[ad_1]

Microsoft revoked several Microsoft hardware developer accounts after drivers signed through their profiles were used in cyberattacks, including ransomware incidents.
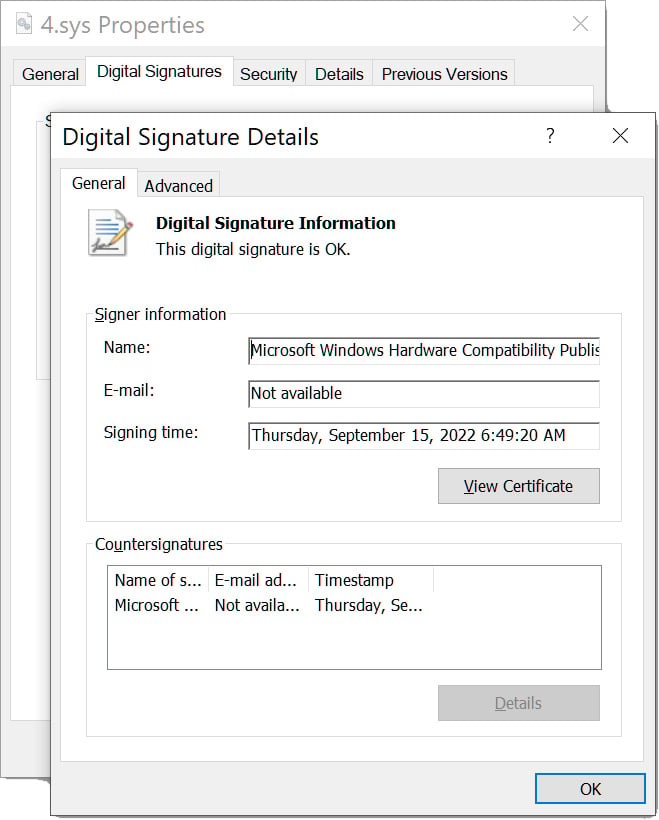
The news comes in a coordinated disclosure between Microsoft, Beggar, Sophosand SentinelOne. The researchers explain that the hackers were using malicious kernel-mode hardware drivers that were trusted with the Authenticode signatures of Microsoft’s Windows Hardware Development Program.
“Microsoft has become aware that drivers certified by Microsoft’s Windows Hardware Development Program are being maliciously used in post-exploitation activities. In these attacks, the attacker had already gained administrator privileges on systems compromised before using the drivers,” Microsoft’s advisory explains. .
“We were made aware of this activity by SentinelOne, Mandiant and Sophos on October 19, 2022, and subsequently conducted an investigation into this activity.”
“This investigation revealed that multiple Microsoft Partner Center developer accounts were engaged in submitting malicious drivers to obtain a Microsoft signature.”
“A new attempt to submit a malicious driver for signature on September 29, 2022 resulted in the suspension of sellers’ accounts in early October.”
Signing Kernel-Mode Drivers
When kernel-mode hardware drivers are loaded in Windows, they get the highest privilege level on the operating system.
These privileges could allow a driver to perform various malicious tasks that are generally not allowed for user-mode applications. Actions include shutting down security software, deleting protected files, and acting on rootkits to hide other processes.
Since Windows 10, Microsoft has required kernel-mode hardware drivers to be signed through Microsoft’s Windows Hardware Developer Program.
Because developers must purchase an Extended Validation (EV) certificate, go through an identification process, and submit Microsoft-approved drivers, many security platforms automatically trust code signed by Microsoft through this program.
For this reason, the ability to have a kernel-mode driver signed by Microsoft for use in malicious campaigns is a valuable commodity.
Source: Mandiant
Toolkit used to terminate security software
In reports published today, researchers explain how they found a new toolkit consisting of two components named STONESTOP (loader) and POORTRY (kernel-mode driver) used in “bring your own vulnerable driver” (BYOVD) attacks. ).
According to Mandiant and SentinelOne, STONESTOP is a user-mode application that attempts to terminate endpoint security software processes on a device. Another variation includes the ability to overwrite and delete files.
Since security software processes are usually protected from tampering by regular applications, STONESTOP loads the Microsoft-signed POORTRY kernel-mode driver to terminate associated protected processes or Windows services.
“STONESTOP works both as a loader/installer for POORTRY, as well as an orchestrator to tell the driver what actions to perform,” the SentinelLabs report explains.
Source: BleepingComputer
Linked to ransomware and SIM card swappers
All three companies have seen the toolkit used by different threat actors.
Sophos’s rapid response team shut down an attack as part of an incident response engagement before hackers could deliver the final payload.
However, Sophos attributed this attack with “high confidence” to the Cuba ransomware operationwho previously used a variant of this malware.
“In incidents investigated by Sophos, malicious actors linked to Cuba ransomware used the BURNTCIGAR loader utility to install a malicious driver signed using Microsoft’s certificate,” Sophos says.
SentinelOne has also seen this Microsoft-signed toolkit used in attacks against telecommunications, BPO, MSSP and financial services companies. In one case, they saw it used by the Hive Ransomware operation against a company in the medical sector.
Notably, SentinelLabs observed a separate threat actor also using a similar Microsoft-signed driver, resulting in the deployment of Hive ransomware against a target in the medical industry, indicating wider use of this technique by various actors with access to similar tools,” the SentinelLabs researchers explained.
Mandiant, on the other hand, saw a malicious actor identified as UNC3944 use the toolkit in attacks as early as August 2022, which is notorious for its SIM swapping attacks.
“Mandiant observed UNC3944 using malware that has been signed through the attestation signing process. UNC3944 is a financially motivated threat group that has been active since at least May 2022 and typically gains initial network access using stolen credentials obtained through SMS phishing operations,” the Mandiant report details.
As many threat clusters use the signed drivers, it’s unclear how they all gained access to similar Microsoft-signed toolkits for use in attacks.
Mandiant and SentinelOne believe the toolkit, or at least the code signing, is from a vendor or service that other threat actors pay to access.
“Further evidence supporting the ‘provider’ theory stems from the similar functionality and design of the pilots. Although they were used by two different threat actors, they operated roughly from the same way. This indicates that they may have been developed by the same person at the time. Later sold for use by someone else.” – SentinelOne.
Mandiant says they could extract the following organization names used to sign driver submissions to Microsoft.
Qi Lijun
Luck Bigger Technology Co., Ltd
XinSing Network Service Co., Ltd
Hangzhou Shunwang Technology Co.,Ltd
Fuzhou Superman
Beijing Hongdao Changxing International Trade Co., Ltd.
Fujian Altron Interactive Entertainment Technology Co., Ltd.
Xiamen Hengxin Excellence Network Technology Co., Ltd.
Dalian Zongmeng Network Technology Co., Ltd.Microsoft’s response
Microsoft has released security updates to revoke certificates used by malicious files and has already suspended accounts used to submit drivers for signing.
New Microsoft Defender signatures (1.377.987.0) have also been released to detect legitimate signed drivers in post-exploit attacks.
“Microsoft is working with Microsoft Active Protections Program (MAPP) partners to help develop additional detections and better protect our joint customers,” Microsoft explained.
“Microsoft Partner Center is also working on long-term solutions to combat these deceptive practices and prevent future impacts on customers.”
However, Microsoft has yet to explain how the malicious drivers passed the review process in the first place.
BleepingComputer contacted Microsoft with further questions about the advisory and review process, but Microsoft said it had nothing further to share.
[ad_2]
Source link
