[ad_1]

More than 60,000 Microsoft Exchange servers exposed online have yet to be patched against remote code execution (RCE) vulnerability CVE-2022-41082, one of two security flaws targeted by ProxyNotShell exploits.
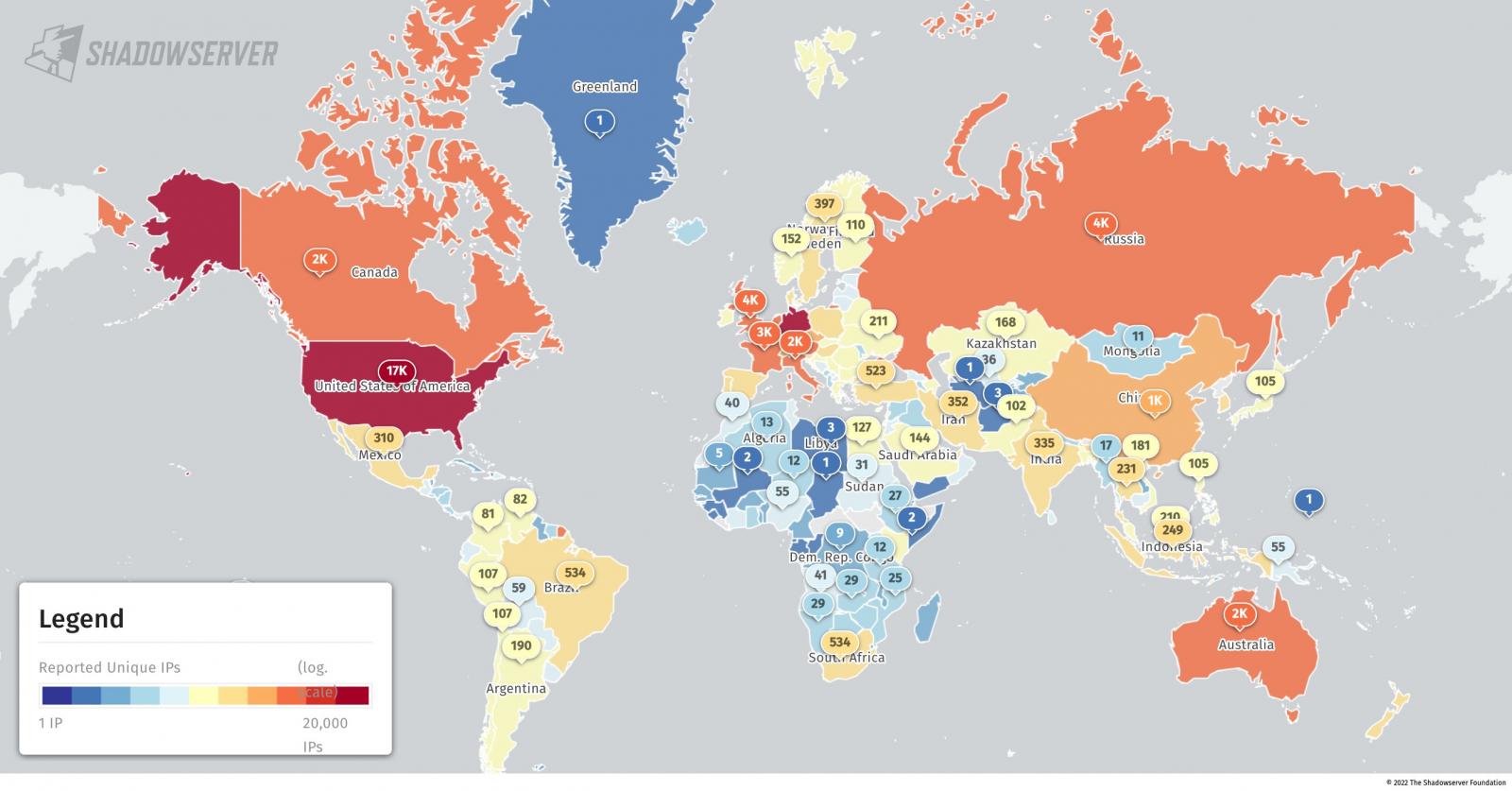
According to a recent tweet security researchers from the Shadowserver Foundation, a non-profit organization dedicated to improving Internet security, nearly 70,000 Microsoft Exchange servers have been found to be vulnerable to ProxyNotShell attacks according to version information (the header x_owa_version of the servers).
