[ad_1]

Millions of GitHub repositories may be vulnerable to dependency repository hijacking, also known as “RepoJacking”, which could help attackers deploy supply chain attacks affecting large numbers of users.
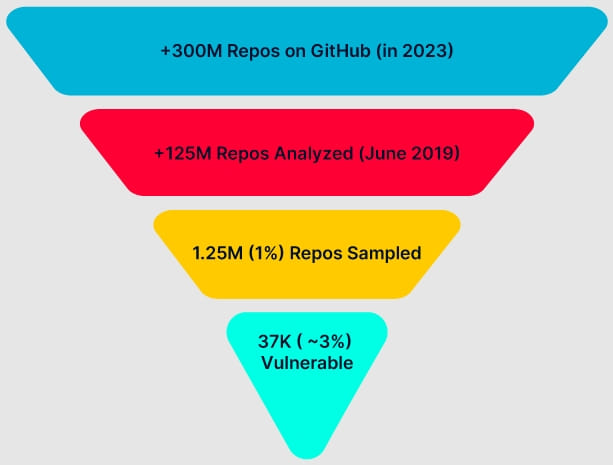
The warning comes from The AquaSec Security Team“Nautilus”, which analyzed a sample of 1.25 million GitHub repositories and found that about 2.95% of them were vulnerable to RepoJacking.
Extrapolating that percentage to GitHub’s entire repository base of over 300 million, the researchers estimate that the issue affects around 9 million projects.
What is Repojacking
Username and repository name changes are common on GitHub, as organizations may gain new direction through acquisition or merger, or they may move to a new brand name.
When this happens, a redirect is created to avoid breaking dependencies of projects using code from repositories that have changed names; however, if someone registers the old name, this redirect becomes invalid.
RepoJacking is an attack where a malicious actor registers a username and creates a repository that was used by an organization in the past but has since changed its name.
This translates to any project or code that relies on the attacked project’s dependencies to retrieve dependencies and code from the attacker-controlled repository, which could contain malware.
GitHub is aware of this possibility and has implemented defenses against RepoJacking attacks. However, AquaSec reports that the solutions so far have been incomplete and easily circumvented.
For example, GitHub only protects very popular projects, but these projects may use a dependency of a less popular and vulnerable repository that is not covered, so the supply chain compromise affects them as well.
Additionally, GitHub protects repositories with over 100 clones the week before it renamed, indicating malicious preparations. This protection does not cover projects that become popular after their name change or transfer of ownership.
Exploitation potential
To highlight the importance of the problem, AquaSec scanned well-known organizations for vulnerable repositories and found exploitable cases in repositories operated by Google and Lyft.
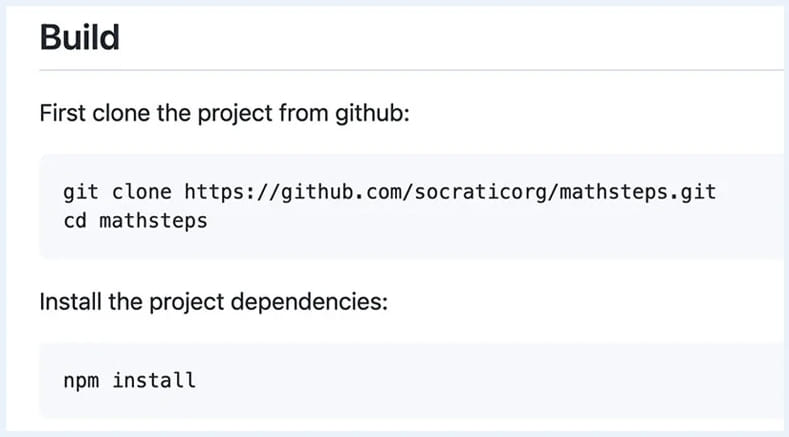
In Google’s case, a readme file with instructions on building the fairly popular “Mathsteps” project pointed to a GitHub repository owned by Socratic, a company Google acquired and assimilated in 2018 that no longer exists.
Since an attacker can clone this repository to break the redirect, users following the readme instructions might have downloaded malicious code from the unauthorized repository.
Additionally, since the instructions included an “npm install” command for the dependency, the attacker’s code would perform arbitrary code execution on the devices of unsuspecting users.
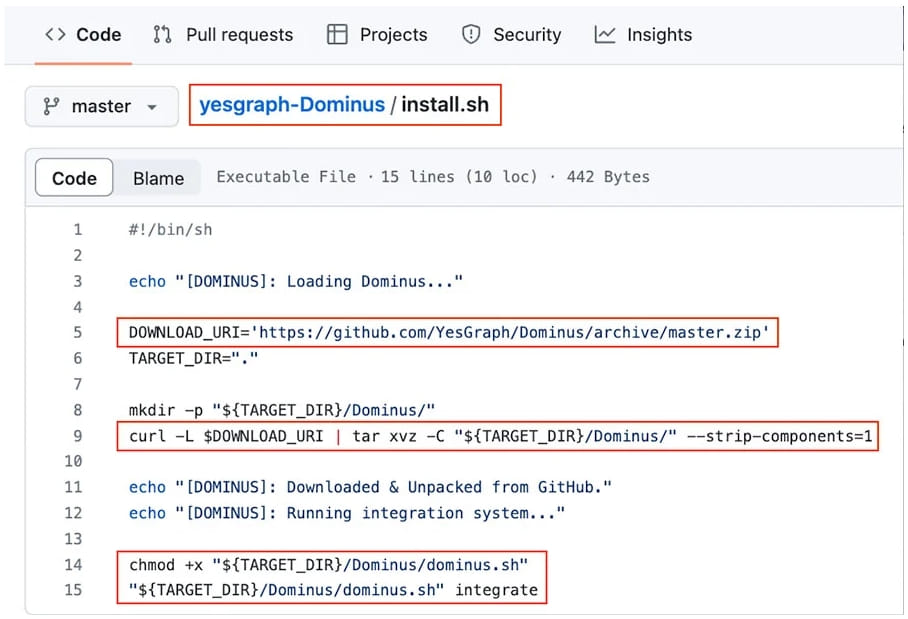
In Lyft’s case, the attack would be more automated, as AquaSec found an installer script on the company’s repository that fetches a ZIP archive from another repository, which is vulnerable to RepoJacking.
An attacker registering a new username and repository with the correct names (“YesGraph” and “Dominus” in this case) could inject their code to anyone running Lyft’s “install.sh” script.
Conclusion
Unfortunately, the risk of RepoJacking is widespread, difficult to mitigate, and can have serious repercussions for organizations and users.
Project owners should minimize the resources they fetch from external repositories as much as possible.
Additionally, owners should consider retaining control of repositories from legacy brands or acquired entities, just to prevent dependency hijacking attacks on themselves and their users.
[ad_2]
Source link
