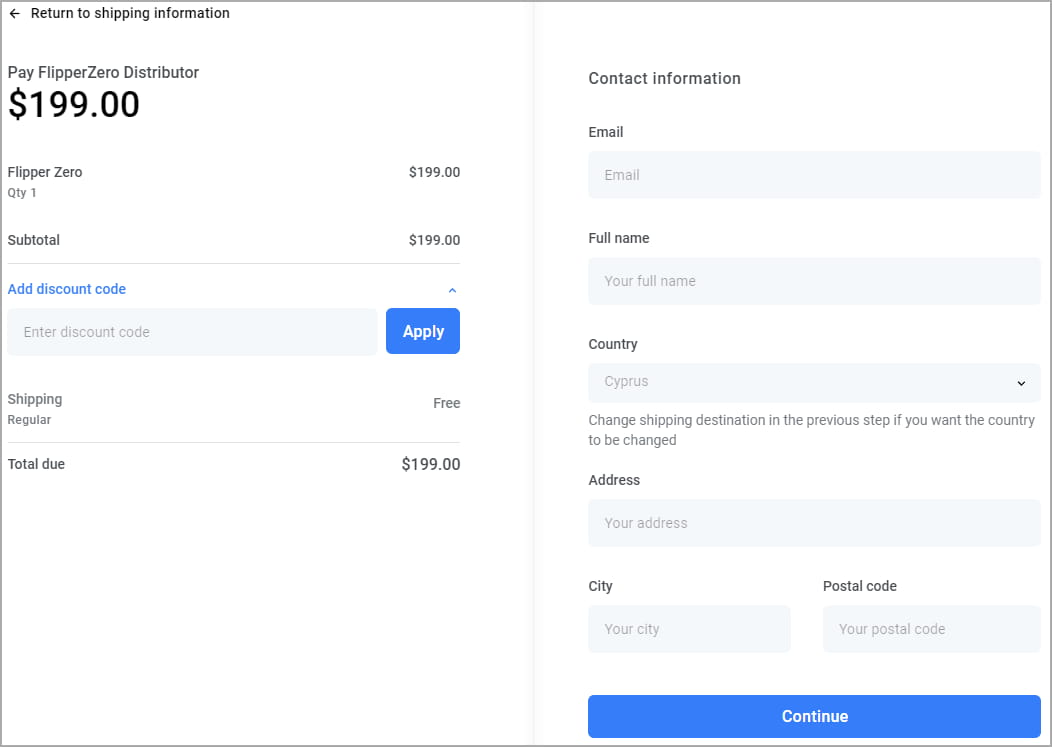
Source: BleepingComputer
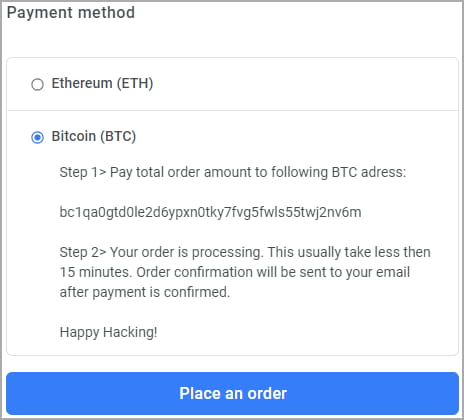
Victims then have the choice of paying using Ethereum or Bitcoin cryptocurrency and are informed that their order will be processed within 15 minutes of submission.
Source: BleepingComputer
The wallet addresses listed did not receive any payment, so the store in question either failed to fool security researchers or used new wallets after each transaction.
Threat actors have since switched to using plisio.net invoices to accept crypto payments, which now include Litecoin. However, these bills do not work, indicating that the command has expired.
As long as interest and shortages persist, cybercriminals keep trying impersonating Pinball Zero through fake shops to trick security enthusiasts into giving up their personal information and crypto.
Therefore, it is essential to be on the lookout for these promotions and shops claiming immediate availability of products and to buy only on the official store.
[ad_2]
Source link
