[ad_1]

Microsoft announced that built-in protection is generally available for all devices integrated with Defender for Endpoint, the company’s endpoint security platform.
When applied, this set of default settings provides better protection for enterprise endpoints against advanced and emerging threats, including ransomware attacks.
“Initially, built-in protection will include enabling tamper protection for your tenant, with more default settings to come,” Microsoft Explain.
Until Redmond rolls out more default protection settings through built-in protection, admins can enable cloud
This announcement comes after the company began enabling tamper protection for all new customers with Defender for Endpoint Plan 2 or Microsoft 365 E5 licenses starting last year.
In September, Redmond added that he would soon be enable tamper protection by default on all Microsoft Defender for Endpoint (MDE) embedded systems, locking down Microsoft Defender Antivirus to secure defaults and preventing any changes to security settings.
“To further protect our customers, we are announcing that Tamper Protection will be enabled for all existing customers unless it has been explicitly disabled in the Microsoft 365 Defender Portal,” said Josh Bregman, Product Manager principal at Microsoft, at the time.
This is achieved by preventing other applications from modifying the settings of real-time and cloud protection, behavior monitoring and Defender components like IOfficeAntivirus (IOAV) which handles the detection of suspicious files downloaded from the Internet.
Deployment to a tenant near you
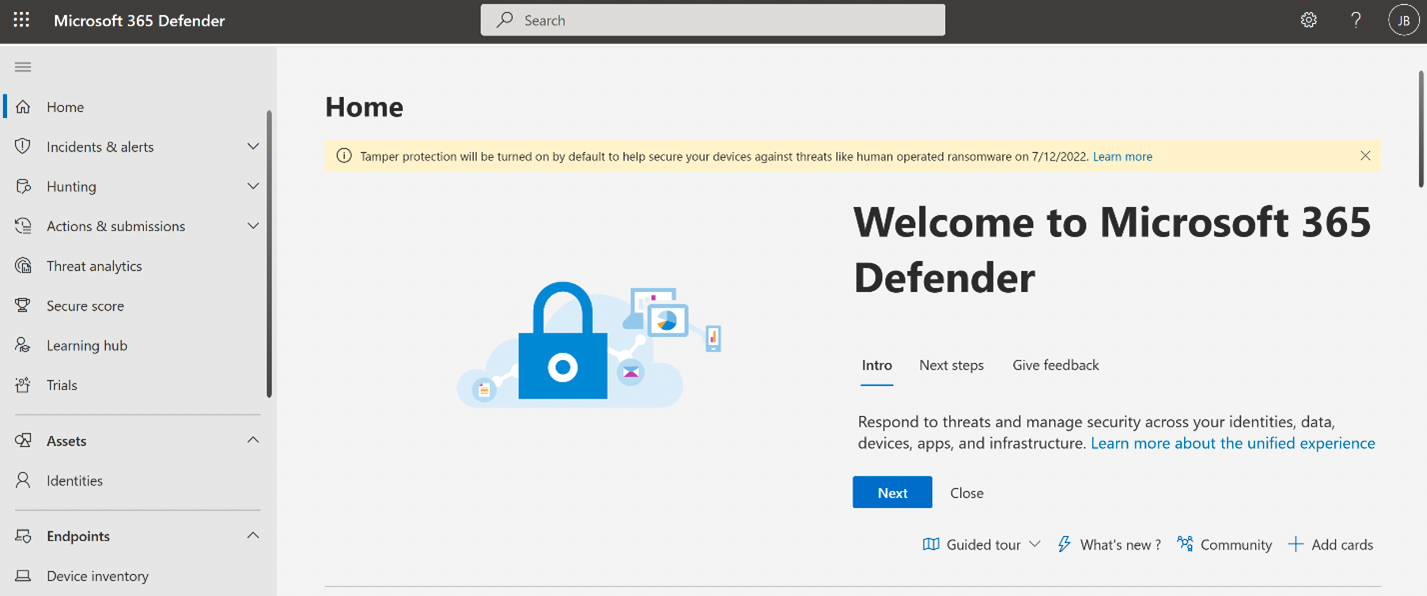
Customers who have not yet configured tamper protection in their enterprise environments will soon receive notifications from the Microsoft 365 Defender Portal notifying them that the feature will be enabled.
“Tamper protection will be enabled for your tenant and will be applied to Windows devices in your organization,” Microsoft said on its support portal.
“Whenever new devices are onboarded to Defender for Endpoint, the built-in protection settings will be applied to all new devices running Windows.”
However, administrators can also change their built-in protection settings or choose to opt out:
- Go to the Microsoft 365 Defender Portal and log in.
- Go to Settings > Endpoints > Advanced features.
- Adjust Self-protection at On (if not already selected), then select Save preferences (do not leave this page yet)
- Adjust Self-protection at Stoppedthen select Save preferences.
Microsoft 365 admins can also exclude certain network devices from tamper protection if there are app compatibility issues by Using security management for Defender for Endpoint Where creating a profile in Microsoft Endpoint Manager.
Redmond also started deploying built-in protection in Defender for Office 365 to tenants worldwide in November 2021 to provide the same level of protection against phishing emails to existing and new end users.
[ad_2]
Source link