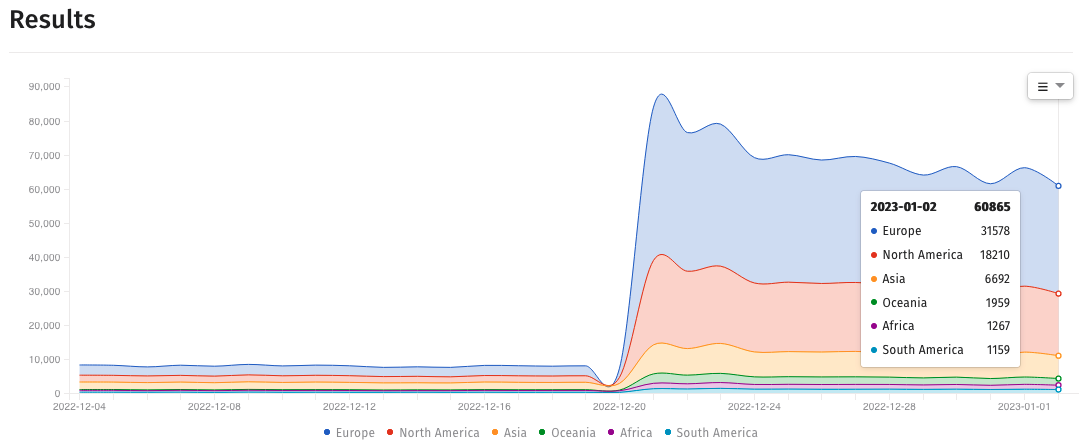
However, new data released on Monday shows that the number of vulnerable Exchange servers decreased from 83,946 cases in mid-December to 60,865 detected on January 2.
These two security bugs, tracked as CVE-2022-41082 and CVE-2022-41040 and collectively known as ProxyNotShell, affect Exchange Server 2013, 2016, and 2019.
If successfully exploited, attackers can elevate privileges and obtain arbitrary or remote code execution on compromised servers.
Microsoft has released security updates to fix vulnerabilities when November 2022 Patch Tuesdayeven if ProxyNotShell attacks have been detected in the wild since at least September 2022.
Threat intelligence firm GreyNoise has been tracking the ongoing exploitation of ProxyNotShell since September 30 and provides information on ProxyNotShell analysis activity and a list of attack-related IP addresses.
Thousands of people are also exposed to ProxyShell and ProxyLogon attacks
In order to protect your Exchange servers from incoming attacks, you must apply the ProxyNotShell patches released by Microsoft in November.
While the company has also provided mitigations, these can be circumvented by attackers, meaning only fully patched servers are safe from compromise.
As reported by BleepingComputer last month, Play ransomware threat actors are now using a new exploit chain to circumvent ProxyNotShell URL Rewrite Mitigation and achieve remote code execution on vulnerable servers through Outlook Web Access (OWA).
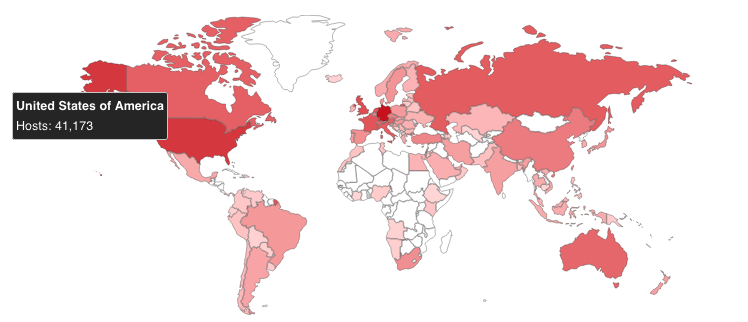
To make matters worse, a Shodan Research reveals significant number of Exchange servers exposed online, with thousands unpatched for ProxyShell and ProxyLogon vulnerabilities that have made their way into the Top most exploited vulnerabilities in 2021.
Exchange servers are valuable targets, as demonstrated by the financially motivated cybercrime group FIN7 which has developed a custom automated attack platform known as Checkmarks and designed to breach Exchange servers.
According to threat intelligence firm Prodaft, which discovered the platform, it searches for and exploits various Microsoft Exchange remote code execution and elevation of privilege vulnerabilities, such as CVE-2021-34473, CVE- 2021-34523 and CVE-2021-31207.
FIN7’s new platform has already been used to infiltrate 8,147 companies, mostly located in the US (16.7%), after scanning over 1.8 million targets.
[ad_2]
Source link
