[ad_1]

A new Python-based credential harvesting and SMTP hacking tool named “Legion” is being sold on Telegram that targets online messaging services for phishing and spam attacks.
Legion is sold by cybercriminals who use the moniker “Forza Tools” and operate a YouTube channel with tutorials and a Telegram channel with over a thousand members.
Legion is modular malware that Cado says is likely based on the AndroxGhOst malware and offers modules to perform SMTP server enumeration, remote code execution, exploit vulnerable versions of Apache, force cPanel and WebHost Manager accounts, interact with Shodan’s API, and abuse AWS services.
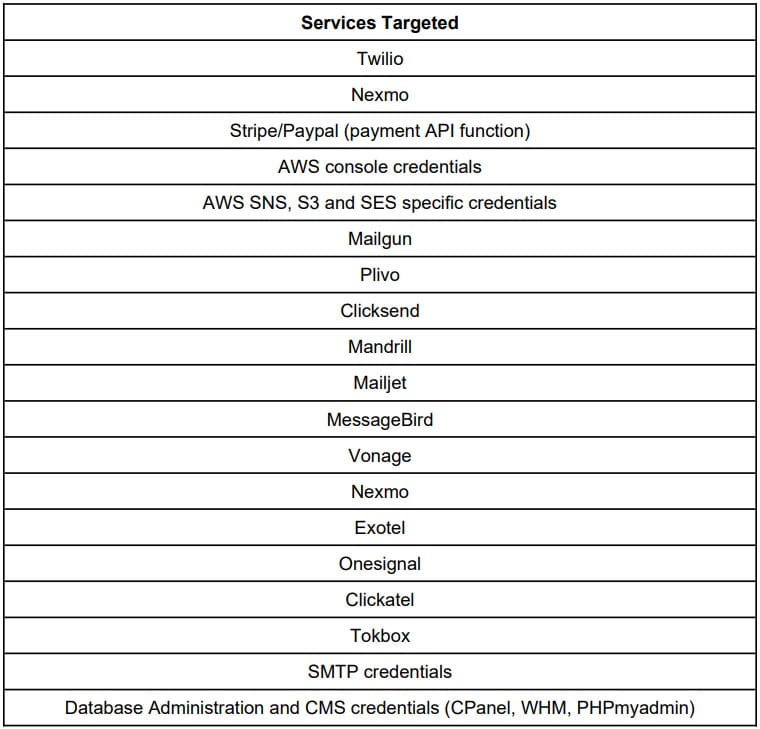
The tool targets numerous services for credential theft, including Twilio, Nexmo, Stripe/Paypal (payments API feature), AWS Console Credentials, AWS SNS, S3, and SES specific, Mailgun and database/CMS platforms.
Besides extracting credentials and breaching web services, Legion can also create admin users, implant webshells, and send spam text messages to US carrier customers.
Harvest IDs
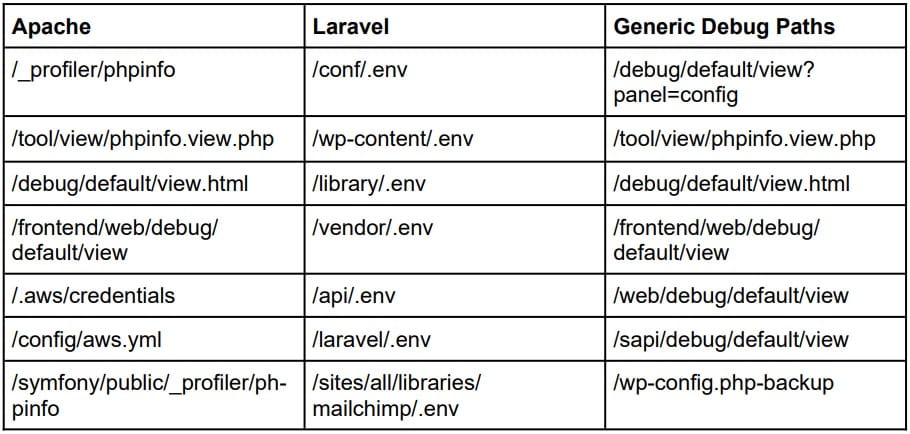
Legion typically targets insecure web servers running content management systems (CMS) and PHP-based frameworks like Laravel using RegEx patterns to search for files known to contain secrets, authentication tokens, and API keys .
