[ad_1]
A new ransomware operation dubbed “Dark Power” has emerged, and it has already listed its first victims on a dark web data leak site, threatening to release the data if a ransom is not paid.
The ransomware gang’s encryptor has a compile date of January 29, 2023, when the attacks began.
Moreover, the operation has not yet been promoted on hacker forums or dark web spaces; it is therefore probably a private project.
According Trelliswho analyzed Dark Power, it is an opportunistic ransomware operation that targets organizations around the world, demanding relatively low ransom payments of $10,000.
Dark Power Attack Details
The Dark Power payload was written in Nim, a cross-platform programming language with several speed-related advantages, making it suitable for performance-critical applications like ransomware.
Moreover, since Nim is only starting to become more popular among cybercriminals, it is generally considered a niche choice that is unlikely to be detected by defense tools.
Trellix does not provide details regarding the Dark Power infection point, but it could be an exploit, phishing emails, or other means.
Upon execution, the ransomware creates a 64-character long random ASCII string to initialize the encryption algorithm with a unique key each time it is executed.
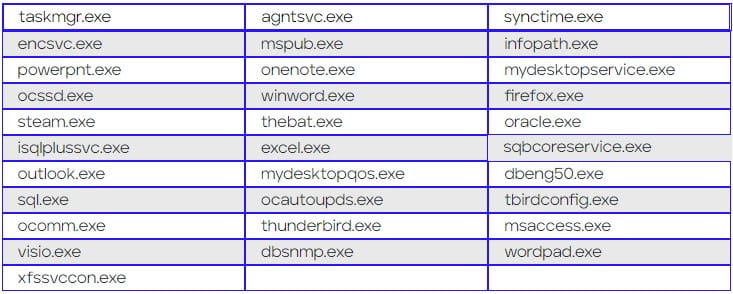
Then the ransomware terminates specific services and processes on the victim’s machine to free up files for encryption and minimize the chances of anything blocking the file-locking process.
