[ad_1]
NCR suffers an outage on its Aloha POS platform after being hit by a ransomware attack claimed by the BlackCat/ALPHV gang.
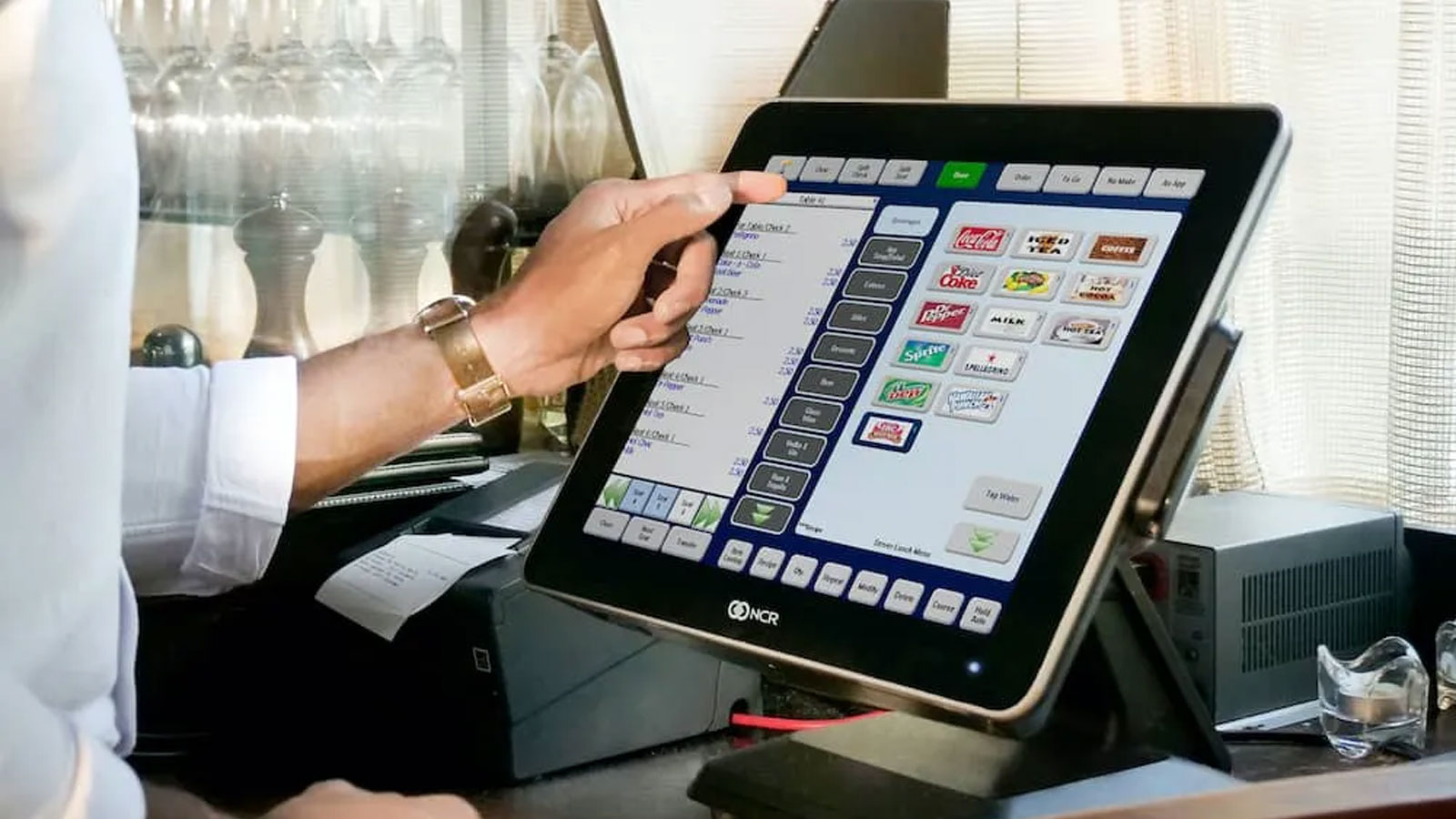
NCR is an American software and technology consulting company that provides digital banking solutions, point of sale system and payment processing solutions for restaurants, businesses and retailers.
One of their products, the Aloha POS platform used in hospitality services, suffered an outage since Wednesday with customers unable to use the system.
After days of silence, NCR revealed today that the outage was caused by a ransomware attack on the data centers used to power their Aloha POS platform.
“As a valued customer of NCR Corporation, we are providing you with additional information on a single data center outage that affects a limited number of ancillary Aloha applications for a subset of our hotel customers,” reads a statement. email sent to Aloha POS customers.
“On April 13, we confirmed that the outage was the result of a ransomware incident.”
“Immediately upon learning of this development, we began contacting customers, engaging third-party cybersecurity experts and launching an investigation.”
“Law enforcement has also been notified.”
In a statement to BleepingComputer, NCR said the outage affects a subset of its hotel Aloha POS customers and only a “limited number of supporting Aloha applications.”
However, Aloha POS customers shared on Reddit that the outage caused significant issues in their business operations.
“Restaurant manager here, small franchise stuck in the Stone Age with about 100 employees. We’re doing the old pen and paper right now and sending it to head office. The whole situation is a huge headache,” said one customer posted on Reddit AlohaPOS.
Other users are concerned about payroll in time for their employees, with various customers recommending that data be manually extracted from data files until the outage is over.
“We have a clear path to recovery and we are executing it. We are working around the clock to restore full service for our customers,” NCR told BleepingComputer. “Additionally, we are providing our customers with dedicated assistance and workarounds to support their operations as we work towards a full recovery.”
Unfortunately, outages caused by cyberattacks like these tend to take a bit of time to resolve securely, as seen with the recent FLAT And western digital cyber attacks.
Do you have any information about this ransomware attack or another? If you would like to share the information, you can contact us securely on Signal at +1 (646) 961-3731, by email at lawrence.abrams@bleepingcomputer.com, or by using our advice form.
BlackCat claims NCR attack
While NCR did not share which ransomware operation was behind its attack, cybersecurity researcher Dominic Alivieri spotted an ephemeral post on the BlackCat/ALPHV ransomware gang’s data leak site where the threat actors claimed responsibility.
This post also included a snippet of the negotiation conversation between an alleged NCR representative and the ransomware gang.
According to his chat, the ransomware gang told NCR that they did not steal any data stored on the servers during the attack.
However, the threat actors claimed to have stolen NCR’s customer credentials and said they would be released if a ransom was not paid.
“We take a lot of credentials from your customers’ networks used to log in to Insight, Pulse, etc. We’ll give you that list after you pay,” the threat actors told NCR.
BlackCat has since removed the NCR post from its data leak site, presumably hoping the company would be willing to negotiate a ransom.
The BlackCat ransomware gang launched its operation in November 2021 with a highly sophisticated cipher that allowed a wide range of attack customization.
The ransomware gang was given the name BlackCat because of an image of a black cat on its data leak site. However, threat actors call themselves ALPHV internally when discussing their operation on hacking forums and during negotiations.
Since its launch, the ransomware operation has become one of the most prominent ransomware today, responsible for hundreds of attacks worldwide, with ransom demands ranging from $35,000 to over $10 million. of dollars.
[ad_2]
Source link