The tool uses an array of methods to recover credentials from misconfigured web servers, such as targeting environment variable files (.env) and configuration files that may contain SMTP credentials, AWS console, Mailgun, Twilio and Nexmo.
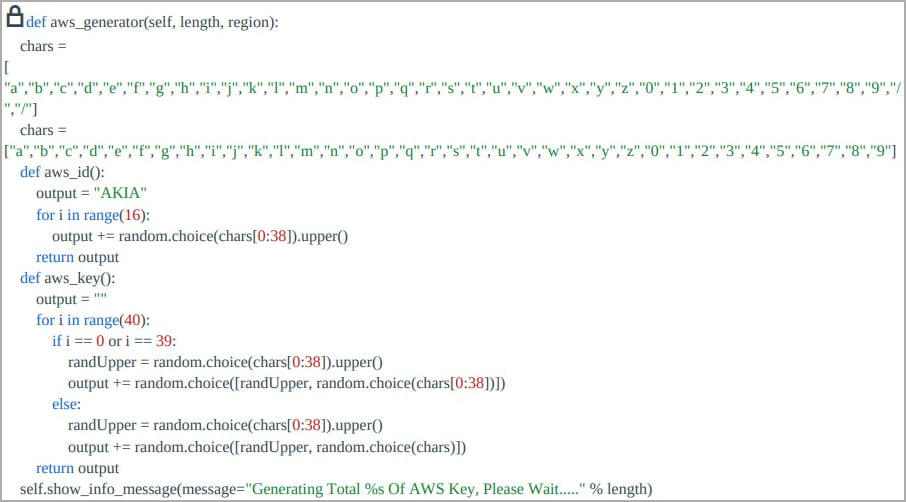
In addition to attempting to harvest AWS credentials, Legion also offers a brute force system to guess them.
However, Cado comments that it is statistically unlikely that this system can generate usable credentials in its current state. Similar functionality is included for brute forcing SendGrid credentials.
Regardless of how credentials are obtained, Legion will use them to access email services and send spam or phishing emails.
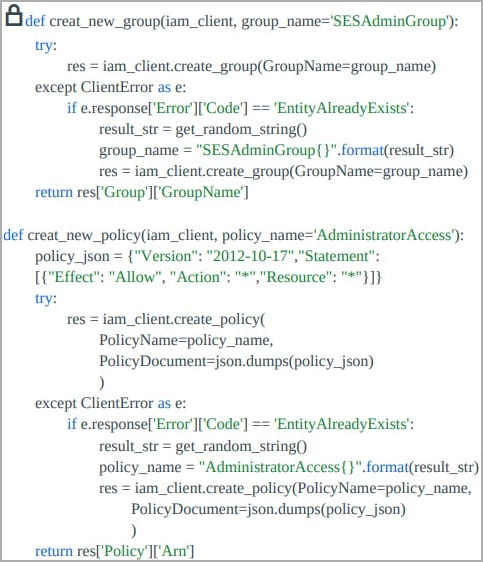
If Legion captures valid AWS credentials, it attempts to create an IAM user named “ses_legion” and sets the policy to give them admin rights, giving the attacker full access to all services and resources AWS.
Legion can also send SMS spam by exploiting stolen SMTP credentials after generating a list of phone numbers with area codes retrieved from online services.
Carriers supported by the malware include AT&T, Sprint, US Cellular, T-Mobile, Cricket, Verizon, Virgin, SunCom, Alltel, Cingular, VoiceStream, etc.
Finally, Legion can exploit known PHP vulnerabilities to register a webshell on the targeted endpoint or execute code remotely to give the attacker full access to the server.
In conclusion, Legion is a versatile credential harvester and hacking tool that is gaining traction in the world of cybercrime, increasing the risk of mismanaged and misconfigured web servers.
AWS users should look for signs of compromise, such as changing the IAM user registration code to include an “Owner” tag with the value “ms.boharas”.
[ad_2]
Source link
