[ad_1]

The Korean National Police Agency (KNPA) has warned that North Korean hackers have hacked into the network of one of the country’s largest hospitals, Seoul National University Hospital (SNUH), to steal sensitive medical information. and personal details.
The incident happened between May and June 2021, and police have conducted an analytical investigation over the past two years to identify the perpetrators.
According to the law enforcement press release, the attack was attributed to North Korean hackers based on the following information:
- the intrusion techniques observed in the attacks,
- IP addresses that have been independently linked to North Korean threat actors,
- website registration details,
- the use of a specific language and North Korean vocabulary
Local media in South Korea linked the attack to the Kimsuky hacking group, but the police report does not explicitly mention the particular threat group.
The attackers used seven servers in South Korea and other countries to launch the attack on the hospital’s internal network.
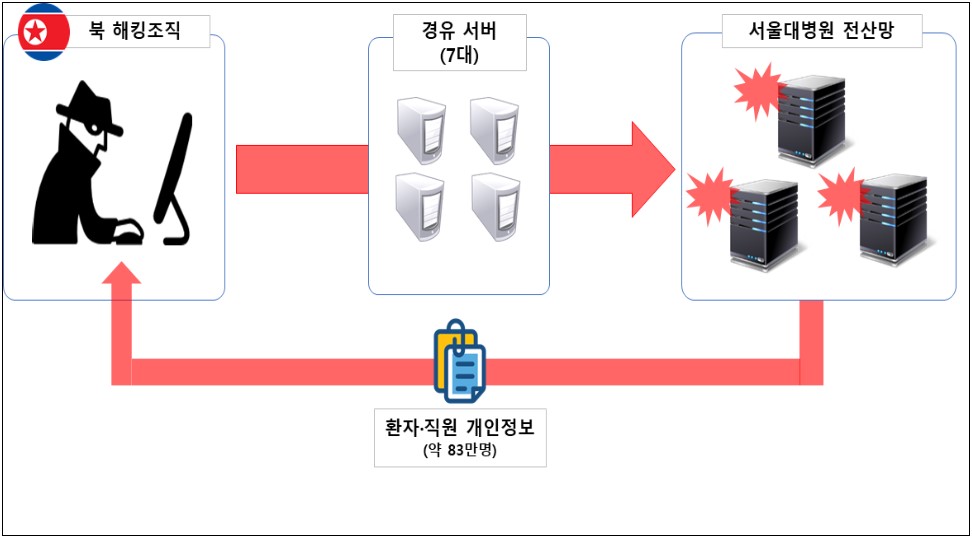
Police said the incident resulted in the data exposure of 831,000 people, most of whom were patients. Additionally, 17,000 of those affected are current and former hospital employees.
The KNPA press release warned that North Korean hackers may try to infiltrate information and communication networks in various industries. He highlighted the need for enhanced security measures and procedures, such as implementing security patches, managing system access and encrypting sensitive data.
“We plan to actively respond to organized cyberattacks supported by national governments by mobilizing all of our security capabilities and firmly safeguard South Korea’s cybersecurity by preventing further harm through information sharing and collaboration with relevant agencies. concerned”, warned the KNPA.
Maui and Andariel
North Korean hackers have previously been linked to hospital network intrusions aimed at stealing sensitive data and extorting ransom from healthcare organizations.
Specifically, the US government highlighted the Maui ransomware threat as such, warning the health sector they need to strengthen their defenses against the North Korean operation.
Shortly after this warning, Kaspersky security researchers related the Maui ransomware operation to a specific activity group named “Andariel” (aka “Stonefly”), considered a subgroup of Lazarus.
Lazarus is known to target South Korean entities with ransomware since April 2021.
[ad_2]
Source link
