[ad_1]

The California Department of Finance has been the target of a cyberattack now claimed by the LockBit ransomware gang.
An investigation has been initiated by the California Cybersecurity Integration Center (Cal-CSIC), a group of state and federal agencies dedicated to protecting against cyber threats.
Ongoing investigation
The California Governor’s Office of Emergency Services confirmed that the Treasury Department was affected by a cyber incident, but did not provide too many details.
“The intrusion was proactively identified through coordination with state and federal security partners. Upon identification of this threat, experts in digital security and online threat hunting were rapidly deployed to assess the extent of the intrusion and to assess, contain and mitigate future vulnerabilities” – California Office of Emergency Services
It’s unclear how much damage the hackers caused or how they managed to break into the department. However, the state of California says public funds were not affected by the attack.
LockBit claims 75 GB of stolen files
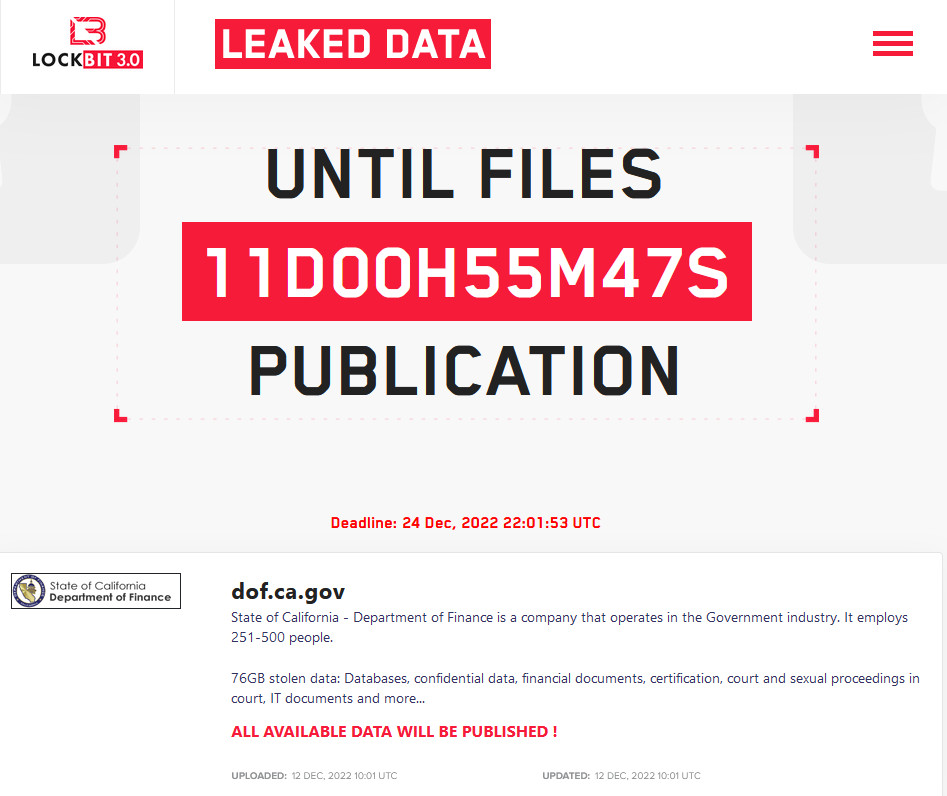
On Monday, the LockBit ransomware gang posted on its leak site that it breached the California State Department of Finance and stole databases, confidential data, financial documents and computer records.
To prove their claim, the hackers posted some screenshots of files they allegedly exfiltrated from California Department of Treasury systems.
The hackers also posted a screenshot of the directories and number of files stored. The properties dialog shows a count of over 246,000 files in over 114,000 folders representing 75.3 GB of data.
LockBit’s data leak site shows a counter to get paid by December 24, threatening to release all files unless they get their ransom.
The builder that generates an encryptor and decryptor for LockBit ransomware was leaked in September by a disgruntled operator.
A week later, a new group calling itself Bloody Ransomware Gang started using it in attacks against a Ukrainian entity.
In October, a 33-year-old Russian national suspected of being linked to the LockBit ransomware gang was arrested in Ontario, Canada. He reportedly deployed the ransomware on critical infrastructure and large industrial organizations.
At the time, Europol said the individual was a “high-value target due to his involvement in numerous high-profile ransomware cases”, demanding between €5 million and €70 million from victims.
LockBit operators typically focus on extorting large corporations and are among the most active in the big-money ransomware scene.
Among the victims of LockBit this year are the automotive giant Continentalsecurity company Entrustand the Italian Internal Revenue Service (The Agenzia delle Entrate).
The gang is financially motivated and is the first to introduce a bug bounty programoffering rewards of up to $1 million for vulnerabilities in their websites, locker, and new ideas to grow their business.
[ad_2]
Source link
