[ad_1]

A new Android malware named “Hook” is being sold by cyber criminals, boasting that it can take control of mobile devices remotely in real time using VNC (virtual network computing).
The new malware is promoted by the creator of Ermaca $5,000/month Android banking trojan that helps threat actors steal credentials from over 467 banking and crypto apps through overlaid login pages.
While Hook’s author claims the new malware was written from scratch, and despite several additional features over Ermac, ThreatFabric researchers dispute these claims and report seeing a lot of code overlap between the two families .
ThreatFabric explains that Hook contains most of Ermac’s codebase, so it’s still a banking Trojan. At the same time, it includes several useless parts found in the old stub that indicate that it reused code en masse.
More Dangerous Android Malware
Despite its origin, Hook is an evolution of Ermac, offering a full set of features that make it a more dangerous threat for Android users.
A new feature of Hook compared to Ermac is the introduction of WebSocket communication which comes on top of the HTTP traffic used exclusively by Ermac. Network traffic is always encrypted using an AES-256-CBC hard-coded key.
The most important addition, however, is the “VNC” module which gives threat actors the ability to interact with the compromised device’s user interface in real time.
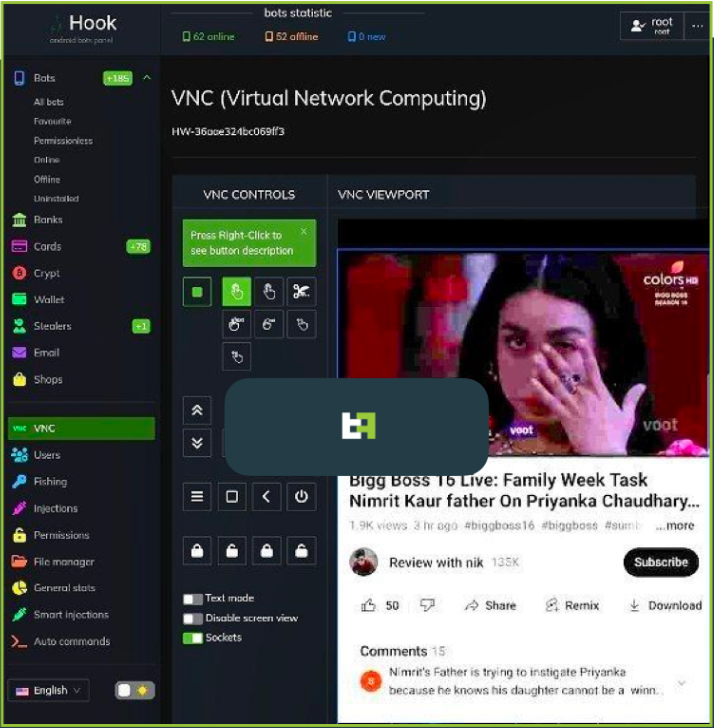
This new system allows Hook operators to perform any action on the device, from exfiltrating PII to monetary transactions.
“With this feature, Hook joins the ranks of malware families capable of performing a full DTO and completing a complete fraud chain, from PII exfiltration to transaction, with all the steps in between, without the need for additional channels”, Warns ThreatFabric.
“This type of transaction is much harder for fraud rating engines to detect and is the biggest selling point for Android bankers.”
The catch is that Hook’s VNC requires Accessibility Service access to work, which can be difficult to obtain on devices running Android 11 or later.
New Hook commands (in addition to Ermac commands) can perform the following actions:
- Start/Stop RAT
- Perform a specific swipe gesture
- Take a screenshot
- Simulate a click on a specific text element
- Simulate a key press (HOME/BACK/RECENTS/LOCK/POWERDIALOG)
- Unlock the device
- Scroll up/down
- Simulate a long press event
- Simulate a click at a specific coordinate
- Set clipboard value to UI element with specific coordinate value
- Simulate a click on a UI element with a specific text value
- Set UI element value to specific text
Besides the above, a “File Manager” command turns the malware into a file manager, allowing hackers to get a list of all files stored on the device and download specific files of their choosing.
Another notable command found by ThreatFabric is for WhatsApp, allowing Hook to log all messages in the popular instant messaging app and even allowing operators to send messages through the victim’s account.
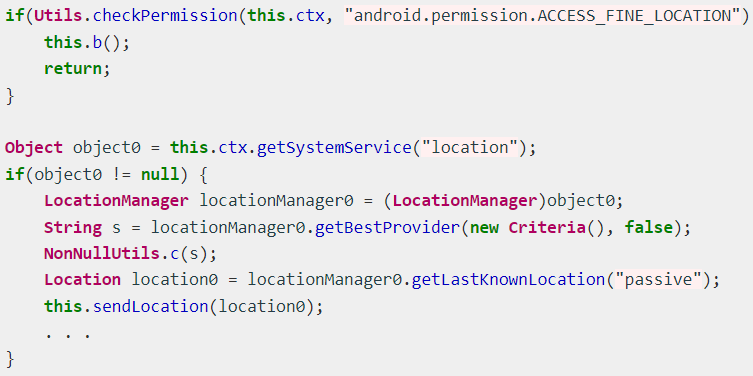
Finally, a new geolocation tracking system allows Hook operators to track the victim’s precise location by abusing the “Access Fine Location” permission.
