[ad_1]

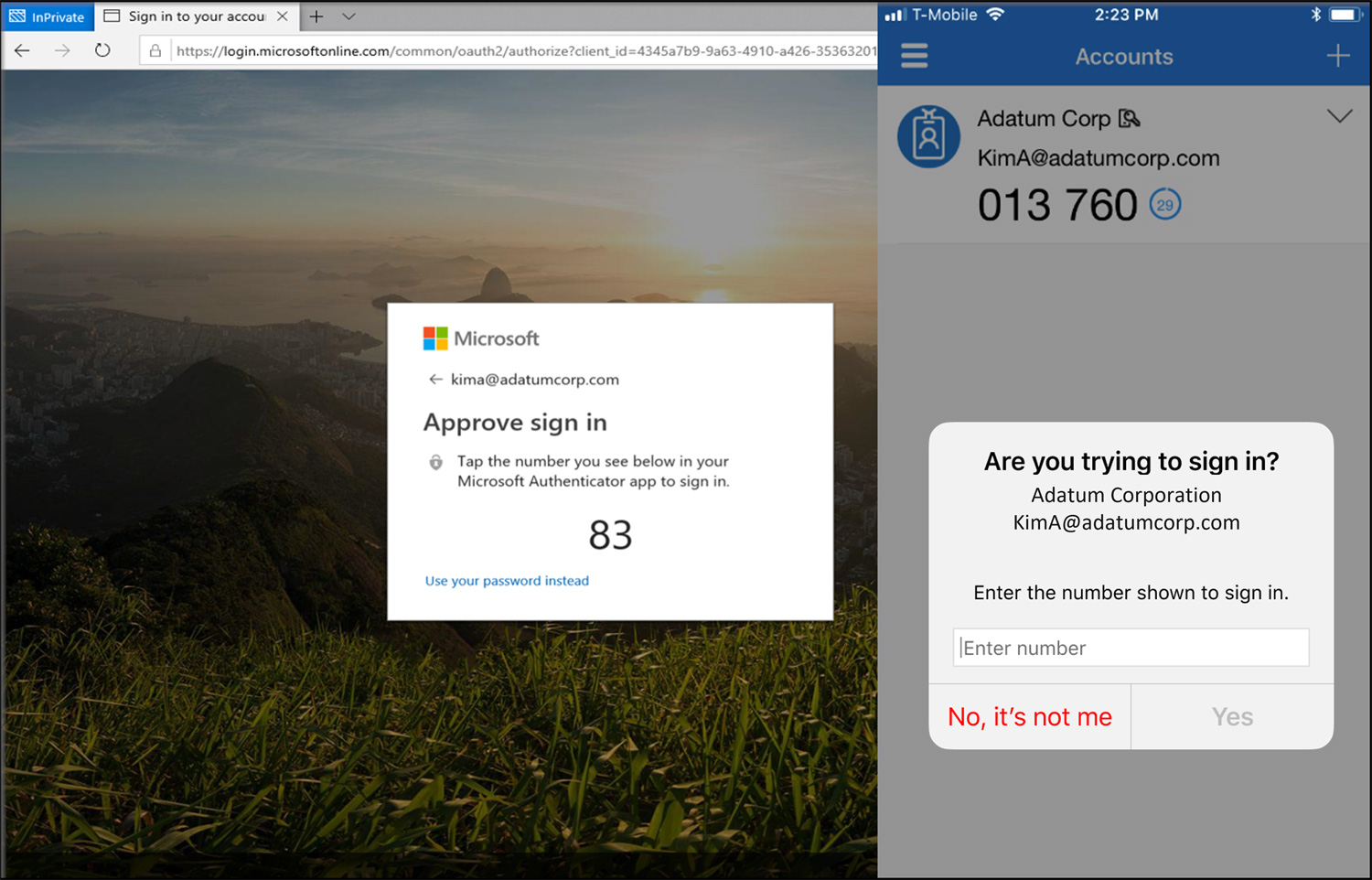
Microsoft has started enforcing number matching in Microsoft Authenticator push notifications to ward off Multi-Factor Authentication (MFA) fatigue attacks.
In such attacks (also known as push bombing or push spam MFA), cybercriminals flood targets with mobile push notifications asking them to approve attempts to log into their corporate accounts using stolen credentials. .
In many cases, targets will give in to repeated malicious MFA push requests, either by mistake or to stop the seemingly endless stream of alerts, allowing attackers to log into their accounts.
This type of social engineering attack has already been proven to be very effective by threat actors Lapsus$ and Yanluowang who have used this attack method to breach high-profile organizations including Microsoft, CiscoAnd Uber.
However, as previously announcedMicrosoft will begin enforcing number matching for MFA Microsoft Authenticator alerts to block MFA fatigue attack attempts among tenants starting today.
“Number Matching is a key security upgrade from traditional second-factor notifications in Microsoft Authenticator. We will be removing admin controls and enforcing the tenant-wide number matching experience for all users on Microsoft Authenticator push notifications from May 8, 2023”, Microsoft said.
“Affected services will begin rolling out these changes after May 8, 2023, and users will begin to see number matches in approval requests. As services roll out, some may see number matches, d ‘others don’t.’
To manually enable number matching before Microsoft removes admin controls, you need to go to Security > Authentication Methods > Microsoft Authenticator in the Azure portal.
From there, follow these steps:
- On the Activate and target tab, click Yes And All the users to enable the policy for everyone or add selected users and groups. Put it on Authentication mode for these users/groups Any Or Push.
- On the Configure tab, for Require number matching for push notificationschange Status For Enabledchoose people to include or exclude from number matching, then click To safeguard.
You can also enable number matching for all users or a single group using Graphics APIs (detailed information is available here).
“If the user has a different default authentication method, there will be no change in their default login,” Microsoft says.
“If the default method is Microsoft Authenticator and the user is specified in one of the following policies, they will begin receiving number matching approval after May 8, 2023.”
Those who want to add an extra line of defense against MFA fatigue attacks can also limit the number of MFA authentication requests per user (Microsoft, DUO, Okta) and lock accounts or alert the security team/domain administrator when these thresholds are exceeded.
[ad_2]
Source link
