[ad_1]

Citrix is today notifying customers of a Critical Severity Vulnerability (CVE-2023-3519) in NetScaler ADC and NetScaler Gateway that already has exploits in the wild, and “urges” to install updated versions without time limit.
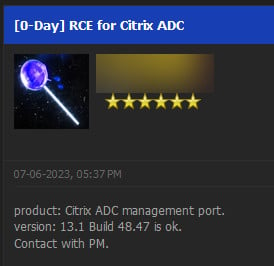
The security issue may be the same one announced earlier this month on a hacker forum as a zero-day vulnerability.
Mandatory patch
Formerly Citrix ADC and Citrix Gateway, both NetScaler products received new releases today to mitigate a set of three vulnerabilities.
The most severe of these received a score of 9.8 out of 10 and is being tracked as CVE-2023-3519. An attacker can exploit it to execute code remotely without authentication.
For hackers to exploit the security issue in attacks, the vulnerable appliance must be configured as a gateway (VPN virtual server, ICA proxy, CVPN, RDP proxy) or as an authentication virtual server (known as an AAA server ).
In a safety bulletin Today, Citrix reports that “exploits of CVE-2023-3519 on non-mitigated appliances have been observed” and strongly advises customers to upgrade to an updated version that fixes the issue:
- NetScaler ADC and NetScaler Gateway 13.1-49.13 and later
- NetScaler ADC and NetScaler Gateway 13.0-91.13 and later versions of 13.0
- NetScaler ADC 13.1-FIPS 13.1-37.159 and later versions of 13.1-FIPS
- NetScaler ADC 12.1-FIPS 12.1-65.36 and later versions of 12.1-FIPS
- NetScaler ADC 12.1-NDcPP 12.1-65.36 and later versions of 12.1-NDcPP
The company notes that NetScaler ADC and NetScaler Gateway version 12.1 have reached the end-of-life phase and customers should upgrade to a newer variant of the product.
Citrix 0day on the hacker forum
During the first week of July, someone announced on a hacker forum a zero-day vulnerability for Citrix ADC. The details are too few to definitively tie it to the Citrix Security Bulletin today, but the small clues available seem to point it.
The author of the post said on July 6 that they have zero-day remote code execution that would have worked for Citrix ADC versions up to 13.1 build 48.47.
BleepingComputer also received a tip some time ago that Citrix learned of a zero-day advertisement on a cybercrime forum and was working on a fix before disclosing the issue.
Defenders with knowledge of the issue said they expect active exploits to continue until Citrix releases a patch.
Organizations can start investigating if they have been compromised by looking for web shells newer than the last install date.
HTTP error logs can also reveal anomalies that could indicate an initial exploit. Administrators can also check shell logs for unusual commands that may be used in the post-operation phase.
XSS and privilege escalation
The updates also include fixes for two other vulnerabilities identified as CVE-2023-3466 and CVE-2023-3467. Both have a high severity score of 8.3 and 8, respectively.
CVE-2023-3466 is a thoughtful cross-site scripting (XSS) issue that can be exploited if a victim loads an attacker’s link in the browser and the vulnerable appliance is accessible from the same network.
Citrix lists CVE-2023-3467 as a vulnerability that allows an attacker to elevate privileges to those of a root (nsroot) administrator.
Exploitation of this flaw requires authenticated access to the NetScaler appliances IP address (NSIP) or subnet IP (SNIP) with access to the management interface.
As of this writing, technical details on the three vulnerabilities are not publicly available, but organizations with NetScaler ADC and Gateway appliances should prioritize updating them.
[ad_2]
Source link