Global targeting
Hook’s target banking apps are impacting users in the US, Spain, Australia, Poland, Canada, Turkey, UK, France, Italy, and Portugal.
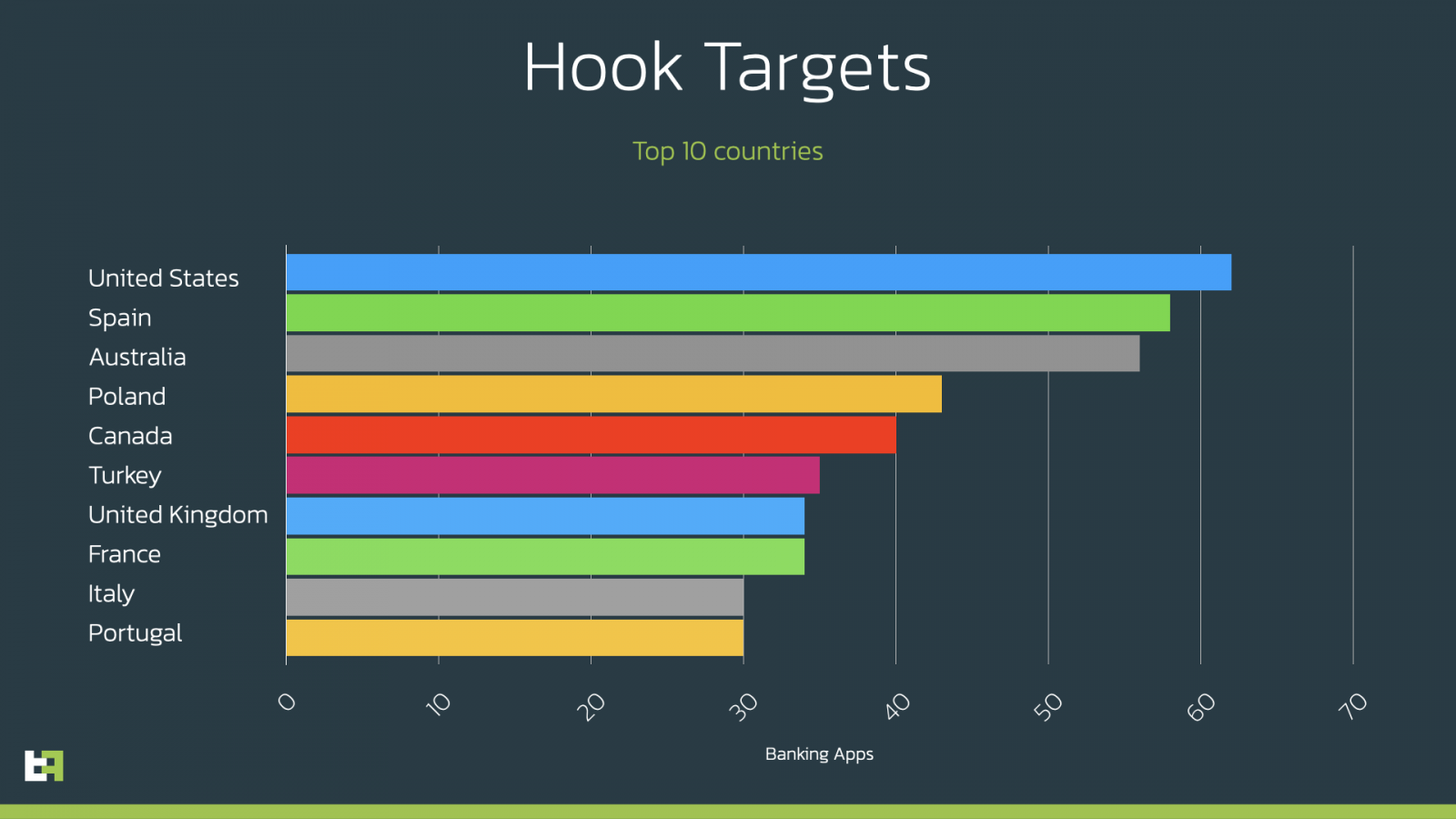
However, it is essential to note that Hook’s broad targeting reach spans the globe. ThreatFabric has listed all application Hook targets in the appendix to the report for those interested.
Currently, Hook is distributed as Google Chrome APK under the package names “com.lojibiwawajinu.guna”, “com.damariwonomiwi.docebi”, “com.damariwonomiwi.docebi” and “com.yecomevusaso .pisifo”, but of course this could change at any time.
To avoid getting infected with Android malware, you should only install apps from the Google Play Store or those provided by your employer.
[ad_2]
Source link
