[ad_1]

Technical information has emerged for a serious vulnerability affecting several versions of the Linux kernel that could be triggered with “minimal capabilities”. The security issue is called StackRot (CVE-2023-3269) and can be used to compromise the kernel and elevate privileges.
A patch has been available for affected stable kernels since July 1, and full details of the issue and full exploit code are expected by the end of the month.
Security researcher Ruihan Li discovered and reported the vulnerability. He explains in an article today that this affects the kernel’s memory management subsystem, a component responsible for implementing virtual memory and on-demand paging, memory allocation for kernel needs and user space programs, as well as file mapping in process address. space.
StackRot impacts all kernel configurations on Linux versions 6.1 through 6.4.
Although Li submitted the vulnerability report on June 15, creating a patch took nearly two weeks due to its complexity, and Linus Torvalds led the effort.
“On June 28, during the Linux 5.5 kernel merge window, the patch was merged into the Linus tree. Linus provided a full merge post to elucidate the patch suite from a technical perspective. These fixes were later backported to stable kernels (6.1.37, 6.3.11, and 6.4.1), effectively fixing the “Stack Rot” bug on July 1,” the researcher clarified.
StackRot Details
StackRot stems from the Linux kernel’s handling of stack expansion within its memory management subsystem, related to the management of Virtual Memory Areas (VMAs).
Specifically, the weak point is in the “maple tree”, a new data structure system for VMAs introduced in Linux kernel 6.1 that replaced “red-black trees” and relied on the read-copy-update (RCU) mechanism.
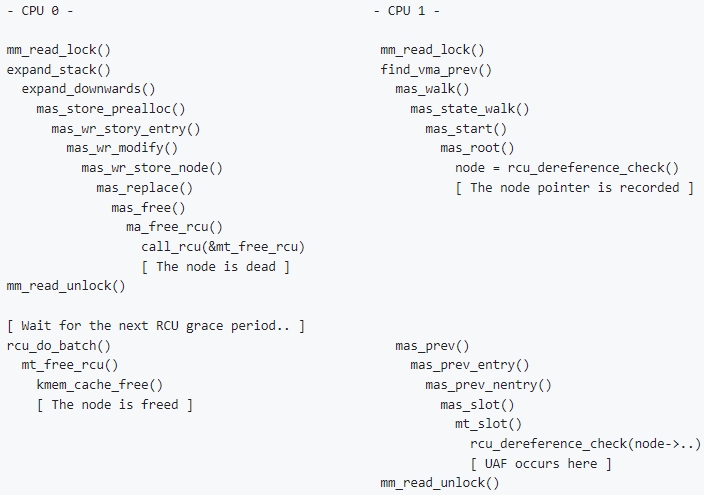
The vulnerability is a use-after-free (UAF) issue resulting from the way stack expansion was handled, as the maple tree could overwrite a node without obtaining the memory management write lock (MM).
As the Linux kernel extends the stack and removes the gap between VMAs, a new node is created in the “maple tree” and the old one is marked for deletion once the current reads are complete due to the maple tree’s RCU security.
However, during the RCU grace period, a use-after-free issue can occur when a process accesses the old node, creating an exploitable context to elevate privileges.
Coming feat
Ruihan Li notes that exploiting StackRot is a difficult task and that CVE-2023-3269 could be the first example of a theoretically exploitable RCU use-after-release (UAFBR) vulnerability.
However, the researcher has announced plans to release full technical details about StackRot and a proof-of-concept (PoC) exploit by the end of July.
The Linux 6.1 kernel has been approved as a Long Term Support (LTS) release since February. However, not all major Linux distributions have adopted it.
For example, Ubuntu 22.04.2 LTS (Jammy Jellyfish), which ends mainstream support in April 2027, ships with Linux kernel version 5.19. On the other hand, Debian 12 (Bookworm) comes with Linux kernel 6.1.
A complete list of Linux distributions using kernel version 6.1 or higher is available at DistroWatch.
Users should check the kernel version their Linux distribution is running on and choose one that is unaffected by StackRot or an updated version that contains the patch.
[ad_2]
Source link