During this stage, the ransomware also stops Volume Shadow Copy Service (VSS), data backup services and anti-malware products in its hardcoded list.
After all the above services are removed, the ransomware sleeps for 30 seconds and wipes Windows console and system logs to prevent analysis by data recovery experts.
The encryption uses AES (CRT mode) and the ASCII string generated at launch. The resulting files are renamed with the “.dark_power” extension.
Interestingly, two versions of the ransomware have been circulating in the wild, each with a different encryption key scheme.
The first variant hashes the ASCII string with the SHA-256 algorithm, then splits the result into two halves, using the first as the AES key and the second as the initialization (nonce) vector.
The second variant uses the SHA-256 digest as the AES key and a fixed 128-bit value as the encryption nonce.
Critical system files such as DLLs, LIBs, INIs, CDMs, LNKs, BINs, and MSIs, as well as program files and web browser folders, are excluded from encryption to keep the computer infected operational, thus allowing the victim to view the ransom note and contact the attackers.
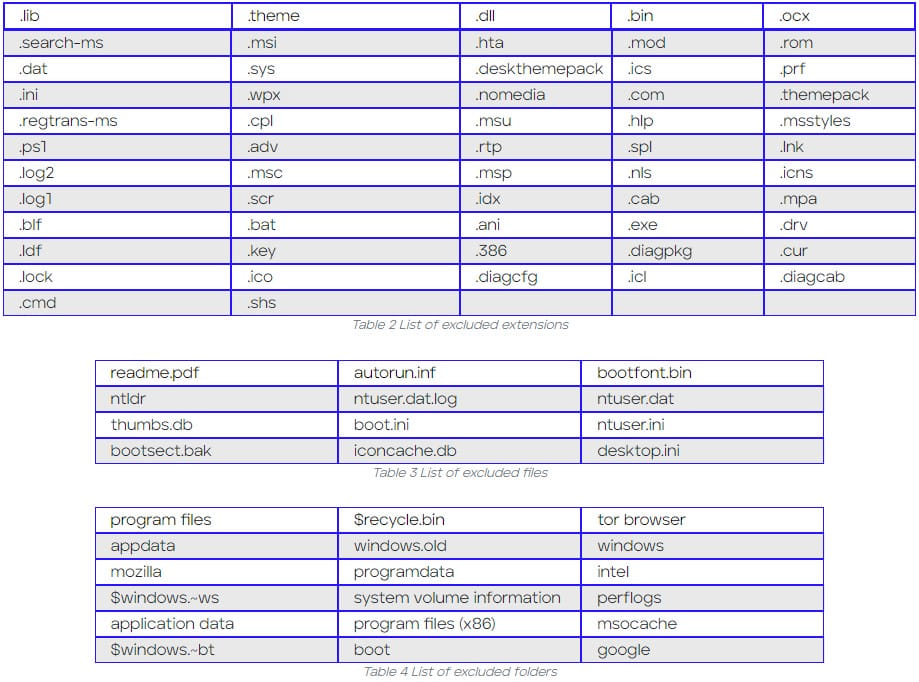
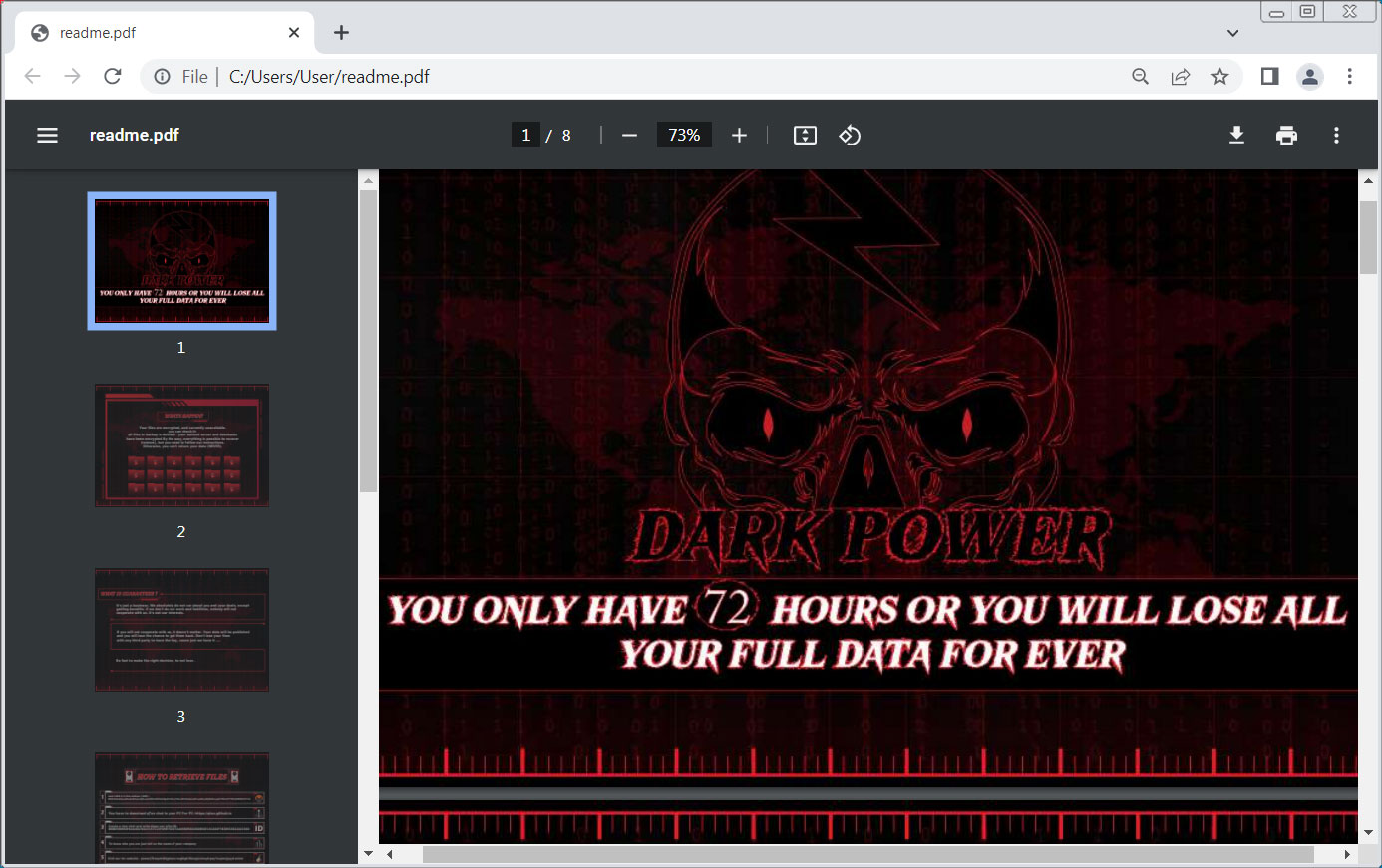
The ransom note, which was last modified on February 9, 2023, gives victims 72 hours to send $10,000 in XMR (Monero) to the provided wallet address to get a working decryptor.
