[ad_1]

Okta, a leading provider of authentication services and identity and access management (IAM) solutions, said its private GitHub repositories were hacked this month.
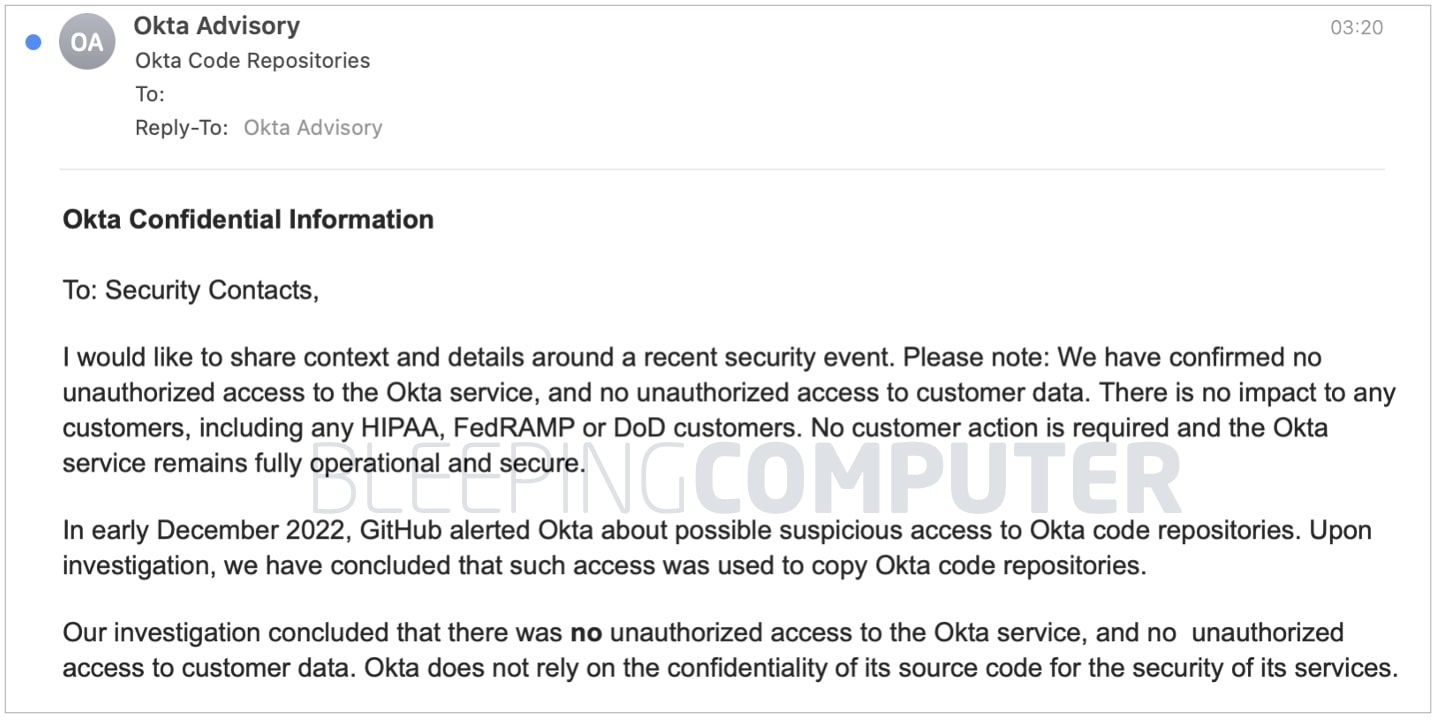
According to a “confidential” email notification sent by Okta and seen by BleepingComputer, the security incident involves threat actors stealing Okta’s source code.
Source code stolen, customer data not impacted
BleepingComputer obtained a “confidential” security incident notification which Okta emailed to its “security contacts” a few hours ago. We have confirmed that multiple sources, including IT admins, received this email notification.
Earlier this month, GitHub alerted Okta to suspicious access to Okta’s code repositories, the notification says.
“Upon investigation, we have concluded that such access was used to copy Okta code repositories,” David Bradbury, the company’s chief security officer (CSO), wrote in the email.
Despite stealing Okta’s source code, the attackers did not gain unauthorized access to the Okta service or customer data, the company says. Okta’s “HIPAA, FedRAMP, or DoD customers” are unaffected because the company “does not rely on the confidentiality of its source code to secure its services.” As such, no customer action is required.
At the time of writing, the incident appears to involve the Okta Workforce Identity Cloud (WIC) code repositories, but not the Auth0 Customer Identity Cloud product, given the wording of the email.
An excerpt from the remainder of the notification, reviewed by BleepingComputer, is posted below:
As soon as Okta became aware of the possible suspicious access, we quickly implemented temporary restrictions on access to Okta GitHub repositories and suspended all GitHub integrations with third-party applications.
We’ve since reviewed all recent accesses to GitHub-hosted Okta software repositories to understand the extent of exposure, reviewed all recent commits to GitHub-hosted Okta software repositories to validate the integrity of our code, and rotates GitHub credentials. We also notified law enforcement.
Additionally, we have taken steps to ensure that this code cannot be used to access corporate or customer environments. Okta does not anticipate any disruption to our business or our ability to serve our customers as a result of this event.
Note: The security event is for Okta Workforce Identity Cloud (WIC) code repositories. It does not concern any Auth0 (Customer Identity Cloud) product.
We have decided to share this information in accordance with our commitment to transparency and partnership with our customers.
While ending his “confidential” email which promises a “commitment to transparency”, Okta announces that he will release a statement today on his blog.
BleepingComputer contacted Okta with questions before publication, but a response was not immediately available.
Okta Security Incidents: Year in Review
It’s been a rough year for Okta with its string of bumpy security incidents and disclosures.
In September of this year, Auth0, owned by Okta revealed a similar style incident. According to the authentication service provider, the old Auth0 source code repositories were obtained by a “third-party individual” from their environment through unknown means. But Okta’s troubles began long before that, amid the irregularity surrounding the disclosure of its January hack.
March of this year data extortion group Lapsus$ claimed he had access to Okta admin consoles and customer data as it began posting screenshots of the stolen data on Telegram.
After stating that it was investigating these allegations, Okta quickly acknowledged that the hack referred to actually happened in late January 2022 and potentially reached 2.5% of its customers. This figure was estimated at around 375 organizations at the time, considering Okta’s customer base of over 15,000. at the time.
That same week, Okta admitted to “making a mistake” by delay disclosure of this hack which the company claims originated from its third-party contractor, Sitel (Sykes).
In April, Okta clarified that the January breach lasted “25 consecutive minutes” and the impact was significantly less than originally anticipated: limited to only two customers.
[ad_2]
Source link
