[ad_1]

A new North Korean hacking group has been revealed to have targeted government organizations, academics and think tanks in the United States, Europe, Japan and South Korea for the past five years.
The moderately sophisticated threat actor is tracked as “APT43” and is believed to engage in financially motivated espionage and cybercrime operations that help fund his activities.
Mandiant analysts who first disclosed APT43’s activities believe with great confidence that the threat actors are state-sponsored, aligning their operational goals with the geopolitical goals of the North Korean government.
“Specifically, Mandiant assesses with moderate confidence that APT43 is attributable to North Korea’s Reconnaissance General Bureau (RGB), the country’s primary foreign intelligence service,” Mandiant’s new report explains.
Researchers have been tracking APT43 since late 2018, but only released more specific details about the threat group now.
APT43 espionage
APT43 has been observed to sharply focus on their spy operations, which is a sign that they are receiving orders on their targets, following the directions of larger strategic planning.
Over the years, he has targeted government offices, diplomatic organizations, think tanks, universities employing professors specializing in Korean Peninsula issues, and other critical organizations in South Korea, the United States, in Europe and Japan.
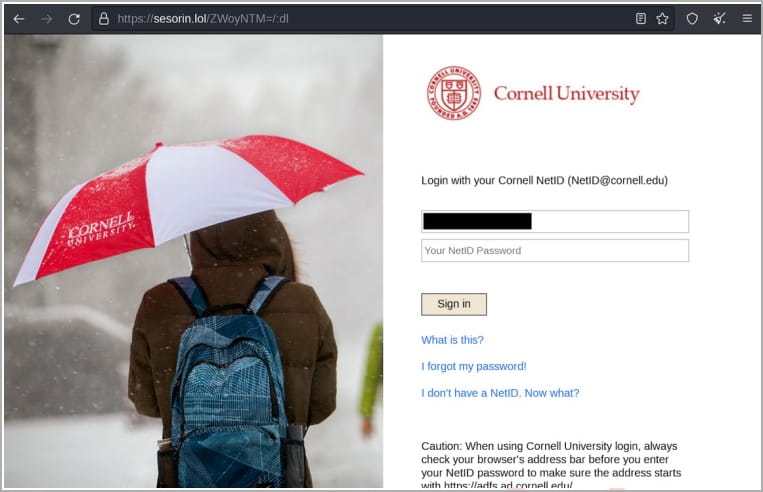
APT43 uses spear phishing emails from fake or spoofed people to approach their targets, sending them to websites posing as legitimizing entities. However, these websites contain fake login pages where victims are tricked into entering their account credentials.
After stealing these credentials, APT43 logs in as the target to perform the intelligence gathering itself. They also use the victim’s contacts to further their phishing activities to other brands.
“The group is primarily interested in information developed and stored within the U.S. military and government, the Defense Industrial Base (DIB), and research and security policies developed by U.S. universities and think tanks. focused on nuclear security policy and non-proliferation”, explains the Mandatory Report.
“APT43 has shown interest in similar industries in South Korea, especially nonprofit organizations and universities that focus on global and regional policies, as well as businesses, such as manufacturing, that can provide information on goods whose export to North Korea has been restricted.”
Examples of such goods include weapons, transport vehicles, machinery, fuel and metals.
Financing its own operations
APT43 employs a strategy similar to most North Korean threat groups that operate independently of state funding. Instead, they are expected to maintain their business through finance-based cyber operations.
Mandiant observed APT43 using malicious Android apps that target Chinese users seeking cryptocurrency loans and instead lose their digital assets to threat actors.
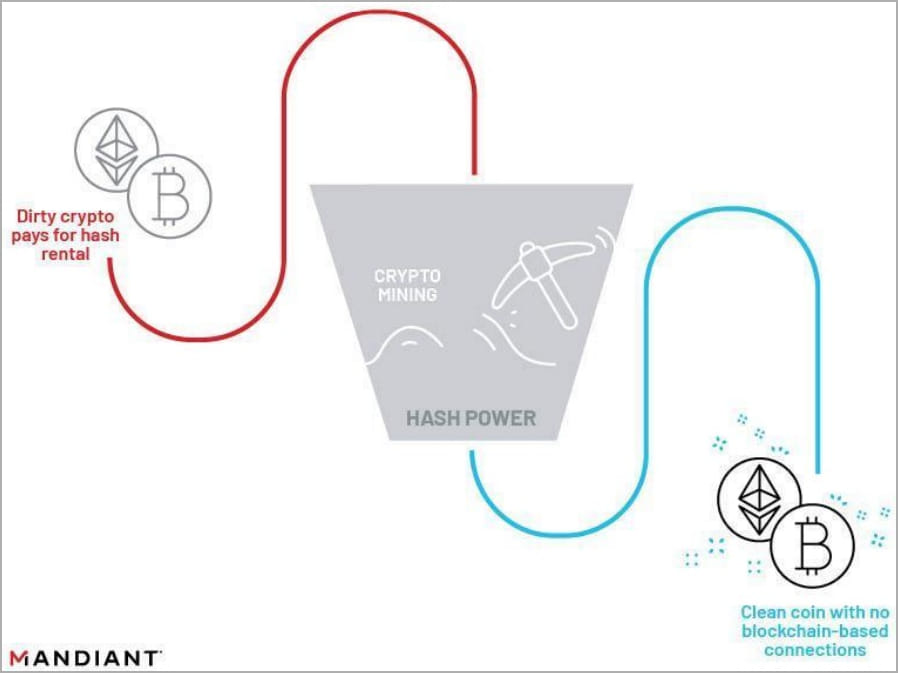
Cryptocurrency stolen by APT43 is laundered through hash rental and cloud mining services using numerous aliases, addresses and payment methods.