The Dark Power ransom note stands out compared to other ransomware operations because it is an 8-page PDF document containing information about what happened and how to contact them through the qTox messenger.
Victims and activity
As of this writing, Dark Power’s Tor site is offline. However, it is not uncommon for ransomware portals to go offline periodically as negotiations with victims develop.
Trellix reports that he saw ten victims from the United States, France, Israel, Turkey, Czech Republic, Algeria, Egypt and Peru, so the reach of the targeting is global.
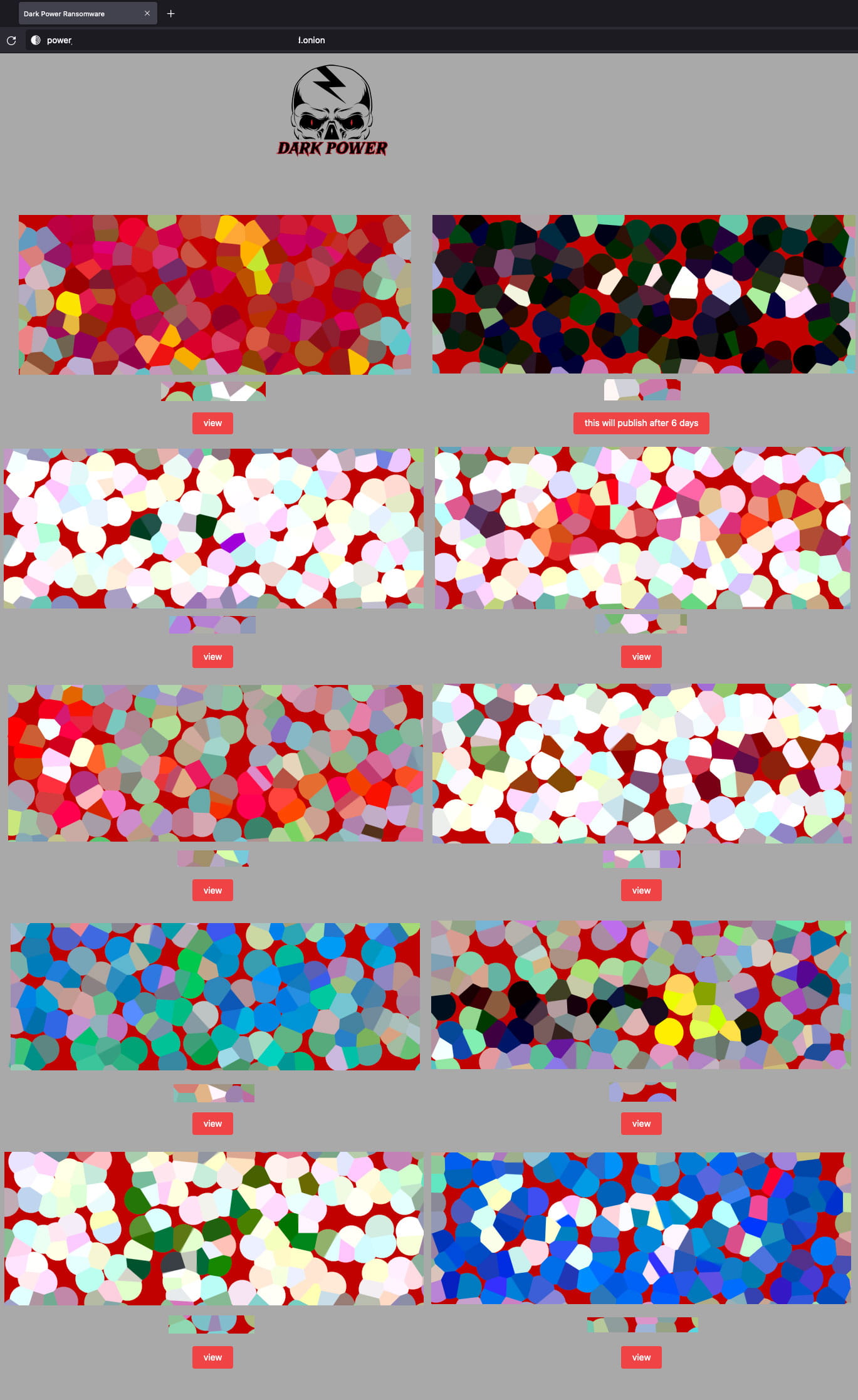
The Dark Power group claims to have stolen data from the networks of these organizations and is threatening to release it if they don’t pay the ransom, so this is yet another double extortion group.
[ad_2]
Source link