Hash rental allows customers to rent computing power for cryptocurrency mining, which can be paid for in crypto. Mandiant says APT43 uses these services to launder stolen cryptocurrency so it cannot be traced to malicious operations.
Mandiant reports seeing the group pay for hardware and infrastructure with PayPal, American Express cards and Bitcoin, all likely stolen from the victims.
Malware and Korean overlap
Mandiant reports that other researchers in the past have spotted APT43 activity, but it was generally attributed to Kimsuky or Thalium.
Additionally, APT43 was seen using malware during the COVID-19 pandemic that the hacking group Lazarus is also using, but this overlap was short-lived.
In another instance, the threat group used the “Lonejogger” crypto-stealing tool which was associated with the UNC1069 threat actor, which may be connected to APT38.
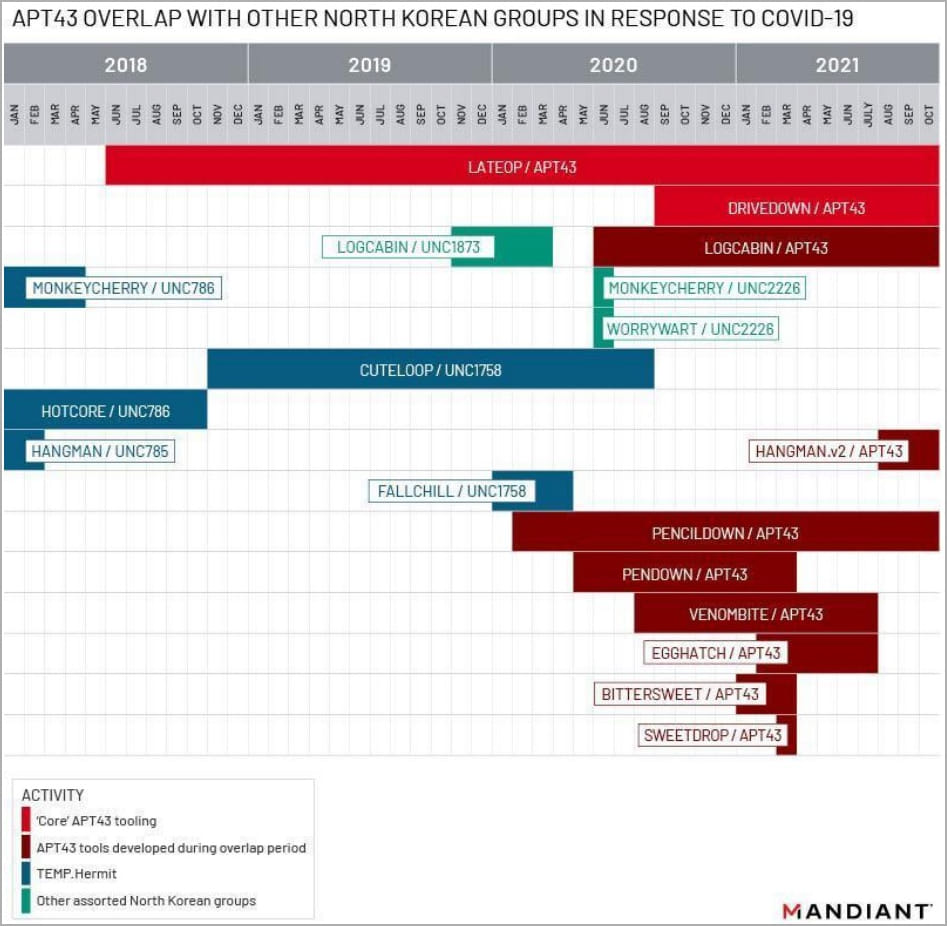
APT43 also has its own set of custom malware not used by other threat actors, such as “Pencildown”, “Pendown”, “Venombite” and “Egghatch” downloaders, “Logcabin” and “Lateop” tools ( “BabyShark”). , and the “Hanged Man” backdoor.
Apart from these, the threat group has also deployed publicly available tools such as “gh0st RAT”, “QuasarRAT” and “Amadey”.
Mandiant expects APT43 to continue to be a very active threat group unless North Korea changes its domestic priorities.
[ad_2]
Source link
